Joining a Windows Server 2012 / 2012 R2 DC to a Samba AD: Difference between revisions
Mmuehlfeld (talk | contribs) (Rewrote Windows Server 2012/2012 R2 DC to a Samba AD) |
m (→Warning) |
||
| (14 intermediate revisions by one other user not shown) | |||
| Line 1: | Line 1: | ||
= Introduction = |
= Introduction = |
||
Samba |
Samba supports Active Directory (AD) schema version 56 and 67. This enables you to join Windows Server 2012 and 2012 R2 to your Samba AD. However, you cannot join the first Windows Server 2012 or 2012 R2 domain controller (DC) directly, because the process uses the Windows management instrumentation (WMI) protocol for several tasks. To work around the problem, you require a Windows Server 2008 or 2008 R2 DC in the domain to join the first 2012 or 2012 R2 DC. After the first Windows Server 2012 or 2012 R2 DC was joined, you can this one as replication partner when joining further Windows DCs. |
||
{{Imbox |
|||
'''Windows Server 2012 and 2012 R2 as a DC, and the directory schemas 56 and 67 are experimental.''' If you encounter a bug, please report at https://bugzilla.samba.org. |
|||
| type = important |
|||
| text = The support for Windows Server 2012 and 2012 R2 DCs, including the directory schemas 56 and 67, is experimental. Please report bugs an incompatibilites. For details, see [[Bug Reporting]]. |
|||
}} |
|||
| Line 11: | Line 14: | ||
= Warning = |
= Warning = |
||
{{Imbox |
|||
'''Joining a Windows Server 2012 or 2012 R2 DC to a Samba AD breaks the AD replication! Do not use this documentation until the problem is fixed!''' |
|||
| type = warning |
|||
For more details, see [https://bugzilla.samba.org/show_bug.cgi?id=12204 Bug #12204]. |
|||
| text = Joining a Windows Server 2012 or 2012 R2 DC to a Samba AD breaks the AD replication! Do not use this documentation until the problem is fixed!<br />For more details, see [https://bugzilla.samba.org/show_bug.cgi?id=13618 Bug #13618] and [https://bugzilla.samba.org/show_bug.cgi?id=13619 Bug #13619]. |
|||
}} |
|||
= Requirements and Known Limitations = |
|||
* All Samba DCs must run 4.6 or later. For details about updating Samba, see [[Updating_Samba|Updating Samba]]. |
|||
* Windows Server 2012 and 2012 R2 requires the Windows management instrumentation (WMI) protocol during the join, and for the forest and domain preparation. Samba currently does not support this protocol. Therefore you must run a Windows domain controller (DC) with WMI support in your domain. For example, you can a Windows Server 2008 or 2008 R2 DC as replication partner during the join. |
|||
* The Windows Server 2008 or 2008 R2 host used for the initial replication must provide a <code>Sysvol</code> share. For details, see [[Enabling the Sysvol Share on a Windows DC]]. |
|||
: If the <code>Sysvol</code> share is missing, joining a Windows Server 2012 or 2012 R2 DC fails. |
|||
= Requirements and Known Limitations = |
|||
* All Samba DCs must run 4.5.0 or later. For information about updating, see [[Updating_Samba|Updating Samba]]. |
|||
* Windows Server 2012 and 2012 R2 requires the Windows management instrumentation (WMI) protocol during the join, and for the forest and domain preparation. Samba currently does not support this protocol. Thus you must have an existing Windows domain controller (DC) with WMI support in your domain. For example, you can a Windows Server 2008 or 2008 R2 DC as replication partner during the join. For further information, see [[Joining_a_Windows_Server_2008_/_2008_R2_DC_to_a_Samba_AD|Joining a Windows Server 2008 / 2008 R2 DC to a Samba AD]]. |
|||
| Line 30: | Line 34: | ||
= Network Configuration = |
= Network Configuration = |
||
* Click the |
* Click the <code>Start</code> button, search for <code>View network connections</code>, and open the search entry. |
||
* Right-click to your network adapter and select |
