Roaming Windows User Profiles: Difference between revisions
Mmuehlfeld (talk | contribs) m (Mmuehlfeld moved page Samba & Windows Profiles to Implementing roaming profiles: Rename page for better wiki structure) |
mNo edit summary |
||
| (30 intermediate revisions by 2 users not shown) | |||
| Line 1: | Line 1: | ||
= Introduction = |
|||
= Creating a profiles share and setting permissions= |
|||
A Windows profile is a set of files that contains all settings of a user including per-user configuration files and registry settings. In an Active Directory or NT4 domain you can set that the profile of a user is stored on a server. This enables the user to log on to different Windows domain members and use the same settings. |
|||
The following sections describe how to setup a profile share stored on a Samba server. |
|||
When using roaming user profiles, a copy of the profile is downloaded from the server to the Windows domain member when a user logs into. Until the user logs out, all settings are stored and updated in the local copy. During the log out, the profile is uploaded to the server. |
|||
There are different ways to setup the share, depending on using Windows ACLs (recommended) or POSIX ACLs: |
|||
| Line 9: | Line 9: | ||
= Windows Roaming Profile Versions = |
|||
== Profile share using Windows ACLs == |
|||
Depending on the operating system version, Windows uses separate profile folders for a user to support Windows version-specific features. Version 2 profiles and later append the <code>.V*</code> suffix to the user's profile folder. |
|||
* [[Shares_with_Windows_ACLs#Preparatory_work|Preparatory work]] |
|||
The following Windows profile versions exist: |
|||
* Create a folder for the roaming profiles, Note: These commands must be run by the 'root' user or with 'sudo' |
|||
# mkdir -p /srv/samba/Profiles/ |
|||
:{| class="wikitable" |
|||
* Add a new share to your smb.conf: |
|||
!Windows Client OS Version |
|||
[profiles] |
|||
!Windows Server OS Version |
|||
path = /srv/samba/Profiles/ |
|||
!Profile Suffix |
|||
read only = no |
|||
!Example Profile Folder Name |
|||
|- |
|||
|Windows NT 4.0 - Windows Vista |
|||
|Windows NT Server 4.0 - Windows Server 2008 |
|||
|''none'' |
|||
|user |
|||
|- |
|||
|Windows 7 |
|||
|Windows Server 2008 R2 |
|||
|V2 |
|||
|user.V2 |
|||
|- |
|||
|Windows 8.0 - 8.1* |
|||
|Windows Server 2012 - 2012 R2* |
|||
|V3 |
|||
|user.V3 |
|||
|- |
|||
|Windows 8.1* |
|||
|Windows Server 2012 R2* |
|||
|V4 |
|||
|user.V4 |
|||
|- |
|||
|Windows 10 (1507 to 1511) |
|||
|Windows Server 2016 |
|||
|V5 |
|||
|user.V5 |
|||
|- |
|||
|Windows 10 (1607 and later) |
|||
| |
|||
|V6 |
|||
|user.V6 |
|||
|} |
|||
: <nowiki>*</nowiki> Using the default settings, Windows 8.1 and Windows Server 2012 R2 use V3 profiles. However, the profiles are incompatible with Windows 8.0 and Windows Server 2012. For this reason it is recommended that you configure Windows 8.1 and Windows Server 2012 R2 to use V4 profiles. For further details, see: [https://support.microsoft.com/en-us/help/2890783/incompatibility-between-windows-8.1-roaming-user-profiles-and-those-in-earlier-versions-of-windows Incompatibility between Windows 8.1 roaming user profiles and those in earlier versions of Windows]. |
|||
* Reload Samba: |
|||
# smbcontrol all reload-config |
|||
When you set the profile path for a user, you always set the path without any version suffix. For example: |
|||
* Log on to a Windows machine as Domain Administrator |
|||
\\server\profiles\user_name |
|||
* Go to „\\Servername“. You'll see the newly added share. |
|||
:[[Image:Shares_view.png]] |
|||
* Right-click the share name, choose „Properties“ and go to the „Security“ tab. |
|||
* Click „Advanced“ and then the „Change permissions“ button for a more granular way to edit the share permissions. |
|||
= Setting up the Share on the Samba File Server = |
