Setting up a Share Using Windows ACLs: Difference between revisions
Mmuehlfeld (talk | contribs) m (Added missing part of a step.) |
(/* added note) |
||
| (21 intermediate revisions by 2 users not shown) | |||
| Line 7: | Line 7: | ||
* NT4 backup domain controllers (BDC) |
* NT4 backup domain controllers (BDC) |
||
* Standalone hosts |
* Standalone hosts |
||
As an alternative to extended ACLs, you can set up shares using POSIX ACLs. For details, see [[Setting_up_a_Share_Using_POSIX_ACLs|Setting up a Share Using POSIX ACLs]]. |
|||
| Line 16: | Line 14: | ||
= Preparing the Host = |
= Preparing the Host = |
||
You need to set up Samba before you are able to create a share. Depending on what type of Samba server you require, see: |
|||
* [[Setting_up_Samba_as_a_Domain_Member|Setting up Samba as a Domain Member]] |
* [[Setting_up_Samba_as_a_Domain_Member|Setting up Samba as a Domain Member]] |
||
* [[Active_Directory_Domain_Controller|Setting up Samba as AD DC]] |
* [[Active_Directory_Domain_Controller|Setting up Samba as AD DC]] |
||
| Line 27: | Line 25: | ||
== File System Support == |
== File System Support == |
||
The file system the share will be created on, must support: |
The file system, the share will be created on, must support: |
||
* user and system <code>xattr</code> name spaces. |
* user and system <code>xattr</code> name spaces. |
||
* extended access control lists (ACL). |
* extended access control lists (ACL). |
||
| Line 37: | Line 35: | ||
== Samba Extended ACL Support == |
== Samba Extended ACL Support == |
||
To create a share with extended access control list (ACL) support, the <code>smbd</code> service must been built with ACL support enabled. |
To create a share with extended access control list (ACL) support, the <code>smbd</code> service must have been built with ACL support enabled. A Samba host working as an Active Directory (AD) domain controller (DC), is always enabled with extended ACL support. |
||
To verify if Samba has been built with ACL support, enter: |
To verify if Samba has been built with ACL support, enter: |
||
| Line 46: | Line 44: | ||
If no output is displayed: |
If no output is displayed: |
||
* Samba was built using the <code>--with-acl-support=no</code> parameter. |
* Samba was built using the <code>--with-acl-support=no</code> parameter. |
||
* The Samba <code>configure</code> script was unable to locate the required libraries for ACL support. For details, see [[ |
* The Samba <code>configure</code> script was unable to locate the required libraries for ACL support. For details, see [[Package Dependencies Required to Build Samba]]. |
||
| Line 58: | Line 56: | ||
vfs objects = acl_xattr |
vfs objects = acl_xattr |
||
map acl inherit = yes |
map acl inherit = yes |
||
# the next line is only required on Samba versions less than 4.9.0 |
|||
store dos attributes = yes |
store dos attributes = yes |
||
| Line 73: | Line 72: | ||
== Granting the <code>SeDiskOperatorPrivilege</code> Privilege == |
== Granting the <code>SeDiskOperatorPrivilege</code> Privilege == |
||
Only users and groups having the <code>SeDiskOperatorPrivilege</code> privilege granted can configure share permissions. |
Only users and groups having the <code>SeDiskOperatorPrivilege</code> privilege granted can configure share permissions. |
||
| ⚫ | |||
| type = note |
|||
| text = Only users or groups that are known to Unix can be used. This means that if you use the winbind 'ad' backend on Unix domain members, you must add a uidNumber attribute to users, or a gidNumber to groups in AD. |
|||
}} |
|||
{{Imbox |
|||
| type = note |
|||