* Right-click to your network adapter and select <code>Properties</code>. |
||
* Configure the IP settings: |
* Configure the IP settings: |
||
| Line 38: | Line 42: | ||
:* Enter the IP of a DNS server that is able to resolve the Active Directory (AD) DNS zone. |
:* Enter the IP of a DNS server that is able to resolve the Active Directory (AD) DNS zone. |
||
* Click |
* Click <code>OK</code> to save the settings. |
||
| Line 50: | Line 54: | ||
Before you join the domain, check the time configuration: |
Before you join the domain, check the time configuration: |
||
* Open the |
* Open the <code>Control Panel</code>. |
||
* |
* Navigate to <code>Clock, Language and Region</code>. |
||
* Click |
* Click <code>Date and Time</code>. |
||
* Verify the date, time, and time zone settings. Adjust the settings, if necessary. |
* Verify the date, time, and time zone settings. Adjust the settings, if necessary. |
||
* Click |
* Click <code>OK</code> to save the changes. |
||
| Line 66: | Line 70: | ||
= FSMO Roles = |
= FSMO Roles = |
||
When you join the first Windows Server 2012 or 2012 R2 host as a domain controller (DC) to an Active Directory (AD) |
When you join the first Windows Server 2012 or 2012 R2 host as a domain controller (DC) to an Active Directory (AD), the directory schema of the forest and domain is updated. You must run this process on an existing Windows 2008 or 2008 R2 domain controller (DC) that owns the following flexible single master operation (FSMO) roles: |
||
* Schema Master |
* Schema Master |
||
* Infrastructure Master |
* Infrastructure Master |
||
* PDC Emulator |
|||
For details about transfering FSMO roles, see [[Transferring_and_Seizing_FSMO_Roles#Windows_FSMO_Role_Management|Transferring and Seizing FSMO Roles]]. |
|||
If you successfully updated the schema during the first Windows Server 2012 or 2012 R2 join, you can later transfer the roles to a Samba DC again. |
|||
'''Note that this is a necesary requirement and the forest or domain preparation fails if a Samba DC holds one or both roles during the first Windows Server 2012 or 2012 R2 DC is joined!''' |
|||
After the forest and domain schema was updated, you can optionally transfer the FSMO roles back to a Samba DC. |
|||
{{Imbox |
|||
| type = important |
|||
| text = Forest and domain preparation fails if a Samba DC holds one to three of the previous mentioned roles when you join the first Windows Server 2012 or 2012 R2 DC. |
|||
}} |
|||
| Line 85: | Line 91: | ||
= Installing the Active Directory Domain Services = |
= Installing the Active Directory Domain Services = |
||
* Start the |
* Start the <code>Server Manager</code>. |
||
* Click |
* Click <code>Add roles and features</code>. |
||
* Select |
* Select <code>Role-based or feature-based installation</code> and click <code>Next</code>. |
||
* Click |
* Click <code>Select a server from the server pool</code> and select the local Windows Server from the list. Click <code>Next</code>. |
||
* Select |
* Select <code>Active Directory Domain Services</code>, including all dependencies. Click <code>Next</code>. |
||
* You do not need to select any additional features. Click |
* You do not need to select any additional features. Click <code>Next</code>. |
||
* Start the installation. |
* Start the installation. |
||
* Click |
* Click <code>Close</code>. |
||
| Line 109: | Line 115: | ||
* Log in to your Windows Server 2012 or 2012 installation using the local administrator account. |
* Log in to your Windows Server 2012 or 2012 installation using the local administrator account. |
||
* Start the |
* Start the <code>Server Manager</code>. |
||
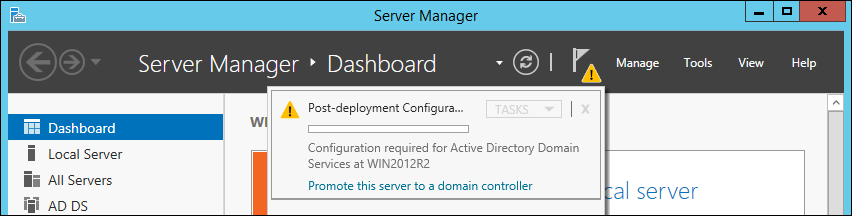
* Click the notifier icon on the top navigation bar and click |
* Click the notifier icon on the top navigation bar and click <code>Promote this server to a domain controller</code>. |
||
:[[Image:Join_Win2012R2_Server_Manager_Post_Deployment.png]] |
