Time Synchronisation: Difference between revisions
m (grammar & spelling) |
(tell that client reconfiguration is usually NOT necessary) |
||
| (23 intermediate revisions by 5 users not shown) | |||
| Line 1: | Line 1: | ||
= Introduction = |
= Introduction = |
||
In an Active Directory |
In an Active Directory (AD) you must have an accurate time synchronisation. For example, Kerberos requires correct time stamps to prevent replay attacks and the AD uses the time to resolve replication conflicts. The default maximum allowed time deviation in an AD is 5 minutes. If a domain member or domain controller (DC) has a higher or lower time difference, the access is denied. As a result, a user cannot access shares or query the directory. |
||
Samba supports the <code>ntpd</code> from http://ntp.org. The daemon synchronises the time with external sources and enables clients to retrieve the time from the server running the daemon. |
|||
ntpd from http://ntp.org allows allows time synchronisation with external sources and can also be configured to be a time source for others. Please note, that ntpd does not support authenticated time to Windows 2000 clients! This is due to these clients not behaving as the ntpd server expects. As these clients are now very old and unsupported, you may need to find another way to keep these clocks in sync. |
|||
By default domain joined Windows clients synchronize their clock via NT5DS with the AD-DC which holds the PDC-emulator FSMO role. |
|||
'''See the [[Server_information_used_in_documentation|server information used in documentation]] page for used paths, hostnames, etc.''' |
|||
The NT5DS protocol uses digital signatures. These can be provided by Samba if ntp runs on the same server, and is configured as described on this page (with options mssntp and ntpsigndsocket). |
|||
Alternatively you could configure all machines to do standard ntp, but NT5DS is recommended. |
|||
Note that <code>ntpd</code> does not support authenticated time synchronisation with Windows 2000 clients. |
|||
| ⚫ | |||
| ⚫ | |||
== Requirements == |
== Requirements == |
||
* ntpd >= 4.2.6 from |
* ntpd >= 4.2.6 from http://www.ntp.org, compiled with enabled signed ntp support (<code>--enable-ntp-signd</code>) |
||
* |
* Verify the socket permissions on your domain controller (DC). The <code>ntpd</code> daemon must have read permissions in the <code>ntp_signed</code> directory. To list the permissions, enter: |
||
| ⚫ | |||
| ⚫ | |||
# ls -ld /usr/local/samba/var/lib/ntp_signd/ |
# ls -ld /usr/local/samba/var/lib/ntp_signd/ |
||
drwxr-x--- 2 root ntp 4096 1. May 09:30 /usr/local/samba/var/lib/ntp_signd/ |
drwxr-x--- 2 root ntp 4096 1. May 09:30 /usr/local/samba/var/lib/ntp_signd/ |
||
: To set the permissions, run: |
|||
| ⚫ | |||
| ⚫ | |||
| ⚫ | |||
| ⚫ | |||
Typically ntpd's configuration file is /etc/ntpd.conf in most distributions. In the following, you see a working minimum ntpd.conf, that retrieves its time from an external NTP server and provides time via signed NTP for others. |
|||
Typically, the <code>ntpd</code> daemon read its configuration from the <code>/etc/ntpd.conf</code> file. |
|||
| ⚫ | |||
The following is a minimum <code>ntpd.conf</code> file that synchronises the time with three external NTP server and enables clients to query the time using signed NTP requests: |
|||
| ⚫ | |||
server 127.127.1.0 |
server 127.127.1.0 |
||
fudge 127.127.1.0 stratum 10 |
fudge 127.127.1.0 stratum 10 |
||
# |
# Where to retrieve the time from |
||
server 0.pool.ntp.org iburst prefer |
server 0.pool.ntp.org iburst prefer |
||
server 1.pool.ntp.org iburst prefer |
|||
server 2.pool.ntp.org iburst prefer |
|||