| text = If you use the winbind 'ad' backend on Unix domain members and you add a gidNumber attribute to the <code>Domain Admins</code> group in AD, you will break the mapping in <code>idmap.ldb</code>. <code>Domain Admins</code> is mapped as <code>ID_TYPE_BOTH</code> in <code>idmap.ldb</code>, this is to allow the group to own files in <code>Sysvol</code> on a Samba AD DC. It is suggested you create a new group (<code>Unix Admins</code> for instance), give this group a <code>gidNumber</code> attribute and add it to the <code>Administrators</code> group and then use the group wherever you see <code>Domain Admins</code>. |
|||
}} |
|||
To grant the privilege to the <code>Domain Admins</code> group, enter: |
|||
# net rpc rights grant "SAMDOM\Domain Admins" SeDiskOperatorPrivilege -U "SAMDOM\administrator" |
# net rpc rights grant "SAMDOM\Domain Admins" SeDiskOperatorPrivilege -U "SAMDOM\administrator" |
||
| Line 81: | Line 93: | ||
{{Imbox |
{{Imbox |
||
| type = note |
| type = note |
||
| text = It is recommended to grant the |
| text = It is recommended to grant the privilege to a group instead of individual accounts. This enables you to add and revoke the privilege by updating the group membership. |
||
}} |
}} |
||
| Line 91: | Line 103: | ||
BUILTIN\Administrators |
BUILTIN\Administrators |
||
SAMDOM\Domain Admins |
SAMDOM\Domain Admins |
||
{{Imbox |
|||
| type = important |
|||
| text = You need to grant the <code>SeDiskOperatorPrivilege</code> privilege on the Samba server that holds the share. |
|||
}} |
|||
| Line 100: | Line 117: | ||
To share the <code>/srv/samba/Demo/</code> directory using the <code>Demo</code> share name: |
To share the <code>/srv/samba/Demo/</code> directory using the <code>Demo</code> share name: |
||
* |
* As the <code>root</code> user, create the directory: |
||
# mkdir -p /srv/samba/Demo/ |
# mkdir -p /srv/samba/Demo/ |
||
* To enable accounts other than the domain user <code>Administrator</code> to set permissions on Windows, grant <code>Full control</code> (<code>rwx</code>) to the user or group you granted the <code>SeDiskOperatorPrivilege</code> privilege. For example: |
|||
# chown root:"Domain Admins" /srv/samba/Demo/ |
|||
# chmod 0770 /srv/samba/Demo/ |
|||
* Add the <code>[Demo]</code> share definition to your <code>smb.conf</code> file: |
* Add the <code>[Demo]</code> share definition to your <code>smb.conf</code> file: |
||
| Line 110: | Line 132: | ||
read only = no |
read only = no |
||
| ⚫ | |||
| ⚫ | |||
:{{Imbox |
|||
| type = important |
| type = important |
||
| text = Do not set additional share parameters, such as <code>force user</code>. Adding them to the share definition can prevent you from configuring or using the share. |
| text = Do not set additional share parameters, such as <code>force user</code>. Adding them to the share definition can prevent you from configuring or using the share. |
||
}} |
}} |
||
| ⚫ | |||
* Reload the Samba configuration: |
* Reload the Samba configuration: |
||
| Line 131: | Line 153: | ||
To set permissions and ACLs on the <code>Demo</code> share: |
To set permissions and ACLs on the <code>Demo</code> share: |
||
* Log on to a Windows host using an account that has the <code>SeDiskOperatorPrivilege</code> privilege granted. |
* Log on to a Windows host using an account that has the <code>SeDiskOperatorPrivilege</code> privilege granted. e.g. <code>SAMDOM\Administrator</code> or <code>SAMDOM\john</code> where <code>john</code> is a member of <code>Domain Admins</code>. |
||
* Click <code>Start</code>, enter <code>Computer Management</code>, and start the application. |
* Click <code>Start</code>, enter <code>Computer Management</code>, and start the application. |
||
| Line 142: | Line 164: | ||
:[[Image:Computer_Management_Shares.png]] |
:[[Image:Computer_Management_Shares.png]] |
||
* Right-click to the share and select <code>Properties</code>. |
* Right-click to the share and select <code>Properties</code>. |
||
* Select the <code>Share Permissions</code> tab and |
* Select the <code>Share Permissions</code> tab and check the share permissions, you need to see <code>Everyone</code>. For example: |