:[[Image:Join_Win2012R2_Server_Manager_Post_Deployment.png]] |
||
* Select |
* Select <code>Add a domain controller to an existing domain</code>, enter the Samba Active Directory (AD) domain name and credentials that are enabled to join a domain controller (DC) to the domain, like the domain administrator account. Click <code>Next</code>. |
||
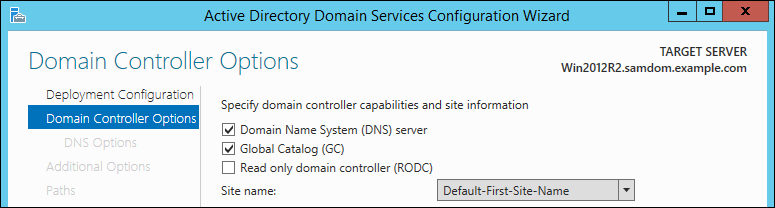
* Select the options to enable on the new DC and enter the directory services restore mode (DSRM) password. It is required to boot the Windows DC in safe-mode to restore or repair the AD in case of problems. Click |
* Select the options to enable on the new DC and enter the directory services restore mode (DSRM) password. It is required to boot the Windows DC in safe-mode to restore or repair the AD in case of problems. Click <code>Next</code>. |
||
:[[Image:Join_Win2012R2_DS_Wizzard_Page2.png]] |
:[[Image:Join_Win2012R2_DS_Wizzard_Page2.png]] |
||
* If you enabled the |
* If you enabled the <code>DNS server</code> option in the previous step, you may see a note, that a delegation for this DNS server cannot be created. Click <code>Next</code>. |
||
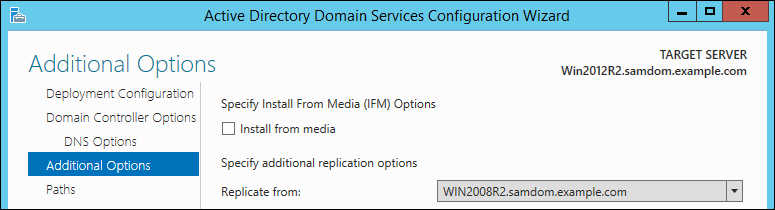
* Samba currently does not support schema replication using the Windows management instrumentation (WMI) protocol. For this reason, select an existing Windows Domain Controller in the domain as replication source and click |
* Samba currently does not support schema replication using the Windows management instrumentation (WMI) protocol. For this reason, select an existing Windows Domain Controller in the domain as replication source and click <code>Next</code>. |
||
:[[Image:Join_Win2012R2_DS_Wizzard_Page3.png]] |
:[[Image:Join_Win2012R2_DS_Wizzard_Page3.png]] |
||
* Set the folders for the AD database, log files and the Sysvol folder. Click |
* Set the folders for the AD database, log files and the Sysvol folder. Click <code>Next</code>. |
||
* Click |
* Click <code>Next</code> to confirm the operations, Windows is going to perform. |
||
* Verify your settings and click |
* Verify your settings and click <code>Next</code> to start the prerequisite check. |
||
* Windows runs some prerequisites checks. If |
* Windows runs some prerequisites checks. If errors are displayed, fix them before you continue. Click <code>Install</code>. |
||
* Windows promotes the server to a DC. If it is the first Windows Server 2012 or 2012 R2 DC, the forest and domain schema is automatically updated. |
|||
* The DC promotions begins. |
|||
: {{Imbox |
|||
| type = warning |
|||
| text = This step breaks the AD directory replication! For details, see [[#Warning|Warning]]. |
|||
}} |
|||
* If the wizard completes successfully, the Windows server is restarted automatically. |
|||
: If this is the first Windows Server 2012 or 2012 R2 DC in your AD forest: |
|||
: '''Warning: This step breaks the AD directory replication!''' For more details, see [[#Warning|Warning]]. |
|||
: The installation wizzard is only able to run the AD forest preparation. The domain preparation step fails. To work around: |
|||
* Verify that all DC related DNS records have been created during the promotion. See [[Verifying and Creating a DC DNS Record|Verifying and Creating a DC DNS Record]]. |
|||
:* Log in using the domain administrator account to your existing Windows Server 2008 or 2008 R2 installation that owns the "Schema Master" and the "Infrastructure Master" flexible single master operation (FSMO) role. |
|||
:{{Imbox |
|||
| type = important |
|||
| text = Do not continue without checking the DNS records. They must exist for a working directory replication! |
|||
}} |
|||
:* Insert the Windows Server 2012 or Windows 2012 R2 installation DVD. |
|||
:* Open a command line and change to the "support\adprep" folder on the installation DVD. For example, if you DVD drive is "D": |
