Joining a Windows Server 2008 / 2008 R2 DC to a Samba AD: Difference between revisions
Mmuehlfeld (talk | contribs) m (Updated link) |
Mmuehlfeld (talk | contribs) (Replaced "Verifying the Directory Replication" section with a link to the new separate page about this topic.) |
||
| Line 103: | Line 103: | ||
= Verifying |
= Verifying Directory Replication = |
||
See [[Verifying_the_Directory_Replication_Statuses#Displaying_the_Replication_Statuses_on_a_Windows_DC|Displaying the Replication Statuses on a Windows DC]]. |
|||
A few minutes after the domain controller (DC) started, the connections with all other DCs are automatically established and the replication begins. |
|||
{{Imbox |
|||
To verify the directory replication, run on a Samba DC: |
|||
| type = important |
|||
| text = To optimize replication latency and cost, the knowledge consistency checker (KCC) on Windows DCs do not create a fully-meshed replication topology between all DCs. For further details, see [[The Samba KCC]]. |
|||
# samba-tool drs showrepl |
|||
}} |
|||
Default-First-Site-Name\SAMBADC |
|||
DSA Options: 0x00000001 |
|||
DSA object GUID: 4a6bd92a-6612-4b15-aa8c-9ec371e8994f |
|||
DSA invocationId: 96bc0d6f-9cea-4011-b9a1-0e9971009b20 |
|||
==== INBOUND NEIGHBORS ==== |
|||
DC=DomainDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ NTTIME(0) was successful |
|||
0 consecutive failure(s). |
|||
Last success @ NTTIME(0) |
|||
DC=ForestDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ NTTIME(0) was successful |
|||
0 consecutive failure(s). |
|||
Last success @ NTTIME(0) |
|||
DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:35:09 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:09 2014 CET |
|||
CN=Schema,CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:35:10 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:10 2014 CET |
|||
CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:35:11 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:11 2014 CET |
|||
==== OUTBOUND NEIGHBORS ==== |
|||
DC=DomainDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:35:17 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:17 2014 CET |
|||
DC=ForestDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:35:17 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:17 2014 CET |
|||
DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:34:26 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:34:26 2014 CET |
|||
CN=Schema,CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:34:26 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:34:26 2014 CET |
|||
CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:34:21 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:34:21 2014 CET |
|||
==== KCC CONNECTION OBJECTS ==== |
|||
Connection -- |
|||
Connection name: f55bce90-d458-400a-a4ca-801c3e64bef3 |
|||
Enabled : TRUE |
|||
Server DNS name : Win2008R2DC.samdom.example.com |
|||
Server DN name : CN=NTDS Settings,CN=Win2008R2DC,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com |
|||
TransportType: RPC |
|||
options: 0x00000001 |
|||
Warning: No NC replicated for Connection! |
|||
It can take several minutes until all connections are established. If the connections on existing Samba DCs to the Windows DC are not established within 15 minutes, start the replication manually. For details, see [[Manually Replicating Directory Partitions]]. |
|||
If you see the warning <code>No NC replicated for Connection!</code>, see [[FAQ#What_does_Warning:_No_NC_replicated_for_Connection.21_Mean.3F|FAQ: What does Warning: No NC replicated for Connection! Means]]. |
|||
== Testing the Directory Replication == |
|||
To test that the directory replication works correctly, add for example a user on an existing DC and verify that it shows up automatically on the new promoted Windows DC. |
|||
Revision as of 01:16, 13 May 2017
Introduction
You can join Windows Server 2008 and 2008 R2 as an domain controller (DC) to a Samba Active Directory (AD).
If you want to join a computer running a Windows Server operating system as a domain member, see Joining a Windows Client or Server to a Domain.
Network Configuration
- Click the
Startbutton, search forView network connections, and open the search entry.
- Right-click to your network adapter and select
Properties.
- Configure the IP settings:
- Assign a static IP address, enter the subnet mask, and default gateway.
- Enter the IP of a DNS server that is able to resolve the Active Directory (AD) DNS zone.
- Click
OKto save the settings.
Date and Time Settings
Active Directory uses Kerberos for authentication. Kerberos requires that the domain member and the domain controllers (DC) are having a synchronous time. If the difference exceeds 5 minutes (default), the client is not able to access domain resources for security reasons.
