Setting up Samba as an Active Directory Domain Controller: Difference between revisions
(fix build instructions: use the toplevel build) |
(→Step 10: Configure NTP (Optional): Add the permission of ntp_signd from https://lists.samba.org/archive/samba-technical/2012-August/085900.html) |
||
| Line 414: | Line 414: | ||
You require a recent ntpd version (=>4.2.6) that supports signed ntp. E. g. the version shipped with RHEL6 and Ubuntu < 11.04 are to old. The Ntpd of Debian Squeeze supports signed ntp. |
You require a recent ntpd version (=>4.2.6) that supports signed ntp. E. g. the version shipped with RHEL6 and Ubuntu < 11.04 are to old. The Ntpd of Debian Squeeze supports signed ntp. |
||
1a. Download ntpd from ntp.org (verify md5 sum) and compile it (add additionals ./configure parameters, if needed): |
|||
$ tar -zxvf ntp-4.x.x.tar.gz |
$ tar -zxvf ntp-4.x.x.tar.gz |
||
| Line 421: | Line 421: | ||
$ make |
$ make |
||
$ make install |
$ make install |
||
1b. Set the permission of the ntp_signd directory (default /usr/local/samba/var/lib/ntp_signd/) to 0750 and its owner to root:ntp to ensure that it is readable from ntpd. |
|||
2a. If you already have a supported ntpd version and ntp.conf, you have to add/adjust only the following lines for minimal: |
2a. If you already have a supported ntpd version and ntp.conf, you have to add/adjust only the following lines for minimal: |
||
Revision as of 16:45, 5 March 2013
HOWTO to set up Samba as an Active Directory compatible Domain Controller
This document explains how to setup a simple Samba server as a Domain Controller compatible with Microsoft's Active Directory, for use particularly by Microsoft Windows clients that are joined to the Active Directory Domain, for services such as Domain Logon. We refer to this capability as being an AD DC for short.
Video Demonstrations of This HOWTO
A set of demonstration videos is available that may provide a useful overview of the contents of this HOWTO.
A Note on Versions
Samba is developing rapidly. This HOWTO is frequently updated to reflect the latest changes in the Samba git repository. Please see the Samba 4.0 Release Planning for more specifics on the release planning.
Server Information
For the rest of this tutorial, we will be using the following configuration for our example AD DC configuration.
Installation Directory: /usr/local/samba Server Hostname: samba DNS Domain Name: samdom.example.com NT4 Domain Name: samdom IP Address: 192.168.1.2 Server Role: DC
Samba OS Requirements
Because of the constantly changing and ever expanding nature of Linux, the OS Requirements for Samba 4 have been moved from Step 2, to Samba_4/OS_Requirements. This not only includes the required packages for a successful Samba AD DC deployment, but also the required file system features. Please consider that page as a prerequisite to a successful Samba AD DC setup.
Step 1: Download Samba
Currently, there are three methods to download the current Samba sources, either as a tarball of the latest stable release, or a development version via git or rsync. If you hope to work with the team on a development version to resolve issues you may hit via code changes, we recommend using the git method for downloading Samba, as it makes getting updates easier, and also allows you to integrate test patches from Samba developers more easily in case of problems.
In the following examples we will assume that your top-level source is named samba4. If you downloaded a tarball this will instead be based on the name of the tarball downloaded (e.g. samba-4.0.0 for the tarball samba-4.0.0.tar.gz). Also note that in the master branch the Samba 4 code in our current git tree is now located in the top level directory.
Downloading a tarball
If you wish to use a released version of Samba 4.0, you can download the latest Samba 4.0 tarball from the Samba website
Downloading via git
Git allows you to download the source tree via either the git or httpprotocols. In general, the git protocol is the preferred choice since it compresses the data being transferred. To download the source tree via git, run the following command:
$ git clone git://git.samba.org/samba.git samba4
Alternatively, if you prefer to use the http protocol, run the following command:
$ git clone http://gitweb.samba.org/samba.git samba4
Either command will create a directory called samba4 in the current directory. This directory will hold a checkout of the branch you choose to download (master, test, or stable).
If you are using the checkout for a production installation you should use the following git branches:
- 'v4-0-stable' (which contains the lastest stable 4.0.x release)
$ git clone -b v4-0-stable git://git.samba.org/samba.git samba4
or
- 'v4-0-test' (which contains the patches scheduled for the next stable 4.0.x release)
$ git clone -b v4-0-test git://git.samba.org/samba.git samba4
Updating via git
If you already have downloaded the source tree via git and want to update the tree to the latest version, run the following command in your samba4 directory:
$ git pull
If you get an error like this:
fatal: Unable to create '[...]/samba_master/.git/index.lock': File exists.
Run the command below to reset your tree.
If you are having trouble compiling the source, it may be due to stale files. You can reset your git tree to correct these errors. To reset your git tree, run the following command in your samba4 directory:
$ git clean -x -f -d
Step 2: Compile Samba
To build Samba, run the following commands in your Samba source directory:
$ ./configure --enable-debug --enable-selftest $ make
The above command will setup Samba to install in /usr/local/samba. If you want Samba to install in a different directory, then you should use the --prefix option to configure.
The reason we recommend using --enable-debug --enable-selftest for Samba is that it will include extra debug information that will help us diagnose problems in case of failures, and will also allow you to run our selftest make test to validate that Samba can behave correctly on your platform. Both of these are however, entirely optional.