|||
:[[Image:Advanced_share_settings.png]] |
|||
== Using Windows ACLs == |
|||
* Set the permissions as shown in the following table |
|||
To create a share, for example, <code>profiles</code> for hosting the roaming profiles on a Samba file server: |
|||
:{| border="1" |
|||
!Name |
|||
* Create a new share using these lines. |
|||
!Permissions |
|||
!Apply to |
|||
[profiles] |
|||
|- |
|||
comment = Users profiles |
|||
|Administrator |
|||
path = /srv/samba/profiles/ |
|||
|Full control |
|||
;browseable = No |
|||
|This folder, subfolders and files |
|||
read only = No |
|||
csc policy = disable |
|||
vfs objects = acl_xattr |
|||
As 'root': |
|||
mkdir -p /srv/samba/profiles |
|||
chown root:"Domain Admins" /srv/samba/profiles |
|||
chmod 0770 /srv/samba/profiles |
|||
{{Imbox |
|||
| type = note |
|||
| text = If you are using the 'ad' idmap backend, then you should not give the 'Domain Admins' group a gidNumber attribute, it will break Sysvol, in which case you should create a new group, make this group a member of 'Domain Admins' and give the new group a gidNumber. Now use the new group name instead of 'Domain Admins' . |
|||
}} |
|||
{{Imbox |
|||
| type = note |
|||
| text = In the share above, <code>browseable = No</code> is commented out, this is done so that you can see the <code>profiles</code> share in RSAT to set the initial permissions. Once the permissions are set, you should uncomment the line (remove the ';'). |
|||
}} |
|||
Set the following permissions: |
|||
:* Share tab permissions: |
|||
::{| class="wikitable" |
|||
!Principal |
|||
!Allow |
|||
|- |
|- |
||
|Everyone |
|||
|Domain Users |
|||
|Full Control / Change / Read |
|||
|Traverse folder/execute file, List folder/read data, Create folder/append data |
|||
|} |
|||
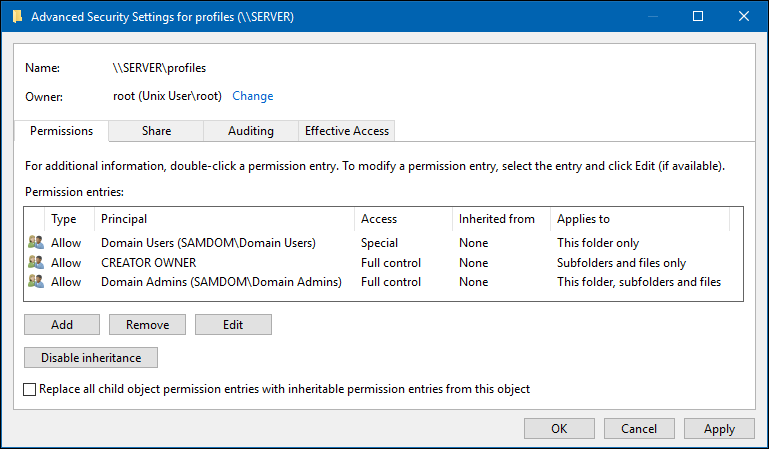
:* Security tab file system permissions on the root of the <code>profiles</code> share: |
|||
::{| class="wikitable" |
|||
!Principal |
|||
!Access |
|||
!Applies to |
|||
|- style="vertical-align:top;" |
|||
|Domain Users * |
|||
|Traverse folder / execute file<br />List folder / read data<br />Create folder / append data |
|||
|This folder only |
|This folder only |
||
|- |
|- |
||
| Line 54: | Line 122: | ||
|Full control |
|Full control |
||
|Subfolders and files only |
|Subfolders and files only |
||
|- |
|||
|Domain Admins |
|||
|Full control |
|||
|This folder, subfolders and files |
|||
|- |
|||
|SYSTEM ** |
|||
|Full control |
|||
|This folder, subfolders and files |
|||
|} |
|} |
||
::<nowiki>*</nowiki> You can alternatively set other groups, to enable the group members to store their user profile on the share. When using different groups, apply the permissions as displayed for <code>Domain Users</code> in the previous example. |
|||
::<nowiki>**</nowiki> For details, see [[The SYSTEM Account]]. |
|||
:[[Image:Profile_share_permissions_for_group.png]] |
|||
:: Verify that permission inheritance is disabled on the root of the share. If any permission entry in the <code>Advanced Security Settings</code> window displays a path in the <code>Inherited from</code> column, click the <code>Disable inheritance</code> button. On Windows 7, unselect the <code>Include inheritable permissions from this object's parent</code> check box to set the same setting. |
|||
:You can replace "Domain Users" with another group name, if you want to use that group to store profiles on the share. You can add multiple groups, just use the same recommended group permissions for "Domain Users". |
|||
::[[Image:Profiles_Folder_File_System_ACLs.png]] |
|||
* Save the new permissions by closing the windows with „OK“. |
|||
These settings enable members of the <code>Domain Users</code> group to store their roaming profiles on the share, without being able to access other user's profiles. Members of the <code>Domain Admins</code> group are able to access all directories on the share. |