driftfile /var/lib/ntp/ntp.drift |
driftfile /var/lib/ntp/ntp.drift |
||
| Line 43: | Line 48: | ||
# Access control |
# Access control |
||
# Default restriction: |
# Default restriction: Allow clients only to query the time |
||
restrict default kod nomodify notrap nopeer mssntp |
restrict default kod nomodify notrap nopeer mssntp |
||
# |
# No restrictions for "localhost" |
||
restrict 127.0.0.1 |
restrict 127.0.0.1 |
||
# |
# Enable the time sources to only provide time to this host |
||
restrict 0.pool.ntp.org mask 255.255.255.255 nomodify notrap nopeer noquery |
restrict 0.pool.ntp.org mask 255.255.255.255 nomodify notrap nopeer noquery |
||
restrict 1.pool.ntp.org mask 255.255.255.255 nomodify notrap nopeer noquery |
|||
restrict 2.pool.ntp.org mask 255.255.255.255 nomodify notrap nopeer noquery |
|||
For further information about ntpd access control, see http://support.ntp.org/bin/view/Support/AccessRestrictions. |
For further information about the <code>ntpd</code> access control, see http://support.ntp.org/bin/view/Support/AccessRestrictions. |
||
Examples about ntpd SELinux labeling and policy you will find [[Time_syncronisation_SELinux_labeling_and_policy|here]]. |
|||
If you have SELinux enabled on your server, see [[Time_Synchronisation_-_SELinux_Labeling_and_Policy|Time Synchronisation - SELinux Labeling and Policy]]. |
|||
= Configuring |
= Configuring Time Synchronisation on a Unix Domain Member = |
||
== Requirements == |
== Requirements == |
||
* ntpd from |
* ntpd from http://www.ntp.org. |
||
== |
== Set up the ntpd.conf File on a Unix Domain Member == |
||
Typically, the <code>ntpd</code> daemon reads its configuration, depending on the operating system, from the <code>/etc/ntpd.conf</code> or <code>/etc/ntp.conf</code> file. |
|||
Typically ntpd's configuration file is /etc/ntpd.conf in most distributions. In the following, you see a working minimum ntpd.conf, that retrieves its time from an Samba AD Domain Controller and doesn't provide NTP for others. |
|||
The following is a minimum conf file that synchronises the time with the Samba Active Directory (AD) domain controllers (DC) <code>DC1</code> and <code>DC2</code> and does not provide time services for other hosts. |
|||
| ⚫ | |||
| ⚫ | |||
server 127.127.1.0 |
server 127.127.1.0 |
||
fudge 127.127.1.0 stratum 10 |
fudge 127.127.1.0 stratum 10 |
||
# |
# Where to retrieve the time from |
||
server DC1.samdom.example.com iburst prefer |
server DC1.samdom.example.com iburst prefer |
||
server DC2.samdom.example.com iburst |
|||
driftfile /var/lib/ntp/ntp.drift |
driftfile /var/lib/ntp/ntp.drift |
||
| Line 82: | Line 93: | ||
# Access control |
# Access control |
||
# Default restriction |
# Default restriction: Disallow everything |
||
restrict default ignore |
restrict default ignore |
||
# |
# No restrictions for "localhost" |
||
restrict 127.0.0.1 |
restrict 127.0.0.1 |
||
# |
# Enable the time sources only to only provide time to this host |
||
restrict DC1.samdom.example.com mask 255.255.255.255 nomodify notrap nopeer noquery |
restrict DC1.samdom.example.com mask 255.255.255.255 nomodify notrap nopeer noquery |
||
restrict DC2.samdom.example.com mask 255.255.255.255 nomodify notrap nopeer noquery |
|||
| ⚫ | |||
| ⚫ | |||
| ⚫ | |||
The following describes the basics of how to configure time synchronizsation on a Windows domain member. For further details, see your Microsoft Windows documentation. |
|||
| ⚫ | |||
== Default Time Source == |
|||
Per default, Windows clients in an Active Directory, automatically synchronize their time with the DC, owning the PDC emulator role. If you don't want to use a different source or to configure multiple time server, etc. you don't have to take any action. |