Profiling with google-perftools
If you want to enable profiling support, change the configure command above to the following:
$ LDFLAGS="-ltcmalloc -lprofiler" ./configure.developer
- (This also works for CFLAGS)
Step 3: Install Samba
To install Samba, run the following command in your Samba source directory:
$ make install
Note that this must be run as a user who has permission to write to the install directory, which defaults to /usr/local/samba. See Step 2: Compile Samba for instructions on how to change the install directory.
For the rest of this HOWTO we will assume that you have installed Samba in the default location. All future Samba commands will stem from the /usr/local/samba/sbin and /usr/local/samba/bin directories.
Please review the Release Notes for the version you have installed, it may contain important information not yet reflected in this HOWTO.
Upgrading
If you are upgrading from a previous release of Samba 4.x, be sure to review all the Release Notes for the new version, as well as the notes for all the interim versions.
To upgrade to the latest Samba 4.x version from a previous Samba 4.x release, you must first download the latest tarball or git tree. If using git, you may either do a full download of the latest git tree as described in the Downloading via git section, or you may upgrade your current git tree as described in the Updating via git section. Once you have obtained the latest version, simply run the following commands.
$ ./configure --enable-debug --enable-selftest $ make $ make install
For more information on the commands above and their associated options, please refer to Step 2
Step 4: Provision Samba
The provision step sets up a basic user database, and is used when you are setting up your Samba server in its own domain. If you instead want to setup your Samba server as an additional domain controller in an existing domain, then please see the Joining a Windows Domain Controller as an Additional DC in a Domain section on this page. If you want to migrate an existing Samba 3.x domain to Samba 4.0 as an AD DC, see the Migrating an Existing Samba 3 Domain to Samba 4 section on this page.
The provision step must be run as a user with permission to write to the install directory.
# /usr/local/samba/bin/samba-tool domain provision
This will run the provision tool interactively. For realm use something like samdom.example.com, for domain (it should suggest this) use samdom.
If you run the previous command with a user who does not have write permission to the install directory, you will get an error similar to this:
tdb_open_ex: could not open file /usr/local/samba/private/sam.ldb.d/DC=SAMDOM,DC=EXAMPLE,DC=COM. ldb: Permission denied
You can pass options to samba-tool domain provision command. You can run it with the --help option to see a list of them.
- Note: As of September 11, 2012 (Samba 4.0.0 RC1) the provision command now uses Samba's internal DNS server, if you would like the older behavior, add --dns-backend=BIND9_DLZ to the above provision command.
- Note: You may need to remove the /usr/local/samba/etc/smb.conf file if you are re-running the provision command.
- Note: If you use the --adminpass='password' switch, be aware that there are password complexity requirements, so if you are getting some odd error with provision, try a more complex password ie. 'Pa$$w0rd'
- Note: If you have a "password complexity" failure during domain provisionsing - read the following!
[I think the requirement is: at least one uppercase letter, and one number, and at least eight characters long.]
If you don't use a complex enough password, the provision script will bomb and re-running it will also bomb - because it doesn't know how to handle a partially provisioned setup.
A solution is: delete the ../samba directory. [Deleting only the smb.conf wasn't doing it, in my case.]
Thus, if you installed samba to the "default" location, do the following: rm /usr/local/samba/ -rf
Then run [make install] again to re-install the files.
Finally, run the domain provision again - with a better password.
Step 5: Starting Samba as an AD DC
If you are planning to run Samba as a production server, then just run the samba binary as root
# /usr/local/samba/sbin/samba
That will run Samba in 'standard' mode, which is suitable for production use. Samba doesn't yet have init scripts included for each platform, but making one for your platform should not be difficult. There are some example scripts (for RedHat/Fedora, Debian and Ubuntu) on the Samba4/InitScript page.
If you are running Samba as a developer you may find the following more useful:
# /usr/local/samba/sbin/samba -i -M single
This will start samba with all log messages printed to stdout, and restricting it to a single process. That mode of operation makes debugging samba with gdb easier. If you want to launch it under gdb, run samba as follows:
# gdb --args /usr/local/samba/sbin/samba -i -M single
Note that if you are running any Samba 3 smbd or nmbd processes they need to be stopped before starting samba from Samba 4.
Take care when running Samba commands if you also have a previous version of Samba installed. To avoid inadvertently running the wrong version, you should consider putting the /usr/local/samba/bin and /usr/local/samba/sbin directories in the beginning of your PATH variable.
You can see what version of Samba, if any, is in your PATH variable by running the following:
# samba -V
Step 6: Testing Samba as an AD DC
First check you have the right version of smbclient by running the following command:
$ /usr/local/samba/bin/smbclient --version
This should show you a version starting with "Version 4.0.XXXXX".
Now run this command to list the shares on your Samba server:
$ /usr/local/samba/bin/smbclient -L localhost -U%
The output of the command should be similar to what is shown below:
Sharename Type Comment
--------- ---- -------
netlogon Disk
sysvol Disk
IPC$ IPC IPC Service (Samba 4.0.0)
The netlogon and sysvol shares are basic shares needed for Active Directory server operation.
If the command failed, restart samba by running the following:
# killall samba # rm -v -- /usr/local/samba/var/run/smbd-fileserver.conf.pid # /usr/local/samba/sbin/samba
To test that authentication is working, you should try to connect to the netlogon share using the Administrator password you set earlier:
$ smbclient //localhost/netlogon -UAdministrator%'p4$$word' -c 'ls'
The output of the command should be similar to what is shown below:
Domain=[SAMDOM] OS=[Unix] Server=[Samba 4.0.0beta9-GIT-e4677e3] . D 0 Wed Sep 12 21:00:36 2012 .. D 0 Wed Sep 12 21:02:28 2012
Step 7: Configure DNS
A working DNS setup is essential to the correct operation of Samba. Without the right DNS entries, Kerberos won't work, which in turn means that many of the basic features of Samba won't work.