|||
== Using POSIX ACLs on a Unix domain member == |
|||
On a Unix domain member server, you can set up the <code>profiles</code> share using POSIX ACLs instead of using Windows access control lists (ACL). This will not work on a Samba Active Directory Controller. |
|||
== Profile share with using POSIX ACLs == |
|||
* Create a folder for the roaming profiles and set permissions |
|||
# mkdir -p /srv/samba/Profiles/ |
|||
# chmod 1770 /srv/samba/profiles |
|||
# chgrp „Domain Users“ /srv/samba/profiles |
|||
{{Imbox |
|||
* Add a new share to your smb.conf: |
|||
| type = note |
|||
[Profiles] |
|||
| text = Whilst it is possible to use POSIX ACLs for the profiles share on an Unix domain member, it is recommended that you set up the permissions from Windows. To do this, see [[#Using_Windows_ACLs|Setting up the Profiles Share on the Samba File Server - Using Windows ACLs]]. |
|||
path = /srv/samba/Profiles/ |
|||
}} |
|||
read only = no |
|||
store dos attributes = Yes |
|||
create mask = 0600 |
|||
directory mask = 0700 |
|||
{{Imbox |
|||
profile acls = yes |
|||
| type = warning |
|||
csc policy = disable |
|||
| text = When setting up the share on a Samba Active Directory (AD) domain controller (DC), you cannot use POSIX ACLs. On an Samba DC, only shares using extended ACLs are supported. For further details, see [[Setting_up_a_Share_Using_Windows_ACLs#Enable_Extended_ACL_Support_in_the_smb.conf_File|Enable Extended ACL Support in the smb.conf File]]. To set up the share on a Samba AD DC, see [[#Using_Windows_ACLs|Setting up the Profiles Share on the Samba File Server - Using Windows ACLs]]. |
|||
}} |
|||
* Add the following share configuration section to your <code>smb.conf</code> file: |
|||
[profiles] |
|||
comment = Users profiles |
|||
path = /srv/samba/profiles/ |
|||
browseable = No |
|||
read only = No |
|||
force create mode = 0600 |
|||
force directory mode = 0700 |
|||
csc policy = disable |
|||
store dos attributes = yes |
|||
vfs objects = acl_xattr |
|||
: For details about the parameters used, see the descriptions in the <code>smb.conf(5)</code> man page. |
|||
* Create the directory and set permissions: |
|||
# mkdir -p /srv/samba/profiles/ |
|||
# chgrp -R "Domain Users" /srv/samba/profiles/ |
|||
# chmod 1750 /srv/samba/profiles/ |
|||
: These settings enable members of the <code>Domain Users</code> group to store their roaming profiles on the share, without being able to access other user's profiles. Alternatively, you can set a different group. |
|||
* Reload Samba: |
* Reload Samba: |
||
# smbcontrol all reload-config |
# smbcontrol all reload-config |
||
| Line 88: | Line 190: | ||
= |
= Assigning a Roaming Profile to a User = |
||
Depending on the Windows version, Windows uses different folders to store the roaming profile of a user. However, when you set the profile path for a user, you always set the path to the folder without any version suffix. For example: |
|||
== In an AD environment == |
|||
\\server\profiles\user_name |
|||
For further details, see [[#The_Windows_Roaming_Profile_Versions|The Windows Roaming Profile Versions]]. |
|||
In an AD environment, you can setup individual roaming profiles for every user. |
|||
Note that you must not set a trailing backslash. |
|||
* Open ADUC. |
|||
* Right-click to an user account and choose „Properties“. |
|||
* Go to the „Profile“ tab, and fill the path to the users profile. |
|||
== In an Active Directory == |
|||
:[[Image:ADUC_profile_share.png]] |
|||
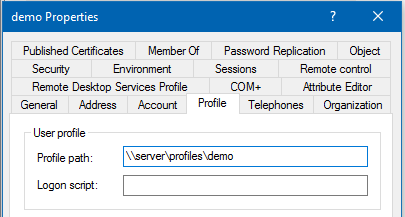
=== Using <code>Active Directory Users and Computers</code> === |
|||
:If you use the %USERNAME% variable, you can set the profile path to multiple accounts at once, too. |
|||