|||
> D: |
|||
> cd support\adprep\ |
|||
:* Start the domain preparation: |
|||
= Verifying Directory Replication = |
|||
> adprep /domainprep |
|||
See [[Verifying_the_Directory_Replication_Statuses#Displaying_the_Replication_Statuses_on_a_Windows_DC|Displaying the Replication Statuses on a Windows DC]]. |
|||
:* You see the following message if the preparation succeeds: |
|||
{{Imbox |
|||
Adprep successfully updated the domain-wide information. |
|||
| type = note |
|||
| text = To optimize replication latency and cost, the knowledge consistency checker (KCC) on Windows DCs do not create a fully-meshed replication topology between all DCs. For further details, see [[The Samba KCC]]. |
|||
}} |
|||
:* Restart the [[#Joining_the_Windows_Server_to_the_Domain|Joining the Windows Server to the Domain]] process. |
|||
* If the wizzard completes successfully, the Windows server is restarted automatically. |
|||
* Verify that all DC related DNS records have been created during the promotion. See [[Verifying and Creating a DC DNS Record|Verifying and Creating a DC DNS Record]]. |
|||
: '''Do not continue without checking the DNS records. They must exist for a working directory replication!''' |
|||
= The Sysvol Share = |
|||
== Enabling the Sysvol Share == |
|||
If you used a Samba domain controller (DC) as replication partner, the <code>Sysvol</code> share is not enabled. For details how to verify and enable the share, see [[Enabling the Sysvol Share on a Windows DC]]. |
|||
= Verifying the Directory Replication = |
|||
A few minutes after the domain controller (DC) started, the connections with all other DCs are automatically established and the replication begins. |
|||
== Sysvol Replication == |
|||
To verify the directory replication, run on a Samba DC: |
|||
Samba currently does not support the DFS-R protocol required for Sysvol replication. Please manually synchronise the content between domain controllers (DC) or use a workaround such as [[Robocopy_based_SysVol_replication_workaround|Robocopy-based Sysvol Replication]]. |
|||
# samba-tool drs showrepl |
|||
Default-First-Site-Name\SAMBADC |
|||
DSA Options: 0x00000001 |
|||
DSA object GUID: 4a6bd92a-6612-4b15-aa8c-9ec371e8994f |
|||
DSA invocationId: 96bc0d6f-9cea-4011-b9a1-0e9971009b20 |
|||
==== INBOUND NEIGHBORS ==== |
|||
DC=DomainDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ NTTIME(0) was successful |
|||
0 consecutive failure(s). |
|||
Last success @ NTTIME(0) |
|||
DC=DomainDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2012R2DC via RPC |
|||
DSA object GUID: fb03f58b-1654-4a02-8e11-f0ea120b60cc |
|||
Last attempt @ NTTIME(0) was successful |
|||
0 consecutive failure(s). |
|||
Last success @ NTTIME(0) |
|||
DC=ForestDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ NTTIME(0) was successful |
|||
0 consecutive failure(s). |
|||
Last success @ NTTIME(0) |
|||
DC=ForestDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2012R2DC via RPC |
|||
DSA object GUID: fb03f58b-1654-4a02-8e11-f0ea120b60cc |
|||
Last attempt @ NTTIME(0) was successful |
|||
0 consecutive failure(s). |
|||
Last success @ NTTIME(0) |
|||
DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:35:09 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:09 2014 CET |
|||
DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2012R2DC via RPC |
|||
DSA object GUID: fb03f58b-1654-4a02-8e11-f0ea120b60cc |
|||
Last attempt @ Sat Dec 20 10:35:09 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:09 2014 CET |
|||
CN=Schema,CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:35:10 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:10 2014 CET |
|||
CN=Schema,CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2012R2DC via RPC |
|||
DSA object GUID: fb03f58b-1654-4a02-8e11-f0ea120b60cc |
|||
Last attempt @ Sat Dec 20 10:35:10 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:10 2014 CET |