It is worth spending some extra time to ensure your DNS setup is correct, as debugging problems caused by mis-configured DNS can take a lot of time later on.
DNS Server
Samba's Internal DNS Server
If you specified --dns-backend=SAMBA_INTERNAL or did not specify any backend at all when you provisioned, there is no further setup required for the DNS server. However, you still need to configure your /etc/resolv.conf as shown in Configure /etc/resolv.conf
If you want the internal DNS server to forward requests it isn't responsible for, then add the following to your smb.conf:
dns forwarder = {IP-Address of the DNS you want to forward to}
Warning: If you are running X windows on your machine, networkmanager could be spawning dnsmasq, check the logs for lines like:
Failed to bind to 0.0.0.0:53 TCP - NT_STATUS_ADDRESS_ALREADY_ASSOCIATED
If you need to disable this you can open /etc/NetworkManager/NetworkManager.conf in your favorite editor as root, and comment out the line dns=dnsmasq, then restart network-manager
Bind 9.8.0 or newer
If using BIND, the next step to get a working DNS setup for Samba is to start with the DNS configuration file that is created by the provision step or if you are using any of the other samba-tool options (classicupgrade for example) you can specify --dns-backend=BIND9_DLZ or --dns-backend=BIND9_FLATFILE.
You can activate the configuration that the provision has created by including this configuration file in bind's named configuration file. This file is typically located in the /etc/bind directory, please refer to your distribution documentation for the location of this file on your system. Once located, add the following line to the configuration file:
include "/usr/local/samba/private/named.conf";
Edit that file to uncomment the correct dlz plugin line, based on your version of bind. Open the /usr/local/samba/private/named.conf file in a text editor and follow the instructions inside.
After adding that line you should restart your Bind server and check in the system logs for any problems. If available, you can run named-checkconf to help you fix any problems with your named configuration.
Bind 9.7.x
Users of bind-9.7.x are strongly encouraged to upgrade to bind-9.8 or bind-9.9. If this is not possible, refer to the section Configure Kerberos DNS Dynamic Updates for instructions on configuring bind-9.7.
Bind (All Versions)
A common problem you may encounter is that many modern Linux distributions activate 'Apparmor' or 'SELinux' by default, and these may be configured to deny access to Bind for your the named.conf and zone files created in the provision. If your Bind logs show that Bind is getting a access denied error accessing these files, please see your local system documentation for how to enable access to these files in Bind (hint: for Apparmor systems such as Ubuntu, the command aa-logprof may be useful).
- Note: On Debian systems, the zone auto-generation might detect and use 127.0.1.1 as the domain controller's IP address. This will cause problems when trying to connect to the server from client machines. To fix this, you will need to adjust /usr/local/samba/private/named.conf by changing 127.0.1.1 to reflect the actual IP address of the server you're setting up.
- Note: On Debian SID (bind9 package), /etc/bind/named.conf.options is missing and this will cause the named daemon to fail to start. To fix this either create an empty file, or comment out corresponding line in /etc/bind/named.conf. See your syslog messages for more information.
Configure /etc/resolv.conf
For all the local DNS lookups to resolve correctly, we need to modify the server's /etc/resolv.conf file. The following example should be sufficient to have DNS resolve properly:
domain samdom.example.com nameserver 192.168.1.2
- Note: Remember to change the IP Address to your Samba server's IP Address
- Note: If your server is set up to receive its IP configuration via DHCP, the /etc/resolv.conf file might be automatically updated. Refer to your distribution's documentation on how to stop this behavior.
Testing DNS
To test that DNS is working properly, run the following commands and compare the output to what is shown:
$ host -t SRV _ldap._tcp.samdom.example.com. _ldap._tcp.samdom.example.com has SRV record 0 100 389 samba.samdom.example.com.
$ host -t SRV _kerberos._udp.samdom.example.com. _kerberos._udp.samdom.example.com has SRV record 0 100 88 samba.samdom.example.com.
$ host -t A samba.samdom.example.com. samba.samdom.example.com has address 10.0.0.1
The answers you get should be similar to the ones above (adjusted for your DNS domain name and hostname). If you get any errors, carefully check your system logs to locate the problem.
Step 8: Configure Kerberos
Kerberos configuration is handled by the krb.conf file. This file is typically located in the /etc directory, please refer to your distribution documentation for the location of this file on your system. Replace the existing file, if any, with the sample from /usr/local/samba/share/setup/krb5.conf. Edit the file and replace ${REALM} with the value you chose for the --realm parameter of the provision command above, make sure to enter the realm in uppercase letters:
- Note: If you've already forgotten <gasp!> what Realm you supplied, you can find it in the smb.conf file. [for default installs that's /usr/local/samba/etc/smb.conf]
[libdefaults]
default_realm = SAMDOM.EXAMPLE.COM
dns_lookup_realm = false
dns_lookup_kdc = true
Testing Kerberos
The simplest test is to use the kinit command as follows:
$ kinit administrator@SAMDOM.EXAMPLE.COM Password:
- Note: You must specify your domain realm SAMDOM.EXAMPLE.COM in uppercase letters
kinit will not give you any output. [It may give you a password expiration notice.] To verify that Kerberos is working, and that you received a ticket, run the following:
$ klist Ticket cache: FILE:/tmp/krb5cc_1000 Default principal: administrator@SAMDOM.EXAMPLE.COM Valid starting Expires Service principal 02/10/10 19:39:48 02/11/10 19:39:46 krbtgt/SAMDOM.EXAMPLE.COM@SAMDOM.EXAMPLE.COM
If either kinit or klist do not exist on your system, refer to Samba_4_OS_Requirements on how to install the necessary packages.