In an Active Directory, you can use the <code>Active Directory Users and Computers</code> Windows application to set the path to the user's profile folder. If you do not have the Remote Server Administration Tools (RSAT) installed, see [[Installing RSAT|Installing RSAT]]. |
|||
:Windows Vista up to Windows 8.0 create .V2 folders for their profiles. Windows 8.1 starts using .V4 folders and Windows 10 .V5. This is appended automatically if a profile from those systems is uploaded to the server. |
|||
To assign <code>\\server\profiles\demo</code> as profile folder to the <code>demo</code> account: |
|||
* Log in to a computer using an account that is enabled to edit user accounts. |
|||
* Open the <code>Active Directory Users and Computers</code> application. |
|||
=== In a NT4 domain === |
|||
* Navigate to the directory container that contains the <code>demo</code> account. |
|||
In a NT4 environment, you can setup roaming profiles globally for all users on the Samba PDC. |
|||
* Right-click to the <code>demo</code> user account and select <code>Properties</code>. |
|||
* Add the following directive to your smb.conf: |
|||
* Select the <code>Profile</code> tab. |
|||
logon path = \\%L\Profiles\%U |
|||
* Fill the path to the home folder into the <code>Profile path</code> field. |
|||
:The logon path directive is where you actually set up roaming profiles. This directive should contain a Windows network path to the location of the profile for each user. If the users profile directory does not exist, it will be created on that location (as long as the user has write access to that directory). |
|||
: Set the path always without any profile version suffix and without trailing backslash. For details, see [[#The_Windows_Roaming_Profile_Versions|The Windows Roaming Profile Versions]]. |
|||
:[[Image:ADUC_Set_Profile_Folder.png]]. |
|||
:You can also take full advantage of Samba's variable substitutions (see „man smb.conf“ in the „variable substitutions“ section). |
|||
* Click <code>OK</code>. |
|||
* Reload Samba: |
|||
# smbcontrol all reload-config |
|||
The setting is applied the next time the user logs in. |
|||
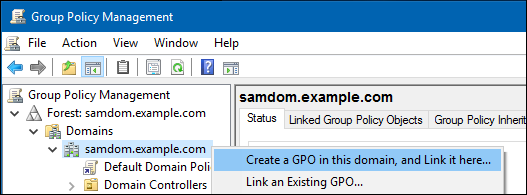
=== Using a Group Policy Object === |
|||
Using group policy objects (GPO), you can assign settings to organizational units (OU) or to a domain. This enables you, for example, to automatically assign profile paths to all users that log on to a computer that is a member of the OU or domain. If you move the computer to a different OU or domain, the setting is removed or updated. Using this way, you do not have to assign manually the settings to each user account. |
|||
{{Imbox |
|||
| type = note |
|||
| text = Windows only supports assigning a profile path using GPOs on a per-computer basis. This means that the path is also applied to local users on domain members, which have no access to the profile share. To set the profile path on a per-user basis, see [[#Using_Active_Directory_Users_and_Computers|Using Active Directory Users and Computers]]. |
|||
}} |
|||
To create a group policy object (GPO) for the domain that automatically assigns the <code>\\server\path\''user_name''</code> path to every user that logs on to a Windows domain member: |
|||
* Log in to a computer using an account that is allowed to edit group policies, such as the AD domain <code>Administrator</code> account. |
|||
* Open the <code>Group Policy Management Console</code>. If you are not having the Remote Server Administration Tools (RSAT) installed on this computer, see [[Installing RSAT|Installing RSAT]]. |
|||
* Right-click to your AD domain and select <code>Create a GPO in this domain, and Link it here</code>. |
|||
:[[Image:GPMC_Create_GPO.png]] |
|||
* Enter a name for the GPO, such as <code>Profiles on ''server''</code>. The new GPO is shown below the domain entry. |
|||
* Right-click to the newly-created GPO and select <code>Edit</code> to open the <code>Group Policy Management Editor</code>. |