|||
CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:35:11 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:11 2014 CET |
|||
CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2012R2DC via RPC |
|||
DSA object GUID: fb03f58b-1654-4a02-8e11-f0ea120b60cc |
|||
Last attempt @ Sat Dec 20 10:35:11 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:11 2014 CET |
|||
==== OUTBOUND NEIGHBORS ==== |
|||
DC=DomainDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:35:17 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:17 2014 CET |
|||
DC=DomainDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2012R2DC via RPC |
|||
DSA object GUID: fb03f58b-1654-4a02-8e11-f0ea120b60cc |
|||
Last attempt @ Sat Dec 20 10:35:17 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:17 2014 CET |
|||
DC=ForestDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:35:17 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:17 2014 CET |
|||
DC=ForestDnsZones,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2012R2DC via RPC |
|||
DSA object GUID: fb03f58b-1654-4a02-8e11-f0ea120b60cc |
|||
Last attempt @ Sat Dec 20 10:35:17 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:35:17 2014 CET |
|||
DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:34:26 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:34:26 2014 CET |
|||
DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2012R2DC via RPC |
|||
DSA object GUID: fb03f58b-1654-4a02-8e11-f0ea120b60cc |
|||
Last attempt @ Sat Dec 20 10:34:26 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:34:26 2014 CET |
|||
CN=Schema,CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:34:26 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:34:26 2014 CET |
|||
CN=Schema,CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2012R2DC via RPC |
|||
DSA object GUID: fb03f58b-1654-4a02-8e11-f0ea120b60cc |
|||
Last attempt @ Sat Dec 20 10:34:26 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:34:26 2014 CET |
|||
CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2008R2DC via RPC |
|||
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9 |
|||
Last attempt @ Sat Dec 20 10:34:21 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:34:21 2014 CET |
|||
CN=Configuration,DC=samdom,DC=example,DC=com |
|||
Default-First-Site-Name\Win2012R2DC via RPC |
|||
DSA object GUID: fb03f58b-1654-4a02-8e11-f0ea120b60cc |
|||
Last attempt @ Sat Dec 20 10:34:21 2014 CET was successful |
|||
0 consecutive failure(s). |
|||
Last success @ Sat Dec 20 10:34:21 2014 CET |
|||
==== KCC CONNECTION OBJECTS ==== |
|||
Connection -- |
|||
Connection name: f55bce90-d458-400a-a4ca-801c3e64bef3 |
|||
Enabled : TRUE |
|||
Server DNS name : Win2008R2DC.samdom.example.com |
|||
Server DN name : CN=NTDS Settings,CN=Win2008R2DC,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com |
|||
TransportType: RPC |
|||
options: 0x00000001 |
|||
Warning: No NC replicated for Connection! |
|||
Connection -- |
|||
Connection name: fb03f58b-1654-4a02-8e11-f0ea120b60cc |
|||
Enabled : TRUE |
|||
Server DNS name : Win2012R2DC.samdom.example.com |
|||
Server DN name : CN=NTDS Settings,CN=Win2012R2DC,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com |
|||
TransportType: RPC |
|||
options: 0x00000001 |
|||
Warning: No NC replicated for Connection! |
|||
It can take several minutes until all connections are established. If the connections on existing Samba DCs to the Windows DC are not established within 15 minutes, start the replication manually. For details, see [[Samba-tool_drs_replicate|samba-tool drs replicate]]. |
|||
If you are seeing the warning "No NC replicated for Connection!", see [[FAQ#Message:_Warning:_No_NC_replicated_for_Connection.21|FAQ: Warning: No NC replicated for Connection!]]. |
|||
== Testing the Directory Replication == |
|||