You can also test Kerberos form a remote client, but you must first configure the client's krb5.conf and resolve.conf as shown previously.
- Note: If you are using a client behind NAT then you have to add the following to the krb5.conf on the domain controller server:
[kdc]
check-ticket-addresses = false
- Note: If provision generated you a password and you forgot it or didn't get it saved in some way, you can use "samba-tool user setpassword administrator" as root to reset it.
Step 9: Configure DNS Dynamic Updates via Kerberos
Samba has the capability to automatically update the bind zone files via Kerberos. While this step is optional, it is highly recommended. If you are using Samba's internal DNS server, no configuration is needed, and you can skip this step.
To setup dynamic DNS updates you need to have a recent version of bind installed. It is highly recommended that you install at least version 9.8.0 as that version includes a set of patches from the Samba Team to make dynamic DNS updates much more robust and easier to configure. In the instructions below we give instructions for both bind 9.7.2 and 9.8.0, but please use 9.8.0 or later if at all possible.
You can tell what version of bind you have using the command /usr/sbin/named -V. If your OS does not have bind-9.8.0 or later, then please consider getting it from a package provided by a 3rd party (for example, on Ubuntu there is a ppa available with the newer versions of bind).
Bind 9.8.0 or Later
When using bind-9.8.0 or later you need to add the following to the options section of your bind config:
options {
[...]
tkey-gssapi-keytab "/usr/local/samba/private/dns.keytab";
[...]
};
This file is typically located in the /etc/bind directory, please refer to your distribution documentation for the location of this file on your system.
Bind 9.7.x
If you have bind-9.7.x (specifically 9.7.2 or later), then first determine if you can at all possibly run bind-9.8. You will have far fewer problems. Otherwise, follow these instructions.
The Samba provision will have created a custom /usr/local/samba/private/named.conf.update configuration file. You need to include this file in your master named.conf to allow Samba/Kerberos DNS updates to automatically take place. Be advised that if you include this file in Bind versions that don't support it, Bind will fail to start.
You additionally need to set two environment variables when using bind-9.7.x:
KEYTAB_FILE="/usr/local/samba/private/dns.keytab" KRB5_KTNAME="/usr/local/samba/private/dns.keytab" export KEYTAB_FILE export KRB5_KTNAME
These should be put in your settings file for bind. On Debian based systems (including Ubuntu) this is in /etc/default/bind9. On RedHat and SUSE derived systems it is in /etc/sysconfig/named, please refer to your distribution documentation for the correct location to set these environment variables. Strictly speaking you only either need KEYTAB_FILE or KRB5_KTNAME, but which you need depends on your distribution, so it's easier to just set both.
The dns.keytab must be readable by the bind server process. Generally, this is accomplished by executing:
$ chown named:named /usr/local/samba/private/dns.keytab
(the provision should have setup these permissions for you automatically).
Finally, you need to add the following to the options section of your bind config:
options {
[...]
tkey-gssapi-credential "DNS/server.samdom.example.com";
tkey-domain "SAMDOM.EXAMPLE.COM";
[...]
};
The last part of the credential in the first line must match the dns name of the server you have set up. This file is typically located in the /etc/bind directory, please refer to your distribution documentation for the location of this file on your system.
Testing/Debugging Dynamic DNS Updates
The way the automatic DNS update in Samba works is that the provision will create a file /usr/local/samba/private/dns_update_list, which contains a list of DNS entries that Samba will try to dynamically update at startup and every 10 minutes thereafter using samba_dnsupdate utility. Updates will only happen if the DNS entries do not already exist. Remember that you need nsupdate utility from bind the distribution for all these to work.
If you want to test or debug this process, then please run this as root:
/usr/local/samba/sbin/samba_dnsupdate --verbose --all-names
The command line options specified will force an update of all records in the dns_update_list, as well as output detailed information on what is being done.
Interaction With Apparmor or SELinux
If you are using Apparmor or SELinux, you have to ensure that the bind process has read access to the /usr/local/samba/private/dns.keytab file, the /usr/local/samba/private/named.conf file as well as read-write access to the /usr/local/samba/private/dns directory and it's own zone file. The Samba provision tries to setup the permissions correctly for these files, but you may find you need to make changes in your Apparmor or SELinux configuration if you are running either of those. If you are using Apparmor then the aa-logprof command may help you add any missing permissions you need to add after you start Samba and bind for the first time after configuring them.
Please refer to Step 11: Permissions, SELinux Labeling and Policy for more information.
Step 10: Configure NTP (Optional)
You require a recent ntpd version (=>4.2.6) that supports signed ntp. E. g. the version shipped with RHEL6 and Ubuntu < 11.04 are to old. The Ntpd of Debian Squeeze supports signed ntp.
1a. Download ntpd from ntp.org (verify md5 sum) and compile it (add additionals ./configure parameters, if needed):
$ tar -zxvf ntp-4.x.x.tar.gz $ cd ntp-4.x.x $ ./configure --enable-ntp-signd $ make $ make install
1b. Set the permission of the ntp_signd directory (default /usr/local/samba/var/lib/ntp_signd/) to 0750 and its owner to root:ntp to ensure that it is readable from ntpd.