|||
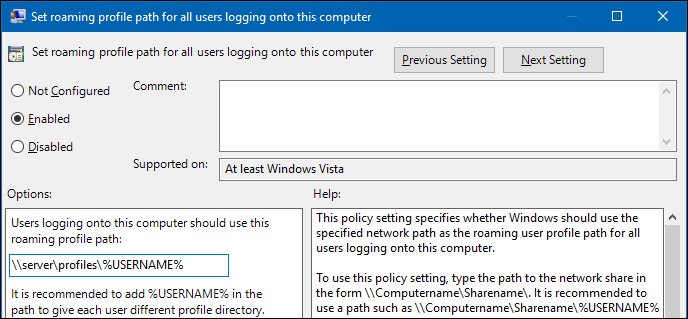
* Navigate to the <code>Computer Configuration</code> → <code>Policies</code> → <code>Administrative Templates</code> → <code>System</code> → <code>User Profiles</code> entry. |
|||
* Double-click the <code>Set roaming profile path for all users logging onto this computer</code> policy to edit: |
|||
:* Enable the policy and set the profile path. For example: |
|||
\\server\profiles\%USERNAME% |
|||
:: Windows replaces the <code>%USERNAME%</code> variable with the user name during login. Set the path without trailing backslash. |
|||
::[[Image:GPME_Set_Profiles_Properties.png]] |
|||
:* Click <code>OK</code>. |
|||
* Close the <code>Group Policy Management Editor</code>. The GPOs are automatically saved on the <code>Sysvol</code> share on the domain controller (DC). |
|||
* Close the <code>Group Policy Management Console</code>. |
|||
The GPO is applied at the next reboot of the Windows domain members or when they reload the group policies. |
|||
=== Using <code>ldbedit</code> on a Domain Controller === |
|||
On a domain controller (DC), to assign, for example, the <code>\\server\profiles\demo\</code> path as profile folder to the <code>demo</code> account: |
|||
* Edit the <code>demo</code> user account: |
|||
# ldbedit -H /usr/local/samba/private/sam.ldb 'sAMAccountName=demo' |
|||
* The accounts attributes are displayed in an editor. Append the following attribute and value to the end of the list: |
|||
profilePath: \\server\profiles\demo |
|||
: You must not set a trailing backslash to the path. |
|||
* Save the changes. |
|||
The setting is applied the next time the user logs in. |
|||
== In an NT4 Domain == |
|||
In an Samba NT4 domain, to set <code>\\server\profiles\%U</code> as path to the profile folder: |
|||
* Add the following parameter to the <code>[global]</code> section in your <code>smb.conf</code> file: |
|||
logon path = \\%L\Profiles\%U |
|||
: During logging in to the domain member, Samba automatically replaces the <code>%U</code> variable with the session user name. For further details, see the <code>Variable Substitutions</code> section in the <code>smb.conf(5)</code> man page. |
|||
* Reload Samba: |
|||
# smbcontrol all reload-config |
|||
= Troubleshooting roaming profiles = |
|||
The registry contains information about each user's profile and should your Samba infrastructure change, like the network location of users profiles, Windows might be unable to find it. The list of user profiles is located at: |
|||
= Configuring Windows Profile Folder Redirections = |
|||
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsNT\CurrentVersion\ProfileList |
|||
See [[Configuring Windows Profile Folder Redirections]]. |
|||
Deleting the correct subkey (user SID) will force Windows to look up the user's profile setting from the domain controller and restore the profile when the next login happens. |
|||
Latest revision as of 12:20, 30 November 2023
Introduction
A Windows profile is a set of files that contains all settings of a user including per-user configuration files and registry settings. In an Active Directory or NT4 domain you can set that the profile of a user is stored on a server. This enables the user to log on to different Windows domain members and use the same settings.
When using roaming user profiles, a copy of the profile is downloaded from the server to the Windows domain member when a user logs into. Until the user logs out, all settings are stored and updated in the local copy. During the log out, the profile is uploaded to the server.
Windows Roaming Profile Versions
Depending on the operating system version, Windows uses separate profile folders for a user to support Windows version-specific features. Version 2 profiles and later append the .V* suffix to the user's profile folder.