To test that the directory replication works correctly, add for example a user on an existing DC and verify that it shows up automatically on the new promoted Windows DC. |
|||
= The Sysvol Share = |
|||
During the join, Windows tries to replicate the Sysvol directory content from an existing domain controller (DC). Samba currently does not support the DFS-R protocol. For this reason, the new DC may not show a "Sysvol" share. To enable the share: |
|||
* Save the following content to a plain text file named "Win-Create-Sysvol-Share.reg" using a text editor like "Notepad" or "Editor" (not Word/Wordpad/OpenOffice/LibreOffice/etc.): |
|||
= Troubleshooting = |
|||
Windows Registry Editor Version 5.00 |
|||
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Netlogon\Parameters] |
|||
"SysvolReady"=dword:00000001 |
|||
== Error: <code>This operation is only allowed for the Primary Domain Controller of the domain</code> == |
|||
* Log in using an account that is member of the local "Administrators" group. |
|||
Windows displays this error if it fails to access the <code>Sysvol</code> on the Windows Server 2008 or 2008 R2 replication partner. For details, see [[Enabling the Sysvol Share on a Windows DC]]. |
|||
* Double-click the file to import it to the Windows registry. |
|||
* Reboot to take the changes effect. |
|||
== Sysvol replication == |
|||
---- |
|||
Samba currently does not support the DFS-R protocol required for Sysvol replication. Please manually synchronise the content between DC or use a workaround like [[Robocopy_based_SysVol_replication_workaround|Robocopy-based Sysvol Replication]]. |
|||
[[Category:Active Directory]] |
|||
[[Category:Domain Control]] |
|||
Revision as of 15:42, 14 September 2018
Introduction
Samba supports Active Directory (AD) schema version 56 and 67. This enables you to join Windows Server 2012 and 2012 R2 to your Samba AD. However, you cannot join the first Windows Server 2012 or 2012 R2 domain controller (DC) directly, because the process uses the Windows management instrumentation (WMI) protocol for several tasks. To work around the problem, you require a Windows Server 2008 or 2008 R2 DC in the domain to join the first 2012 or 2012 R2 DC. After the first Windows Server 2012 or 2012 R2 DC was joined, you can this one as replication partner when joining further Windows DCs.
| The support for Windows Server 2012 and 2012 R2 DCs, including the directory schemas 56 and 67, is experimental. Please report bugs an incompatibilites. For details, see Bug Reporting. |
Warning
| Joining a Windows Server 2012 or 2012 R2 DC to a Samba AD breaks the AD replication! Do not use this documentation until the problem is fixed! For more details, see Bug #13618 and Bug #13619. |
Requirements and Known Limitations
- All Samba DCs must run 4.6 or later. For details about updating Samba, see Updating Samba.
- Windows Server 2012 and 2012 R2 requires the Windows management instrumentation (WMI) protocol during the join, and for the forest and domain preparation. Samba currently does not support this protocol. Therefore you must run a Windows domain controller (DC) with WMI support in your domain. For example, you can a Windows Server 2008 or 2008 R2 DC as replication partner during the join.
- The Windows Server 2008 or 2008 R2 host used for the initial replication must provide a
Sysvolshare. For details, see Enabling the Sysvol Share on a Windows DC.
- If the
Sysvolshare is missing, joining a Windows Server 2012 or 2012 R2 DC fails.
Network Configuration
- Click the
Startbutton, search forView network connections, and open the search entry.
- Right-click to your network adapter and select
Properties.
- Configure the IP settings:
- Assign a static IP address, enter the subnet mask, and default gateway.
- Enter the IP of a DNS server that is able to resolve the Active Directory (AD) DNS zone.
- Click
OKto save the settings.