2a. If you already have a supported ntpd version and ntp.conf, you have to add/adjust only the following lines for minimal:
ntpsigndsocket /usr/local/samba/var/lib/ntp_signd/ restrict default mssntp
2b. If a minimal/simple ntp.conf is fine for you, then fill the file with the following:
server 127.127.1.0 fudge 127.127.1.0 stratum 12 ntpsigndsocket /usr/local/samba/var/lib/ntp_signd/ restrict default mssntp
2c. A more complex ntp.conf is the following:
server 127.127.1.0 fudge 127.127.1.0 stratum 10 server 0.pool.ntp.org iburst prefer server 1.pool.ntp.org iburst prefer driftfile /var/lib/ntp/ntp.drift logfile /var/log/ntp ntpsigndsocket /usr/local/samba/var/lib/ntp_signd/ restrict default kod nomodify notrap nopeer mssntp restrict 127.0.0.1 restrict 0.pool.ntp.org mask 255.255.255.255 nomodify notrap nopeer noquery restrict 1.pool.ntp.org mask 255.255.255.255 nomodify notrap nopeer noquery
For explanation: This config allows clients to receive time from this NTP host, localhost doesn't have any restrictions, and the servers we receive the time from ,are not allowed to do anything else than providing the time to us. For mor information about ntpd access controll, see http://support.ntp.org/bin/view/Support/AccessRestrictions
3. On members of the domain you don't have to configure anything. Per default they will receive the time from the DC that has the FSMO role PDC.
Step 11: Permissions, SELinux Labeling and Policy
These instructions are intended for RedHat 6.X, but may serve as a guide for other distributions/versions.
There is still more work to be done in regards of creating a Samba 4 specific SELinux policy but for now you should be able to have everything working without disabling SELinux.
For all the commands below, make sure you have set the following environment variable:
MYREALM="samdom.example.com"
Bind
Set Permissions:
chown named:named /usr/local/samba/private/dns chgrp named /usr/local/samba/private/dns.keytab chmod g+r /usr/local/samba/private/dns.keytab chmod 775 /usr/local/samba/private/dns
Label files:
chcon -t named_conf_t /usr/local/samba/private/dns.keytab
chcon -t named_conf_t /usr/local/samba/private/named.conf.update
chcon -t named_var_run_t /usr/local/samba/private/dns
chcon -t named_var_run_t /usr/local/samba/private/dns/${MYREALM}.zone
Set Label Persistence:
semanage fcontext -a -t named_conf_t /usr/local/samba/private/dns.keytab
semanage fcontext -a -t named_conf_t /usr/local/samba/private/named.conf
semanage fcontext -a -t named_conf_t /usr/local/samba/private/named.conf.update
semanage fcontext -a -t named_var_run_t /usr/local/samba/private/dns
semanage fcontext -a -t named_var_run_t /usr/local/samba/private/dns/${MYREALM}.zone
semanage fcontext -a -t named_var_run_t /usr/local/samba/private/dns/${MYREALM}.zone.jnl
semanage fcontext -a -t ntpd_t /usr/local/samba/var/run/ntp_signd
NTP
Set Permissions:
$ chgrp ntp /usr/local/samba/var/lib/ntp_signd
Multiple attempts to set the context for ntp failed so the below policy was needed for windows clients time sync after joining the DOMAIN.
$ chcon -u system_u -t ntpd_t /usr/local/samba/var/run/ntp_signd $ chcon -u system_u -t ntpd_t /usr/local/samba/var/run/ $ chcon -t ntpd_t /usr/local/samba/var/run/ntp_signd/socket
samba4.te policy:
module samba4 1.0;
require {
type ntpd_t;
type usr_t;
type initrc_t;
class sock_file write;
class unix_stream_socket connectto;
}
#============= ntpd_t ==============
allow ntpd_t usr_t:sock_file write;
#============= ntpd_t ==============
allow ntpd_t initrc_t:unix_stream_socket connectto;
Check and load policy:
$ checkmodule -M -m -o samba4.mod samba4.te $ semodule_package -o samba4.pp -m samba4.mod $ semodule -i samba4.pp
The provisioning will create a very simple /usr/local/samba/etc/smb.conf file with no non-system shares by default. For the server to be useful you, will need to update it to have at least one share. For example:
[test]
path = /data/test
comment = Test Share
read only = no
- Note: In older alpha versions of Samba 4, you need to restart Samba to make new shares visible.
You can share any printers already configured with CUPS, keep in mind that Samba communicates with CUPS via sockets, so you don't need to set any configure any special permissions beyond a listen directive for the CUPS socket.
Basic Print Sharing
- Create a print spool directory, and set the permissions properly. This is where Samba will store temporary files related to print documents:
mkdir /usr/local/samba/var/spool chmod 1777 /usr/local/samba/var/spool
- Configure samba to use it, by adding the following to /usr/local/samba/etc/smb.conf:
[printers]
comment = All Printers
path = /usr/local/samba/var/spool
browseable = Yes
read only = No
printable = Yes
Point and Print Drivers
For the sake of convenience, Windows clients can query the server that is sharing a printer for a print driver. To enable this functionality in Samba, we have to create a special print$ file share.