||
:[[Image: |
:[[Image:share.png]] |
||
{{Imbox |
|||
| type = note |
|||
| text = You should not need to change anything here. |
|||
}} |
|||
: Samba stores share permissions in the <code>/usr/local/samba/var/locks/share_info.tdb</code> database. |
: Samba stores share permissions in the <code>/usr/local/samba/var/locks/share_info.tdb</code> database. |
||
* Select the <code>Security</code> tab. |
* Select the <code>Security</code> tab. |
||
| Line 155: | Line 188: | ||
:[[Image:Demo_Share_Security.png]] |
:[[Image:Demo_Share_Security.png]] |
||
: For details about using the <code>SYSTEM</code> account on a Samba share see [[The SYSTEM Account]]. |
|||
: For details where the ACLs are stored, see [[#File_System_ACLs_in_the_Back_End|File System ACLs in the Back End]]. |
: For details where the ACLs are stored, see [[#File_System_ACLs_in_the_Back_End|File System ACLs in the Back End]]. |
||
* Click the <code>Add</code> button. |
|||
* Click <code>Advanced</code> button |
|||
* Click <code>Find Now</code> |
|||
* Select a user or group from the list, <code>Domain Users</code> for instance. |
|||
* Click <code>OK</code> |
|||
* Click <code>OK</code> |
|||
* Select permissions to grant, <code>Full control</code> for instance. |
|||
* A windows security box should open, asking if you want to continue, Click <code>Yes</code> |
|||
* If you check the list of <code>Group or user names</code>, you should find <code>Domain Users</code> listed |
|||
* Click <code>OK</code> to close the <code>Permissions for Demo</code> window. |
* Click <code>OK</code> to close the <code>Permissions for Demo</code> window. |
||
| Line 183: | Line 236: | ||
:[[Image:Folder_Permissions.png]] |
:[[Image:Folder_Permissions.png]] |
||
: For details about using the <code>SYSTEM</code> account on a Samba share see [[The SYSTEM Account]]. |
|||
: For details where the ACLs are stored, see [[#File_System_ACLs_in_the_Back_End|File System ACLs in the Back End]]. |
: For details where the ACLs are stored, see [[#File_System_ACLs_in_the_Back_End|File System ACLs in the Back End]]. |
||
| Line 223: | Line 278: | ||
default:other::--- |
default:other::--- |
||
* To list the <code> |
* To list the <code>security.NTACL</code> extended attribute of the <code>/srv/samba/Demo/</code> directory, enter: |
||
# getfattr -d /srv/samba/Demo/ |
# getfattr -n security.NTACL -d /srv/samba/Demo/ |
||
# file: srv/samba/Demo/ |
# file: srv/samba/Demo/ |
||
security.NTACL=0sBAAEAAAAAgAEAAIAAQC4zK0lHchKFvwXwbPR/h8P8sXMj5dNIT5QQuWsYwO3RAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAcG9zaXhfYWNsAEbGxuGu39MBuiZRk2pYxeL5ZWc4au0ikqRAk53MkjVd2b4quyk2WwcAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEABJy0AAAA0AAAAAAAAADsAAAAAQUAAAAAAAUVAAAASSVmaZneO8cxOHk/9AEAAAEFAAAAAAAFFQAAAEklZmmZ3jvHMTh5P0oIAAACAMQABwAAAAALFACpABIAAQEAAAAAAAEAAAAAAAAUAAAAEAABAQAAAAAAAQAAAAAACxQA/wEfAAEBAAAAAAADAAAAAAALFACpABIAAQEAAAAAAAMBAAAAAAMkAP8BHwABBQAAAAAABRUAAABJJWZpmd47xzE4eT9KCAAAAAAkAP8BHwABBQAAAAAABRUAAABJJWZpmd47xzE4eT/0AQAAAAMkAL8BEwABBQAAAAAABRUAAABJJWZpmd47xzE4eT8BAgAA |
|||
user.SAMBA_PAI=0sAgScBwAHAAABAAAAAAAAAAAAAAAC/////wABAAAAAAAAAAAAAAABEScAAAABECcAAAABAAAAAAAAAAAAAAAC/////wABAAAAAAAAAAAAAAMBEScAAAMBECcAAA== |
|||
The previous example of file system ACLs and the extended attribute is mapped to the following Windows ACLs: |
The previous example of file system ACLs and the extended attribute is mapped to the following Windows ACLs: |
||
| Line 245: | Line 300: | ||
|} |
|} |
||
* To get the ACL in a more readable form, enter: |
|||
# samba-tool ntacl get /usr/local/samba/var/locks/sysvol --as-sddl |
|||
# O:BAG:SYD:PAI(A;OICIIO;WOWDGRGWGX;;;CO)(A;OICIIO;GRGX;;;AU)(A;;0x001200a9;;;AU)(A;OICIIO;GA;;;SY)(A;;0x001f01ff;;;SY)(A;OICIIO;WOWDGRGWGX;;;BA)(A;;0x001e01bf;;;BA)(A;OICIIO;GRGX;;;SO)(A;;0x001200a9;;;SO) |
|||