The following Windows profile versions exist:
Windows Client OS Version Windows Server OS Version Profile Suffix Example Profile Folder Name Windows NT 4.0 - Windows Vista Windows NT Server 4.0 - Windows Server 2008 none user Windows 7 Windows Server 2008 R2 V2 user.V2 Windows 8.0 - 8.1* Windows Server 2012 - 2012 R2* V3 user.V3 Windows 8.1* Windows Server 2012 R2* V4 user.V4 Windows 10 (1507 to 1511) Windows Server 2016 V5 user.V5 Windows 10 (1607 and later) V6 user.V6
- * Using the default settings, Windows 8.1 and Windows Server 2012 R2 use V3 profiles. However, the profiles are incompatible with Windows 8.0 and Windows Server 2012. For this reason it is recommended that you configure Windows 8.1 and Windows Server 2012 R2 to use V4 profiles. For further details, see: Incompatibility between Windows 8.1 roaming user profiles and those in earlier versions of Windows.
When you set the profile path for a user, you always set the path without any version suffix. For example:
\\server\profiles\user_name
Using Windows ACLs
To create a share, for example, profiles for hosting the roaming profiles on a Samba file server:
- Create a new share using these lines.
[profiles]
comment = Users profiles
path = /srv/samba/profiles/
;browseable = No
read only = No
csc policy = disable
vfs objects = acl_xattr
As 'root':
mkdir -p /srv/samba/profiles chown root:"Domain Admins" /srv/samba/profiles chmod 0770 /srv/samba/profiles
| If you are using the 'ad' idmap backend, then you should not give the 'Domain Admins' group a gidNumber attribute, it will break Sysvol, in which case you should create a new group, make this group a member of 'Domain Admins' and give the new group a gidNumber. Now use the new group name instead of 'Domain Admins' . |
In the share above, browseable = No is commented out, this is done so that you can see the profiles share in RSAT to set the initial permissions. Once the permissions are set, you should uncomment the line (remove the ';'). |
Set the following permissions:
- Share tab permissions:
Principal Allow Everyone Full Control / Change / Read
- Security tab file system permissions on the root of the
profilesshare:
- Security tab file system permissions on the root of the
Principal Access Applies to Domain Users * Traverse folder / execute file
List folder / read data
Create folder / append dataThis folder only CREATOR OWNER Full control Subfolders and files only Domain Admins Full control This folder, subfolders and files SYSTEM ** Full control This folder, subfolders and files
- * You can alternatively set other groups, to enable the group members to store their user profile on the share. When using different groups, apply the permissions as displayed for
Domain Usersin the previous example.
- * You can alternatively set other groups, to enable the group members to store their user profile on the share. When using different groups, apply the permissions as displayed for
- ** For details, see The SYSTEM Account.
- Verify that permission inheritance is disabled on the root of the share. If any permission entry in the
Advanced Security Settingswindow displays a path in theInherited fromcolumn, click theDisable inheritancebutton. On Windows 7, unselect theInclude inheritable permissions from this object's parentcheck box to set the same setting.
- Verify that permission inheritance is disabled on the root of the share. If any permission entry in the
These settings enable members of the Domain Users group to store their roaming profiles on the share, without being able to access other user's profiles. Members of the Domain Admins group are able to access all directories on the share.
Using POSIX ACLs on a Unix domain member
On a Unix domain member server, you can set up the profiles share using POSIX ACLs instead of using Windows access control lists (ACL). This will not work on a Samba Active Directory Controller.
| Whilst it is possible to use POSIX ACLs for the profiles share on an Unix domain member, it is recommended that you set up the permissions from Windows. To do this, see Setting up the Profiles Share on the Samba File Server - Using Windows ACLs. |
| When setting up the share on a Samba Active Directory (AD) domain controller (DC), you cannot use POSIX ACLs. On an Samba DC, only shares using extended ACLs are supported. For further details, see Enable Extended ACL Support in the smb.conf File. To set up the share on a Samba AD DC, see Setting up the Profiles Share on the Samba File Server - Using Windows ACLs. |
- Add the following share configuration section to your
smb.conffile:
[profiles]
comment = Users profiles
path = /srv/samba/profiles/
browseable = No
read only = No
force create mode = 0600
force directory mode = 0700
csc policy = disable
store dos attributes = yes
vfs objects = acl_xattr
- For details about the parameters used, see the descriptions in the
smb.conf(5)man page.