- Create the print file share directory, and architecture sub-directories:
mkdir -p /usr/local/samba/var/print/{COLOR,IA64,W32ALPHA,W32MIPS,W32PPC,W32X86,WIN40,x64}
- Configure samba to use it, by adding the following to /usr/local/samba/etc/smb.conf:
[print$]
comment = Point and Print Printer Drivers
path = /usr/local/samba/var/print
read only = No
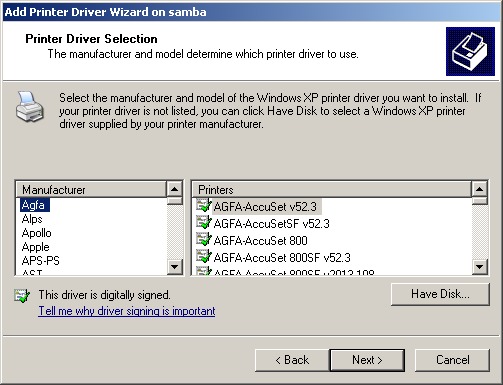
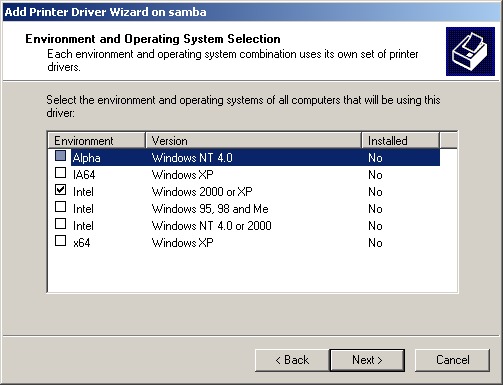
- Log in as a Domain Administrator on a client computer
- Click Start -> Run '\\samba\'
- In the list of shares, Double-Click 'Printers and Faxes'
- Click File -> Server Properties
- On the Drivers Tab, Click 'Add...', then 'Next'
- In the following prompts, choose the driver you would like to install, and click 'Next'
- Choose the architectures you are installing the drivers for. Be aware if you choose an architecture that the client computer does not have the driver for you will be prompted to provide a disk with the drivers.
- Close the Server Driver Dialog box
- Right-click on the printer the driver is for and choose Properties
- On the Advanced tab, change the Driver drop-down box to the driver you just installed
Note: Filesystem Support
This information has been included in the Samba_4_OS_Requirements#File_System_Support
Configure a Windows Client to join a Samba 4 Active Directory
Active Directory is a powerful administration service which enables an Administrator to centrally manage a network of Windows 2000, Windows XP Pro, Windows 2003, Windows Vista Business Edition, and Windows 7 Professional (and up) effectively. To test the real Samba capability, we use Windows XP Pro as testing environment (Windows XP Home doesn't include Active Directory functionality and won't work).
To allow Samba 4 Active Directory or Microsoft Active Directory to manage a computer, we need to join the computer into the active directory. It involves:
- Configuring DNS Settings
- Configuring Date & Time and Time Zone
- Joining the domain
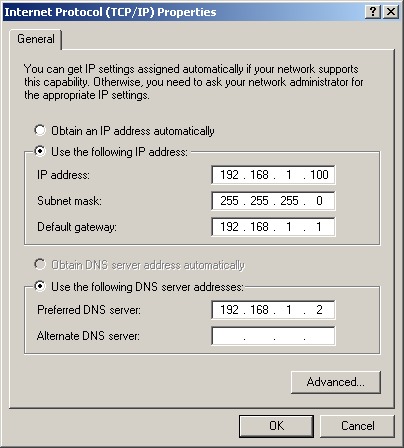
Step 1: Configure DNS Setting for Windows
Before we configure the DNS settings, verify that you are able to ping the server's IP address. If you are not able to ping the server, double check your IP address, firewall, routing, etc.
Once you have verified network connectivity between the Samba server and client,
- Right Click My Network Places, Select Properties
- Right Click Local Area Network, Select Properties
- Double click TCP/IP
- Use a static DNS server, add the Samba server's IP address inside the Primary DNS Server Column.
- Press OK on all opened windows.
- Open a command prompt, type 'ping samdom.example.com' (as per your provision).
If you get replies, then it means that your Windows settings are correct for DNS, and the Samba server's DNS service is working as well.
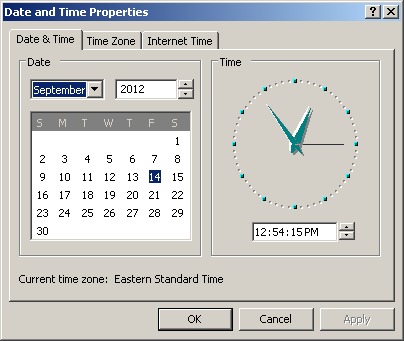
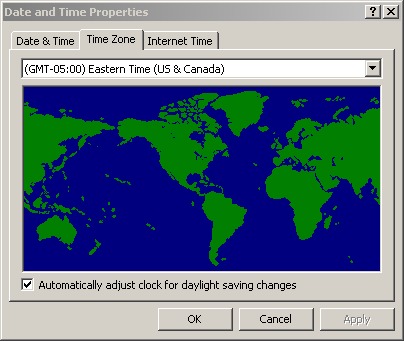
Step 2: Configure Date & Time and Time Zone
Active Directory uses Kerberos as the backend for authentication. Kerberos requires that the system clocks on the client and server be synchronized to within a few seconds of each other. If they are not synchronized, then authentication will fail for apparently no reason.
Configure the Date & Time
- Right-Click on the Time display in the system notification area, Select Adjust Date/Time.
- Change the Date and Time so the client matches the server to the minute, and click OK
Configure the Time Zone
- Right-Click on the Time display in the system notification area, Select Adjust Date/Time.
- Click on the Time Zone Tab
- Change the Time Zone to match the Time Zone on the server.