|||
Windows AD domain members use the DC holding the [[Flexible_Single-Master_Operations_(FSMO)_Roles#PDC_Emulator|PDC emulator FSMO role]] as default time source. If you have set up ntp on the DC as described on this page, you usually do not need to reconfigure the clients. Alternative configuration options for the clients are described below. |
|||
For more information about the time synchronisation and hierarchy in an AD, see http://technet.microsoft.com/en-us/library/cc773013%28v=ws.10%29.aspx#w2k3tr_times_how_izcr. |
|||
== Setting |
== Setting User Defined Time Sources and Options == |
||
To create a group policy object (GPO) to for setting a user defined NTP time source and options: |
|||
If you require your Windows clients to synchronize time with a different server than your DC owning the PDC role, you can configure this via Group Policies. Using the following way, you can define multiple time servers and adjust time synchronisation related options: |
|||
* Log in to a computer using an account that is allowed you to edit group policies, such as the AD domain <code>Administrator</code> account. |
|||
* Create a new Group Policy Object in the Group Policy Management Console (part of the [[Installing_RSAT|Remote Server Administration Tools]]) and edit it. |
|||
* |
* Open the <code>Group Policy Management Console</code>. If you are not having the Remote Server Administration Tools (RSAT) installed on this computer, see [[Installing RSAT|Installing RSAT]]. |
||
* Right-click to your AD domain and select <code>Create a GPO in this domain, and Link it here</code>. |
|||
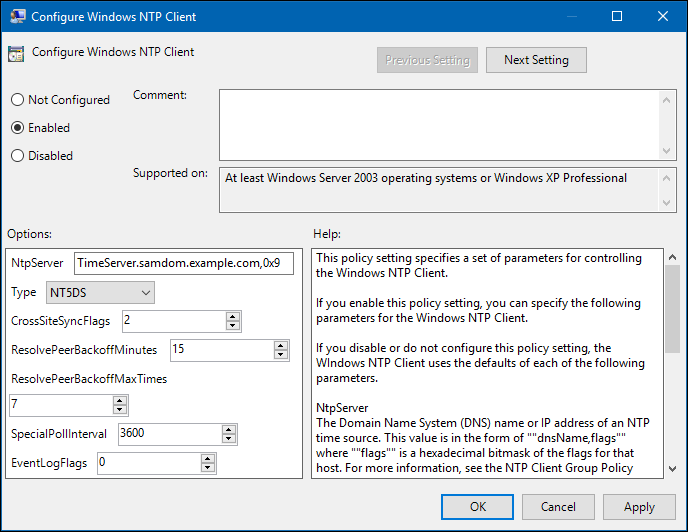
* Edit the "Configure Windows NTP Client" policy: |
|||
* Enter a name for the GPO, such as <code>Time Sources</code>. The new GPO is shown below the domain entry. |
|||
| ⚫ | |||
* Right-click to the newly-created GPO and select <code>Edit</code> to open the <code>Group Policy Management Editor</code>. |
|||
:This example changes the NTP server setting to a DC that provides time, but is not owner of the PDC role. For further explanations on the possible options, see the description in the policy and, visit http://technet.microsoft.com/de-de/library/cc779145%28v=ws.10%29.aspx. |
|||
* Navigate to the <code>Computer Configuration</code> → <code>Policies</code> → <code>Administrative Templates</code> → <code>System</code> → <code>Windows Time Service</code> → <code>Time Providers</code> entry, and double-click <code>Configure Windows NTP Client</code> to configure the policy: |
|||
* Save the GPO and link it to the desired OU. |
|||
:* Enable the policy and set the following options: |
|||
::* Enter the fully-quallified domain name (FQDN) of the NTP server to the <code>NtpServer</code> field and and append the <code>0x9</code> flag. For example: |
|||
| ⚫ | |||
::: To enter multiple server, separate the individual entries using a space. |
|||
::* Keep the <code>NT5DS</code> type setting. |
|||
::* Update the additional parameters, if necessary. |
|||
:* Click <code>OK</code> to save the settings. |
|||
* Navigate to the <code>Computer Configuration</code> → <code>Policies</code> → <code>Administrative Templates</code> → <code>System</code> → <code>Windows Time Service</code> → <code>Time Providers</code> entry, and double-click <code>Enable Windows NTP Client</code> to configure the policy: |
|||
:* Enable the policy. |
|||
:* Click <code>OK</code> to save the settings. |
|||
* Close the <code>Group Policy Management Editor</code>. |
|||
* Close the <code>Group Policy Management Console</code>. |
|||
Notes: |
|||