Date and Time Settings
Active Directory uses Kerberos for authentication. Kerberos requires that the domain member and the domain controllers (DC) are having a synchronous time. If the difference exceeds 5 minutes (default), the client is not able to access domain resources for security reasons.
Before you join the domain, check the time configuration:
- Open the
Control Panel.
- Navigate to
Clock, Language and Region.
- Click
Date and Time.
- Verify the date, time, and time zone settings. Adjust the settings, if necessary.
- Click
OKto save the changes.
FSMO Roles
When you join the first Windows Server 2012 or 2012 R2 host as a domain controller (DC) to an Active Directory (AD), the directory schema of the forest and domain is updated. You must run this process on an existing Windows 2008 or 2008 R2 domain controller (DC) that owns the following flexible single master operation (FSMO) roles:
- Schema Master
- Infrastructure Master
- PDC Emulator
For details about transfering FSMO roles, see Transferring and Seizing FSMO Roles.
After the forest and domain schema was updated, you can optionally transfer the FSMO roles back to a Samba DC.
| Forest and domain preparation fails if a Samba DC holds one to three of the previous mentioned roles when you join the first Windows Server 2012 or 2012 R2 DC. |
Installing the Active Directory Domain Services
- Start the
Server Manager.
- Click
Add roles and features.
- Select
Role-based or feature-based installationand clickNext.
- Click
Select a server from the server pooland select the local Windows Server from the list. ClickNext.
- Select
Active Directory Domain Services, including all dependencies. ClickNext.
- You do not need to select any additional features. Click
Next.
- Start the installation.
- Click
Close.
Joining the Windows Server to the Domain
- Log in to your Windows Server 2012 or 2012 installation using the local administrator account.
- Start the
Server Manager.
- Click the notifier icon on the top navigation bar and click
Promote this server to a domain controller.
- Select
Add a domain controller to an existing domain, enter the Samba Active Directory (AD) domain name and credentials that are enabled to join a domain controller (DC) to the domain, like the domain administrator account. ClickNext.
- Select the options to enable on the new DC and enter the directory services restore mode (DSRM) password. It is required to boot the Windows DC in safe-mode to restore or repair the AD in case of problems. Click
Next.
- If you enabled the
DNS serveroption in the previous step, you may see a note, that a delegation for this DNS server cannot be created. ClickNext.
- Samba currently does not support schema replication using the Windows management instrumentation (WMI) protocol. For this reason, select an existing Windows Domain Controller in the domain as replication source and click
Next.
- Set the folders for the AD database, log files and the Sysvol folder. Click
Next.
- Click
Nextto confirm the operations, Windows is going to perform.
- Verify your settings and click
Nextto start the prerequisite check.
- Windows runs some prerequisites checks. If errors are displayed, fix them before you continue. Click
Install.
- Windows promotes the server to a DC. If it is the first Windows Server 2012 or 2012 R2 DC, the forest and domain schema is automatically updated.

This step breaks the AD directory replication! For details, see Warning.
- If the wizard completes successfully, the Windows server is restarted automatically.
- Verify that all DC related DNS records have been created during the promotion. See Verifying and Creating a DC DNS Record.

Do not continue without checking the DNS records. They must exist for a working directory replication!
Verifying Directory Replication
See Displaying the Replication Statuses on a Windows DC.
| To optimize replication latency and cost, the knowledge consistency checker (KCC) on Windows DCs do not create a fully-meshed replication topology between all DCs. For further details, see The Samba KCC. |
If you used a Samba domain controller (DC) as replication partner, the Sysvol share is not enabled. For details how to verify and enable the share, see Enabling the Sysvol Share on a Windows DC.
Sysvol Replication
Samba currently does not support the DFS-R protocol required for Sysvol replication. Please manually synchronise the content between domain controllers (DC) or use a workaround such as Robocopy-based Sysvol Replication.
Troubleshooting
Error: This operation is only allowed for the Primary Domain Controller of the domain
Windows displays this error if it fails to access the Sysvol on the Windows Server 2008 or 2008 R2 replication partner. For details, see Enabling the Sysvol Share on a Windows DC.