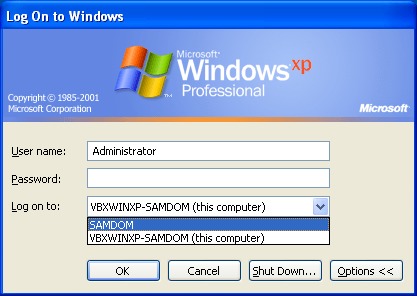
Step 3: Joining Windows Clients to the Domain
Now your Windows computer is ready to join the Active Directory (AD) domain,
As an Administrator:
- Right Click My Computer -> Properties
- Choose the Computer Name tab, click Change...
- Click option 'Domain', insert SAMDOM.EXAMPLE.COM. If this fails, try SAMDOM.
- When it requests a username and password, type Administrator as the username, and p4$$word as the password.
- You should get a message box stating "Welcome to the SAMDOM.EXAMPLE.COM domain."
- Click OK on this message box and the Properties window, and you will be instructed to restart your computer.
- After restarting, you should be presented with the normal logon dialog.
- Change the domain to SAMDOM and type Administrator as the username, and p4$$word as the password.
Viewing Samba 4 Active Directory object from Windows
We need install Windows 2003 Adminpak into Windows XP in order to use GUI tools to manage the domain. Before you begin, make sure that the domain administrators have administrative rights to control your computer.(To give any user administrative rights in Windows XP Pro, right click My Computer, select Manage-> choose Groups-> double click Administrators and add members from domain into the member list. When you add members from Active Directory, it will prompt you to enter an Active Directory username and password).
Step 1: Installing Windows Remote Administration Tools onto Windows
Windows 8/7/Vista
- Download the Windows Remote Administration Tools from:
- http://www.microsoft.com/download/details.aspx?id=28972 (Windows 8)
- http://www.microsoft.com/downloads/details.aspx?FamilyId=9FF6E897-23CE-4A36-B7FC-D52065DE9960&displaylang=en (Vista)
- http://www.microsoft.com/downloads/details.aspx?FamilyID=7D2F6AD7-656B-4313-A005-4E344E43997D&displaylang=en (Windows 7)
- Follow the "Install RSAT" instructions (Just a note: After installing, you have to enable the features in "Turn Windows features on or off" in "Programs" of the Control Panel!).
Windows XP Pro
Administration Tools Pack & Support Tools
- Download adminpak and supporttools from:
- http://www.microsoft.com/downloads/en/details.aspx?FamilyID=86b71a4f-4122-44af-be79-3f101e533d95
- http://download.microsoft.com/download/3/e/4/3e438f5e-24ef-4637-abd1-981341d349c7/WindowsServer2003-KB892777-SupportTools-x86-ENU.exe
- If you installed an older version of the adminpak, you'll notice the dial-in tab is missing from property pages. Just follow the link above to get SP2 which does not have this issue.
- Run through the installation.
- Press start->run, type 'dsa.msc', if a window 'active directory users and computers' prompt up, it mean you had install adminpak it successfully. You can also find this at Start>Programs>Administrative Tools, which should have a lot more items now.
- Go to c:\Program Files\Support Tools to check whether the support tools were installed correctly; if yes, then your XP workstation is ready to manage the Samba 4 Active Directory.
Group Policy Management Console
- You may also find the Group Policy Management Console useful. You can download it from
- This is primarily useful when you have larger installs and are managing many machines. You may need to download the .NET Framework first.
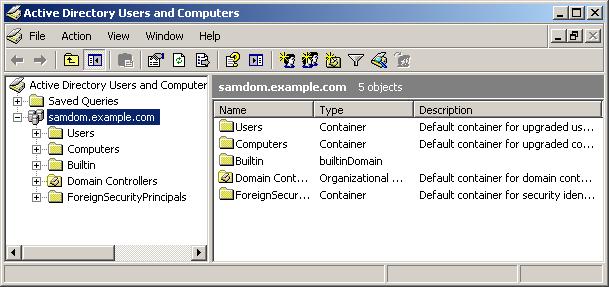
Step 2: Viewing Samba Active Directory Content
- When logged on as a Domain Administrator, start the Active Directory Users and Computers Snap-In, either by clicking Start -> Programs\Administrative Tools\Active Directory Users and Computers, or by clicking Start -> Run 'dsa.msc'
- Expand the samdom.example.com tree to see existing objects in the domain.
Managing Samba 4 Active Directory From a Windows Client
One of Samba 4's goals is to integrate with (and replace) Active Directory as a system. At this point, if everything has worked correctly you should have an "Administrative Tools" menu under Programs. If, under Administrative Tools you have "Active Directory Users and Computers", that is a very good sign. Most times, if there is a configuration or bug in Samba, the AD Users & Computers (among other interfaces) won't show up as an option. You can run it by hand (Start->Run->dsa.msc) but it's unlikely to work correctly.
Step 1: Adding Users into Samba 4 Active Directory
Unlike Samba 3, Samba 4 does not require a local Unix user for each Samba user that is created.
To create a Samba user, use the following command:
/usr/local/samba/bin/samba-tool user add USERNAME
To inspect the allocated user ID and SID, use the following command:
$ /usr/local/samba/bin/wbinfo --name-to-sid USERNAME S-1-5-21-4036476082-4153129556-3089177936-1005 SID_USER (1) $ /usr/local/samba/bin/wbinfo --sid-to-uid S-1-5-21-4036476082-4153129556-3089177936-1005 3000011
If you want to change this mapping, then use ldbedit on the /usr/local/samba/private/idmap.ldb, as shown:
$ ldbedit -e emacs -H /usr/local/samba/private/idmap.ldb objectsid=S-1-5-21-4036476082-4153129556-3089177936-1005
- Note: You can replace emacs with your editor of choice.