| Line 254: | Line 313: | ||
* [[Troubleshooting_Samba_Domain_Members|Troubleshooting Samba Domain Members]] |
* [[Troubleshooting_Samba_Domain_Members|Troubleshooting Samba Domain Members]] |
||
* [[Samba_AD_DC_Troubleshooting|Samba AD DC Troubleshooting]] |
* [[Samba_AD_DC_Troubleshooting|Samba AD DC Troubleshooting]] |
||
---- |
|||
[[Category:Active Directory]] |
|||
[[Category:Domain Members]] |
|||
[[Category:File Serving]] |
|||
[[Category:NT4 Domains]] |
|||
Revision as of 14:35, 14 October 2019
Introduction
Extended access control lists (ACL) enable you to set permissions on shares, files, and directories using Windows ACLs and applications. Samba supports shares using extended ACLs on:
- Domain members
- Active Directory (AD) domain controllers (DC)
- NT4 primary domain controller (PDC)
- NT4 backup domain controllers (BDC)
- Standalone hosts
Preparing the Host
You need to set up Samba before you are able to create a share. Depending on what type of Samba server you require, see:
- Setting up Samba as a Domain Member
- Setting up Samba as AD DC
- Setting up Samba as an NT4 PDC (Quick Start)
- Setting up Samba as an NT4 BDC
- Setting up Samba as a Standalone Server
File System Support
The file system, the share will be created on, must support:
- user and system
xattrname spaces. - extended access control lists (ACL).
For further details, see File system support.
Samba Extended ACL Support
To create a share with extended access control list (ACL) support, the smbd service must have been built with ACL support enabled. A Samba host working as an Active Directory (AD) domain controller (DC), is always enabled with extended ACL support.
To verify if Samba has been built with ACL support, enter:
# smbd -b | grep HAVE_LIBACL HAVE_LIBACL
If no output is displayed:
- Samba was built using the
--with-acl-support=noparameter. - The Samba
configurescript was unable to locate the required libraries for ACL support. For details, see Package Dependencies Required to Build Samba.
Enable Extended ACL Support in the smb.conf File
To configure shares using extended access control lists (ACL), you must enable the support in the smb.conf file. To enable extended ACL support globally, add the following settings to the [global] section of your smb.conf file:
vfs objects = acl_xattr map acl inherit = yes # the next line is only required on Samba versions less than 4.9.0 store dos attributes = yes
| On a Samba Active Directory (AD) domain controller (DC), extended ACL support is automatically enabled globally. You must not enable the support manually. |
Alternatively, to enable extended ACL support only for a specific share, add the parameters to the share's section.
For further details about the parameters, see the smb.conf(5) man page.
Granting the SeDiskOperatorPrivilege Privilege
Only users and groups having the SeDiskOperatorPrivilege privilege granted can configure share permissions.
| Only users or groups that are known to Unix can be used. This means that if you use the winbind 'ad' backend on Unix domain members, you must add a uidNumber attribute to users, or a gidNumber to groups in AD. |
If you use the winbind 'ad' backend on Unix domain members and you add a gidNumber attribute to the Domain Admins group in AD, you will break the mapping in idmap.ldb. Domain Admins is mapped as ID_TYPE_BOTH in idmap.ldb, this is to allow the group to own files in Sysvol on a Samba AD DC. It is suggested you create a new group (Unix Admins for instance), give this group a gidNumber attribute and add it to the Administrators group and then use the group wherever you see Domain Admins. |
To grant the privilege to the Domain Admins group, enter:
# net rpc rights grant "SAMDOM\Domain Admins" SeDiskOperatorPrivilege -U "SAMDOM\administrator" Enter SAMDOM\administrator's password: Successfully granted rights.