= Configuring time synchronisation on Linux clients = |
|||
* The default Type NT5DS ignores the parameter NtpServer, and syncs with the DC. |
|||
See [[#Configuring_time_synchronisation_on_Samba_Domain_Members|Configuring Time Synchronisation on Samba Domain Members]]. |
|||
* If ntpd on your DC is not configured for mssntp with ntpsigndsocket, use Type NTP. |
|||
* If a client will not be able to connect to the DC for a long time (for example a laptop), use Type AllSync and set NtpServer to "time.windows.com,0x9". This will cause the client to try both NT5DS to your DC, and NTP to NtpServer. |
|||
---- |
---- |
||
[[Category:Configuration]] |
|||
[[Category:Active Directory]] |
[[Category:Active Directory]] |
||
Revision as of 11:32, 26 April 2018
Introduction
In an Active Directory (AD) you must have an accurate time synchronisation. For example, Kerberos requires correct time stamps to prevent replay attacks and the AD uses the time to resolve replication conflicts. The default maximum allowed time deviation in an AD is 5 minutes. If a domain member or domain controller (DC) has a higher or lower time difference, the access is denied. As a result, a user cannot access shares or query the directory.
Samba supports the ntpd from http://ntp.org. The daemon synchronises the time with external sources and enables clients to retrieve the time from the server running the daemon.
By default domain joined Windows clients synchronize their clock via NT5DS with the AD-DC which holds the PDC-emulator FSMO role. The NT5DS protocol uses digital signatures. These can be provided by Samba if ntp runs on the same server, and is configured as described on this page (with options mssntp and ntpsigndsocket). Alternatively you could configure all machines to do standard ntp, but NT5DS is recommended.
Note that ntpd does not support authenticated time synchronisation with Windows 2000 clients.
Configuring Time Synchronisation on a DC
Requirements
- ntpd >= 4.2.6 from http://www.ntp.org, compiled with enabled signed ntp support (
--enable-ntp-signd)
- Verify the socket permissions on your domain controller (DC). The
ntpddaemon must have read permissions in thentp_signeddirectory. To list the permissions, enter:
# ls -ld /usr/local/samba/var/lib/ntp_signd/ drwxr-x--- 2 root ntp 4096 1. May 09:30 /usr/local/samba/var/lib/ntp_signd/
- To set the permissions, run:
# chown root:ntp /usr/local/samba/var/lib/ntp_signd/ # chmod 750 /usr/local/samba/var/lib/ntp_signd/
Set up the ntpd.conf File on a DC
Typically, the ntpd daemon read its configuration from the /etc/ntpd.conf file.
The following is a minimum ntpd.conf file that synchronises the time with three external NTP server and enables clients to query the time using signed NTP requests:
# Local clock. Note that is not the "localhost" address! server 127.127.1.0 fudge 127.127.1.0 stratum 10 # Where to retrieve the time from server 0.pool.ntp.org iburst prefer server 1.pool.ntp.org iburst prefer server 2.pool.ntp.org iburst prefer driftfile /var/lib/ntp/ntp.drift logfile /var/log/ntp ntpsigndsocket /usr/local/samba/var/lib/ntp_signd/ # Access control # Default restriction: Allow clients only to query the time restrict default kod nomodify notrap nopeer mssntp # No restrictions for "localhost" restrict 127.0.0.1 # Enable the time sources to only provide time to this host restrict 0.pool.ntp.org mask 255.255.255.255 nomodify notrap nopeer noquery restrict 1.pool.ntp.org mask 255.255.255.255 nomodify notrap nopeer noquery restrict 2.pool.ntp.org mask 255.255.255.255 nomodify notrap nopeer noquery
For further information about the ntpd access control, see http://support.ntp.org/bin/view/Support/AccessRestrictions.