You will find records that look like this:
# record 1 dn: CN=S-1-5-21-4036476082-4153129556-3089177936-1005 cn: S-1-5-21-4036476082-4153129556-3089177936-1005 objectClass: sidMap objectSid: S-1-5-21-4036476082-4153129556-3089177936-1005 type: ID_TYPE_BOTH xidNumber: 3000011 distinguishedName: CN=S-1-5-21-4036476082-4153129556-3089177936-1005
If you change the xidNumber attribute and save your editor then exit, then Samba will update the mapping to between the SID and the user ID. Updating group mappings works in the same way.
- Note: You can also manage users using the normal Windows AD user management tools.
Setting Up Roaming Profiles
1. You will need to create a share for the profiles, typically named profiles. Edit the /usr/local/samba/etc/smb.conf to include:
[profiles]
path = /usr/local/samba/var/profiles
read only = no
2. Create the directory above using:
$ sudo mkdir /usr/local/samba/var/profiles
3. In Windows, start Active Directory Users and Computers, select all the users, right click, and hit properties
4. Under the profile tab, in the Profile path, type the path to your share along with %USERNAME% as follows:
\\sambaserver.samdom.example.com\profiles\%USERNAME%
5. click OK, logout and login as one of those users. When you logout again, you should see that the profile has been synced onto the samba server.
- Note: An excellent walk-through on configuring Roaming Profiles and Folder Redirection is available here.
Adding Organization Units (OU) Into a Samba Domain
The Organizational Unit (OU) is a powerful feature in Active Directory. This is a type of container which allows you to drag & drop users and/or computers into it.
We can link several types of group policies to an OU, and the settings will push out to all users/computers that sit under the OU. Withing a single domain, you can have as many OUs and sub-OUs as you'd like. The result is that it can greatly reduce administrative overhead since you are able to manage everything via an OU. The implementation of Group Policy will be discussed in the next chapter.
Before we create an OU, we must know what one looks like. By default we can see a sample OU called 'Domain Controllers', which uses a different icon in the Windows management tools than the 'users' and 'computers' containers. We can deploy Group Policy to the users or the computers container.
- To create an OU as the Domain Administrator, click Start -> Run -> dsa.msc
- Right click your domain.
- Select New -> Organizational Unit
- Type 'OU Demo'
- You will see a new OU appear, with the name 'OU Demo'.
- You can drag the user 'demo' into the new OU (Don't move other users! Unless you want to get stuck!).
- Right click 'OU Demo', A sub-OU can be created with New -> Organizational Unit.
Normally OUs are created according to the department setup of your organization. Be careful not to confuse Groups and OUs. Groups are used to control permissions, OUs are used for deploying settings to all users/computers within the OU.
Implementing Group Policies (GPO) in A Samba Domain
Samba Active Directory has support for Goup Plicies, and can create the Goup Plicy on the fly. The basic idea of Goup Plicies is:-
- Group Policies have two kinds of settings: computers and users.
- Computer settings apply to computers, while user settings apply to users.
- We link the group policy to a particular OU, and the group policy will effect all computers/users under the OU.
- To add a group policy, right click 'OU Demo' OU->properties.
- Choose group policy.
- Press new, and name it as 'GP Demo'.
- Press edit to modify the policy.
- Here will demonstrate how to block users from access to the control panel. Open the tree 'User Configuration'->'Administrative Templates'->'Control Panel'.
- Double click on 'Prohibit access to the Control Panel'.
- Press enabled and then press OK. Now the all users under 'OU Demo' won't able to access to the control panel.
- Make sure that the user 'demo' is inside the 'OU Demo' (You can drag and drop it).
- Logout and login as user 'demo'.
- You'll find user demo is not able to access control panel.
Notes
- User configuration will take effect once you logout and login.
- Computer configuration will take effect when you restart the computer.
- GPO Password Policies are not read by Samba when assigning passwords, to change the policy that Samba uses you must use samba-tool domain passwordsettings
To learn more about managing and implementing organizational units, group policies, and Active Directory, try a web search for Google in Windows 2003 Active Directory implementation.
Joining a Windows Domain Controller as an Additional DC in a Domain
Once you have a Samba domain controller set up, you can choose to join additional domain controllers to the domain, whether they be additional Samba domain controllers, or additional Windows domain controllers.
If you wish to join an additional Samba domain controller to a domain, then please see the Joining a domain as a DC page. The instructions on that page are the same for joining Samba to a Windows domain as they are for joining Samba to an existing Samba domain.
If you wish to join a new Windows domain controller to a Samba domain, then you should use the 'dcpromo' tool on the Windows machine. Please see the normal instructions for installing dcpromo on Windows, with the exception that you should not check the 'DNS server' option box when it is offered. Right now you should either use Windows for DNS, or use Samba and bind9 for DNS. Mixing the two can work, but it is an advanced topic that is beyond the scope of this howto.
Migrating an Existing Samba Domain to Samba
It is very likely that you already have a running Samba3 domain on your network. The question is, how do you migrate that domain and all of its users and machines over to a new Samba 4 based domain without having to move every user profile and machine to the new domain? The answer is the samba-tool domain classicupgrade function.
Connecting other services to your new/migrated Active Directory
If you finished setting up or migrating to Samba 4, you maybe want to connect other services to your new Active Directory. Have a look at the Beyond Samba page.
Report Your Success/Failure!
Samba, as a replicating domain controller, is still developing rapidly. We'd like to hear from users about their successes and failures. We would encourage you to report both your successes and failures to the samba-technical mailing list on http://lists.samba.org