Before you join the domain, check the time configuration:
- Open the
Control Panel.
- Navigrate to
Clock, Language and Region.
- Click
Date and Time.
- Verify the date, time, and time zone settings. Adjust the settings, if necessary.
- Click
OKto save the changes.
Joining the Windows Server to the Domain
- Select
Start/Run, enterdcpromo.exeand clickOK.
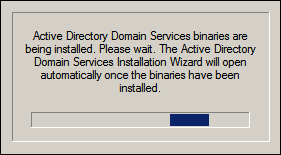
- Windows Server automatically installs missing features, if necessary:
- Check
Use advanced mode installationto display additional options in later steps. ClickOK.
- Read the
Operating System Compatibilityinformation and clickNext.
- Select
Existing forest/Add a domain controller to an existing domain, and clickNext.
- Enter the Samba Active Directory (AD) domain name and credentials that are enabled to join a domain controller (DC) to the domain, such as the domain administrator account. Click
Next.
- Select the domain to join and click
Next.
- If AD sites are configured, select the site to join. Otherwise continue using the
Default-First-Site-Namesite. ClickNext.
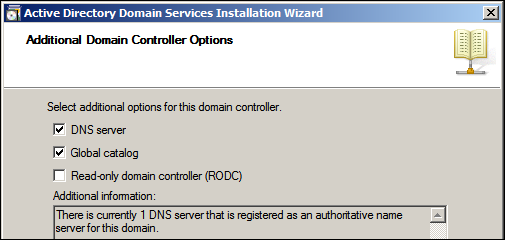
- Select the options to enable on the new DC and click
Next.
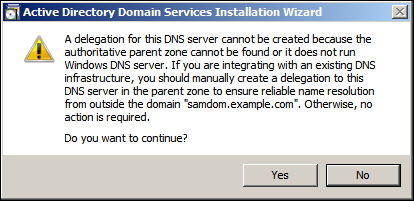
- If you enabled the
DNS serveroption in the previous step, you may see a note, that a delegation for this DNS server cannot be created. ClickYesto continue.
- Select
Replicate data over the network from an existing domain controllerand clickNext.
- Select a DC as source for the initial directory replication or let the installation wizard choose an appropriate DC. Click
Next.
- Set the folders for the AD database, log files and the Sysvol folder. Click
Next.
- Set a Directory Service Restore Mode Administrator Password (DSRM). It is required to boot the Windows DC in safe-mode to restore or repair the AD. Click
Next.
- Verify your settings and click
Nextto start the DC promotion.
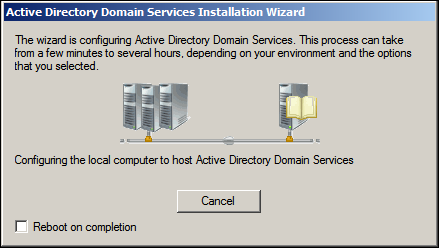
- The wizard starts the installation, replicates the directory, and so on.
- Verify that all DC related DNS records have been created during the promotion. See Verifying and Creating a DC DNS Record.

Do not continue without verifying the DNS records. They must exist for a working directory replication!
- After the wizard completed click
Finish.
- Restart the computer.
The Windows server now acts as an AD DC.
Verifying Directory Replication
See Displaying the Replication Statuses on a Windows DC.
| To optimize replication latency and cost, the knowledge consistency checker (KCC) on Windows DCs do not create a fully-meshed replication topology between all DCs. For further details, see The Samba KCC. |
During the join, Windows tries to replicate the Sysvol directory content from an existing domain controller (DC). Samba currently does not support the DFS-R protocol. For this reason, the new DC may not show a Sysvol share. To enable the share:
- Save the following content to a plain text file named
Win-Create-Sysvol-Share.regusing a text editor such as "Notepad" or "Editor" (not Word/Wordpad/OpenOffice/LibreOffice/etc.):
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Netlogon\Parameters] "SysvolReady"=dword:00000001
- Log in using an account that is member of the local
Administratorsgroup.
- Double-click the file to import it to the Windows registry.
- Reboot to take the changes effect.
Sysvol replication
Samba currently does not support the DFS-R protocol required for Sysvol replication. Please manually synchronise the content between domain controllers (DC) or use a workaround such as Robocopy-based Sysvol Replication.