If you have SELinux enabled on your server, see Time Synchronisation - SELinux Labeling and Policy.
Configuring Time Synchronisation on a Unix Domain Member
Requirements
- ntpd from http://www.ntp.org.
Set up the ntpd.conf File on a Unix Domain Member
Typically, the ntpd daemon reads its configuration, depending on the operating system, from the /etc/ntpd.conf or /etc/ntp.conf file.
The following is a minimum conf file that synchronises the time with the Samba Active Directory (AD) domain controllers (DC) DC1 and DC2 and does not provide time services for other hosts.
# Local clock. Note that is not the "localhost" address! server 127.127.1.0 fudge 127.127.1.0 stratum 10 # Where to retrieve the time from server DC1.samdom.example.com iburst prefer server DC2.samdom.example.com iburst driftfile /var/lib/ntp/ntp.drift logfile /var/log/ntp # Access control # Default restriction: Disallow everything restrict default ignore # No restrictions for "localhost" restrict 127.0.0.1 # Enable the time sources only to only provide time to this host restrict DC1.samdom.example.com mask 255.255.255.255 nomodify notrap nopeer noquery restrict DC2.samdom.example.com mask 255.255.255.255 nomodify notrap nopeer noquery
For further information about the ntpd access control, see http://support.ntp.org/bin/view/Support/AccessRestrictions.
Configuring Time Synchronisation on a Windows Domain Member
The following describes the basics of how to configure time synchronizsation on a Windows domain member. For further details, see your Microsoft Windows documentation.
Default Time Source
Windows AD domain members use the DC holding the PDC emulator FSMO role as default time source. If you have set up ntp on the DC as described on this page, you usually do not need to reconfigure the clients. Alternative configuration options for the clients are described below.
For more information about the time synchronisation and hierarchy in an AD, see http://technet.microsoft.com/en-us/library/cc773013%28v=ws.10%29.aspx#w2k3tr_times_how_izcr.
Setting User Defined Time Sources and Options
To create a group policy object (GPO) to for setting a user defined NTP time source and options:
- Log in to a computer using an account that is allowed you to edit group policies, such as the AD domain
Administratoraccount.
- Open the
Group Policy Management Console. If you are not having the Remote Server Administration Tools (RSAT) installed on this computer, see Installing RSAT.
- Right-click to your AD domain and select
Create a GPO in this domain, and Link it here.
- Enter a name for the GPO, such as
Time Sources. The new GPO is shown below the domain entry.
- Right-click to the newly-created GPO and select
Editto open theGroup Policy Management Editor.
- Navigate to the
Computer Configuration→Policies→Administrative Templates→System→Windows Time Service→Time Providersentry, and double-clickConfigure Windows NTP Clientto configure the policy:
- Enable the policy and set the following options:
- Enter the fully-quallified domain name (FQDN) of the NTP server to the
NtpServerfield and and append the0x9flag. For example:
- Keep the
NT5DStype setting. - Update the additional parameters, if necessary.
- Enter the fully-quallified domain name (FQDN) of the NTP server to the
- Click
OKto save the settings.
- Navigate to the
Computer Configuration→Policies→Administrative Templates→System→Windows Time Service→Time Providersentry, and double-clickEnable Windows NTP Clientto configure the policy:
- Enable the policy.
- Click
OKto save the settings.
- Close the
Group Policy Management Editor.
- Close the
Group Policy Management Console.
Notes:
- The default Type NT5DS ignores the parameter NtpServer, and syncs with the DC.
- If ntpd on your DC is not configured for mssntp with ntpsigndsocket, use Type NTP.
- If a client will not be able to connect to the DC for a long time (for example a laptop), use Type AllSync and set NtpServer to "time.windows.com,0x9". This will cause the client to try both NT5DS to your DC, and NTP to NtpServer.