- Create the directory and set permissions:
# mkdir -p /srv/samba/profiles/ # chgrp -R "Domain Users" /srv/samba/profiles/ # chmod 1750 /srv/samba/profiles/
- These settings enable members of the
Domain Usersgroup to store their roaming profiles on the share, without being able to access other user's profiles. Alternatively, you can set a different group.
- Reload Samba:
# smbcontrol all reload-config
Assigning a Roaming Profile to a User
Depending on the Windows version, Windows uses different folders to store the roaming profile of a user. However, when you set the profile path for a user, you always set the path to the folder without any version suffix. For example:
\\server\profiles\user_name
For further details, see The Windows Roaming Profile Versions.
Note that you must not set a trailing backslash.
In an Active Directory
Using Active Directory Users and Computers
In an Active Directory, you can use the Active Directory Users and Computers Windows application to set the path to the user's profile folder. If you do not have the Remote Server Administration Tools (RSAT) installed, see Installing RSAT.
To assign \\server\profiles\demo as profile folder to the demo account:
- Log in to a computer using an account that is enabled to edit user accounts.
- Open the
Active Directory Users and Computersapplication.
- Navigate to the directory container that contains the
demoaccount.
- Right-click to the
demouser account and selectProperties.
- Select the
Profiletab.
- Fill the path to the home folder into the
Profile pathfield.
- Set the path always without any profile version suffix and without trailing backslash. For details, see The Windows Roaming Profile Versions.
- Click
OK.
The setting is applied the next time the user logs in.
Using a Group Policy Object
Using group policy objects (GPO), you can assign settings to organizational units (OU) or to a domain. This enables you, for example, to automatically assign profile paths to all users that log on to a computer that is a member of the OU or domain. If you move the computer to a different OU or domain, the setting is removed or updated. Using this way, you do not have to assign manually the settings to each user account.
| Windows only supports assigning a profile path using GPOs on a per-computer basis. This means that the path is also applied to local users on domain members, which have no access to the profile share. To set the profile path on a per-user basis, see Using Active Directory Users and Computers. |
To create a group policy object (GPO) for the domain that automatically assigns the \\server\path\user_name path to every user that logs on to a Windows domain member:
- Log in to a computer using an account that is allowed to edit group policies, such as the AD domain
Administratoraccount.
- Open the
Group Policy Management Console. If you are not having the Remote Server Administration Tools (RSAT) installed on this computer, see Installing RSAT.
- Right-click to your AD domain and select
Create a GPO in this domain, and Link it here.
- Enter a name for the GPO, such as
Profiles on server. The new GPO is shown below the domain entry.
- Right-click to the newly-created GPO and select
Editto open theGroup Policy Management Editor.
- Navigate to the
Computer Configuration→Policies→Administrative Templates→System→User Profilesentry.
- Double-click the
Set roaming profile path for all users logging onto this computerpolicy to edit:
- Enable the policy and set the profile path. For example:
\\server\profiles\%USERNAME%
- Windows replaces the
%USERNAME%variable with the user name during login. Set the path without trailing backslash.
- Windows replaces the
- Click
OK.
- Click
- Close the
Group Policy Management Editor. The GPOs are automatically saved on theSysvolshare on the domain controller (DC).
- Close the
Group Policy Management Console.
The GPO is applied at the next reboot of the Windows domain members or when they reload the group policies.
Using ldbedit on a Domain Controller
On a domain controller (DC), to assign, for example, the \\server\profiles\demo\ path as profile folder to the demo account:
- Edit the
demouser account:
# ldbedit -H /usr/local/samba/private/sam.ldb 'sAMAccountName=demo'
- The accounts attributes are displayed in an editor. Append the following attribute and value to the end of the list:
profilePath: \\server\profiles\demo
- You must not set a trailing backslash to the path.
- Save the changes.
The setting is applied the next time the user logs in.
In an NT4 Domain
In an Samba NT4 domain, to set \\server\profiles\%U as path to the profile folder:
- Add the following parameter to the
[global]section in yoursmb.conffile:
logon path = \\%L\Profiles\%U
- During logging in to the domain member, Samba automatically replaces the
%Uvariable with the session user name. For further details, see theVariable Substitutionssection in thesmb.conf(5)man page.
- Reload Samba:
# smbcontrol all reload-config