| It is recommended to grant the privilege to a group instead of individual accounts. This enables you to add and revoke the privilege by updating the group membership. |
To list all users and groups having the SeDiskOperatorPrivilege privilege granted, enter:
# net rpc rights list privileges SeDiskOperatorPrivilege -U "SAMDOM\administrator" Enter administrator's password: SeDiskOperatorPrivilege: BUILTIN\Administrators SAMDOM\Domain Admins
You need to grant the SeDiskOperatorPrivilege privilege on the Samba server that holds the share. |
To share the /srv/samba/Demo/ directory using the Demo share name:
- As the
rootuser, create the directory:
# mkdir -p /srv/samba/Demo/
- To enable accounts other than the domain user
Administratorto set permissions on Windows, grantFull control(rwx) to the user or group you granted theSeDiskOperatorPrivilegeprivilege. For example:
# chown root:"Domain Admins" /srv/samba/Demo/ # chmod 0770 /srv/samba/Demo/
- Add the
[Demo]share definition to yoursmb.conffile:
[Demo]
path = /srv/samba/Demo/
read only = no
- Further share-specific settings and file system permissions are set using the Windows utilities.

Do not set additional share parameters, such as force user. Adding them to the share definition can prevent you from configuring or using the share.
- Reload the Samba configuration:
# smbcontrol all reload-config
When you configure a share with extended access control lists (ACL) support, you set the share permissions using Windows utilities instead of adding parameters to the share section in the smb.conf file.
To set permissions and ACLs on the Demo share:
- Log on to a Windows host using an account that has the
SeDiskOperatorPrivilegeprivilege granted. e.g.SAMDOM\AdministratororSAMDOM\johnwherejohnis a member ofDomain Admins.
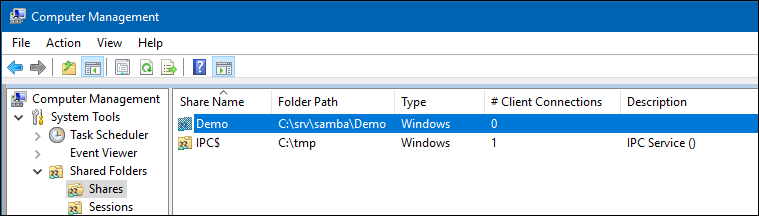
- Click
Start, enterComputer Management, and start the application.
- Select
Action/Connect to another computer.
- Enter the name of the Samba host and click
OKto connect the console to the host.
- Open the
System Tools/Shared Folders/Sharesmenu entry.
- Right-click to the share and select
Properties.
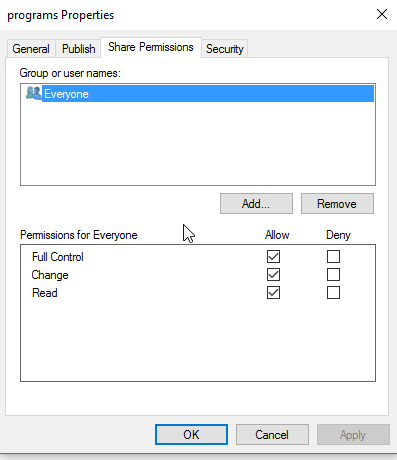
- Select the
Share Permissionstab and check the share permissions, you need to seeEveryone. For example:
| You should not need to change anything here. |
- Samba stores share permissions in the
/usr/local/samba/var/locks/share_info.tdbdatabase.
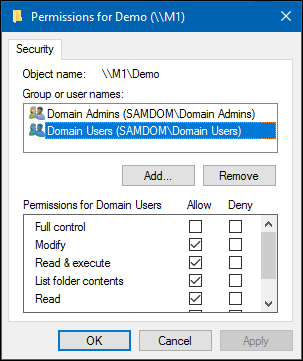
- Select the
Securitytab.
- Click the
Editbutton and set the file system ACLs on the share's root directory. For example:
- For details about using the
SYSTEMaccount on a Samba share see The SYSTEM Account.
- For details where the ACLs are stored, see File System ACLs in the Back End.
- Click the
Addbutton.
- Click
Advancedbutton
- Click
Find Now
- Select a user or group from the list,
Domain Usersfor instance.
- Click
OK
- Click
OK
- Select permissions to grant,
Full controlfor instance.
- A windows security box should open, asking if you want to continue, Click
Yes
- If you check the list of
Group or user names, you should findDomain Userslisted
- Click
OKto close thePermissions for Demowindow.
- Click
OKto store the updated settings.
For further details about configuring share permissions and ACLs, see the Windows documentation.
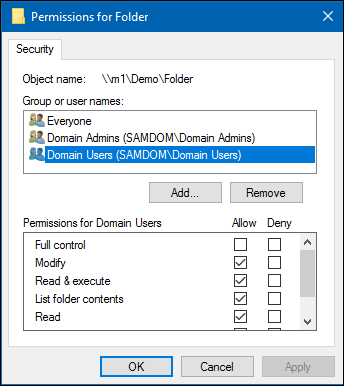
Setting ACLs on a Folder
To set file system permissions on a folder located on a share that uses extended access control lists (ACL):
- Log on to a Windows host using an account that has
Full controlon the folder you want to modify the file system ACLs.
- Navigate to the folder.
- Right-click to the folder and select
Properties.
- Select the
Securitytab and click theEditbutton.
- Set the permission. For example:
- For details about using the
SYSTEMaccount on a Samba share see The SYSTEM Account.
- For details where the ACLs are stored, see File System ACLs in the Back End.
- Click
OKto close thePermissions for Folderwindow.
- Click
OKto store the updated settings.
For further details about setting ACLs, see the Windows documentation.
File System ACLs in the Back End
Samba stores the file system permissions in extended file system access control lists (ACL) and in an extended attribute. For example:
- To list the extended ACLs of the
/srv/samba/Demo/directory, enter:
# getfacl /srv/samba/Demo/ # file: srv/samba/Demo/ # owner: root # group: root user::rwx user:root:rwx group::--- group:root:--- group:domain\040users:rwx group:domain\040admins:rwx mask::rwx other::--- default:user::rwx default:user:root:rwx default:group::--- default:group:root:--- default:group:domain\040users:rwx default:group:domain\040admins:rwx default:mask::rwx default:other::---
- To list the
security.NTACLextended attribute of the/srv/samba/Demo/directory, enter:
# getfattr -n security.NTACL -d /srv/samba/Demo/ # file: srv/samba/Demo/ security.NTACL=0sBAAEAAAAAgAEAAIAAQC4zK0lHchKFvwXwbPR/h8P8sXMj5dNIT5QQuWsYwO3RAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAcG9zaXhfYWNsAEbGxuGu39MBuiZRk2pYxeL5ZWc4au0ikqRAk53MkjVd2b4quyk2WwcAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEABJy0AAAA0AAAAAAAAADsAAAAAQUAAAAAAAUVAAAASSVmaZneO8cxOHk/9AEAAAEFAAAAAAAFFQAAAEklZmmZ3jvHMTh5P0oIAAACAMQABwAAAAALFACpABIAAQEAAAAAAAEAAAAAAAAUAAAAEAABAQAAAAAAAQAAAAAACxQA/wEfAAEBAAAAAAADAAAAAAALFACpABIAAQEAAAAAAAMBAAAAAAMkAP8BHwABBQAAAAAABRUAAABJJWZpmd47xzE4eT9KCAAAAAAkAP8BHwABBQAAAAAABRUAAABJJWZpmd47xzE4eT/0AQAAAAMkAL8BEwABBQAAAAAABRUAAABJJWZpmd47xzE4eT8BAgAA
The previous example of file system ACLs and the extended attribute is mapped to the following Windows ACLs:
| Principal | Permissions | Applies to |
|---|---|---|
| Domain Users (SAMDOM\Domain Users) | Modify, Read & execute, List folder contents, Read, Write | (This folder, subfolders and files) |
| Domain Admins (SAMDOM\Domain Admins) | Full control | (This folder, subfolders and files) |
- To get the ACL in a more readable form, enter:
# samba-tool ntacl get /usr/local/samba/var/locks/sysvol --as-sddl # O:BAG:SYD:PAI(A;OICIIO;WOWDGRGWGX;;;CO)(A;OICIIO;GRGX;;;AU)(A;;0x001200a9;;;AU)(A;OICIIO;GA;;;SY)(A;;0x001f01ff;;;SY)(A;OICIIO;WOWDGRGWGX;;;BA)(A;;0x001e01bf;;;BA)(A;OICIIO;GRGX;;;SO)(A;;0x001200a9;;;SO)
Troubleshooting
For troubleshooting, see: