Joining a Windows Server 2008 / 2008 R2 DC to a Samba AD: Difference between revisions
Mmuehlfeld (talk | contribs) m (Fix link) |
|||
| Line 1: | Line 1: | ||
= Introduction = |
= Introduction = |
||
For various reasons user may find themself in a situation, to add a Windows Server 2008 / 2008 R2 as a <u>Domain Controller</u> to their Samba based Active Directory. This process differs from simply joining a Windows Server as a [[ |
For various reasons user may find themself in a situation, to add a Windows Server 2008 / 2008 R2 as a <u>Domain Controller</u> to their Samba based Active Directory. This process differs from simply joining a Windows Server as a [[Joining_a_Windows_client_to_a_domain|Member Server]]. |
||
This documentation is valid only for Microsoft Windows Server 2008 and 2008 R2! |
This documentation is valid only for Microsoft Windows Server 2008 and 2008 R2! |
||
Revision as of 20:59, 24 August 2015
Introduction
For various reasons user may find themself in a situation, to add a Windows Server 2008 / 2008 R2 as a Domain Controller to their Samba based Active Directory. This process differs from simply joining a Windows Server as a Member Server.
This documentation is valid only for Microsoft Windows Server 2008 and 2008 R2!
Server information
This documentation uses the following configurations/settings:
Existing Samba DCs in the domain: Domain Controllers: DC1 (10.99.0.1), DC2 (10.99.0.2) DCs act also as a DNS server: yes Domain information: DNS Domain Name: samdom.example.com NT4 Domain Name (NETBIOS): SAMDOM DNS Servers: 10.99.0.1, 10.99.0.2 Domain Administrator: Administrator Domain Administrator Password: passw0rd Windows DC additionally joined to the domain: Hostname: DC3 IP Address: 10.99.0.3 Operating System: Microsoft Windows Server 2008 R2
Installation / Preparation
General
- Install Windows Server 2008 R2
Configure network
- Search the Control Panel for „Network and Sharing Center“
- Click „Change adapter settings“
- Right-click to your network connection and choose „properties“
- Configure the IP properties. Make sure, that you use a DNS server, that is authoritative for your AD DNS domain!
Date and time settings
Active Directory uses Kerberos for authentication, which relies on a fairly consistent time across the network. This makes it necessary, that, before you can join the server to the Domain, the time does not differ more than 5 minutes (default setting in an AD) to your other Domain Controllers:
- Search the Control Panel for „Date and Time“
- Check your date, time and time zone settings.
Joining the Domain
- Click „Start“ / „Run“, enter „dcpromo.exe“ and click „OK“.
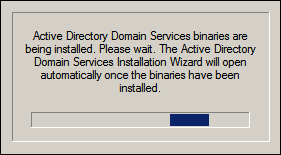
- Windows Server checks if the necessary features are already installed. If not, they will.
- Check the option „Use advanced mode installation“. This mode displays some additional options, that may be useful, like specifying an initial DC to replicate from. To continue click „Next“.
- Read the „Operating System Compatibility“ information and click „Next“.
- Choose „Existing forest“ / „Add a domain controller to an existing domain“ and click „Next“.
- Enter the domain name and credentials of an account that is allowed to join a Domain Controller to the Domain (e. g. Domain Administrator). Afterwards click „Next“.
- If your forest contains multiple domains, the „Select a Domain“ window will list all domains and you have to choose the one, you want to join and then click „Next“.
- Select the AD Site for the new Domain Controller. If you haven't configured AD Sites, choose the default („Default-First-Site-Name“) and click „Next“.
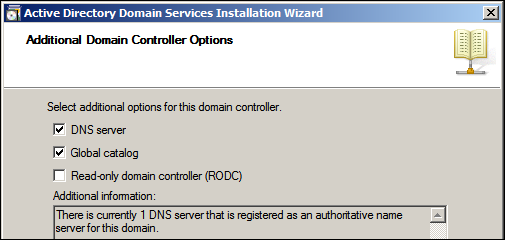
- Decite the options of the new Domain Controller and click „Next“. If you install the DNS server option, make sure, that there is at least one DNS server in your network configuration, that is authoritative for the DNS zone of this domain. An appropriate message is shown in the information box. We assume here, to install the new DC with „DNS server“ and „Global catalog“.
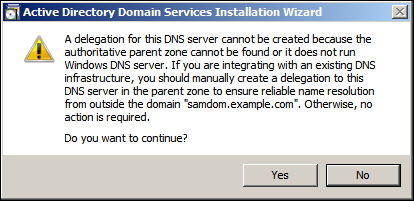
- If you receive a message, that a delegation for this DNS server cannot be created, continue by clicking „Yes“.
- In the „Install from Media“ window, choose to „replicate the data over the network from an existing Domain Controller“ and click „Next“.
- Choose one of the existing DCs to replicate from or let the wizzard do. Then click „Next“.
- Define the folders for the AD database, logs and SysVol and click „Next“
- Set a Directory Service Restore Mode Administrator Passwort. The DSRM passwort is used to boot the Windows DC in a safe-mode, to restore or repair the AD. To continue click „Next“.
- A summery is displayed. Verify your settings and click „Next“ to start the Domain Controller promotion process.
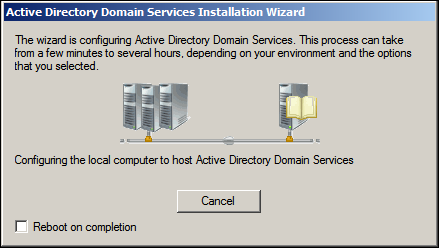
- The wizzard begins to install options, replicate the directory, etc. Depending on the size of your directory and your bandwitdh, this may take some time.
- Check if all important DNS records exists. If not, add them manually. It's an important step for a healthy and working replication!
- After the wizzard has completed, click „Finish“ and restart the new Domain Controller.
- The Windows Server is now joined as a Domain Controller.
Directory replication
A few minutes after startup, connections with other DCs will be established automatically and replication begins. On a Samba DC, this can be verified by
# samba-tool drs showrepl
Default-First-Site-Name\DC1
DSA Options: 0x00000001
DSA object GUID: 4a6bd92a-6612-4b15-aa8c-9ec371e8994f
DSA invocationId: 96bc0d6f-9cea-4011-b9a1-0e9971009b20
==== INBOUND NEIGHBORS ====
DC=DomainDnsZones,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC2 via RPC
DSA object GUID: c14a774f-9732-4ec2-b9fa-2156c95c4e48
Last attempt @ Sat Dec 20 10:35:19 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:35:19 2014 CET
DC=DomainDnsZones,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC3 via RPC
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9
Last attempt @ NTTIME(0) was successful
0 consecutive failure(s).
Last success @ NTTIME(0)
DC=ForestDnsZones,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC2 via RPC
DSA object GUID: c14a774f-9732-4ec2-b9fa-2156c95c4e48
Last attempt @ Sat Dec 20 10:35:19 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:35:19 2014 CET
DC=ForestDnsZones,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC3 via RPC
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9
Last attempt @ NTTIME(0) was successful
0 consecutive failure(s).
Last success @ NTTIME(0)
DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC2 via RPC
DSA object GUID: c14a774f-9732-4ec2-b9fa-2156c95c4e48
Last attempt @ Sat Dec 20 10:35:20 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:35:20 2014 CET
DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC3 via RPC
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9
Last attempt @ Sat Dec 20 10:35:09 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:35:09 2014 CET
CN=Schema,CN=Configuration,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC2 via RPC
DSA object GUID: c14a774f-9732-4ec2-b9fa-2156c95c4e48
Last attempt @ Sat Dec 20 10:35:16 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:35:16 2014 CET
CN=Schema,CN=Configuration,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC3 via RPC
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9
Last attempt @ Sat Dec 20 10:35:10 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:35:10 2014 CET
CN=Configuration,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC2 via RPC
DSA object GUID: c14a774f-9732-4ec2-b9fa-2156c95c4e48
Last attempt @ Sat Dec 20 10:35:17 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:35:17 2014 CET
CN=Configuration,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC3 via RPC
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9
Last attempt @ Sat Dec 20 10:35:11 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:35:11 2014 CET
==== OUTBOUND NEIGHBORS ====
DC=DomainDnsZones,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC3 via RPC
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9
Last attempt @ Sat Dec 20 10:35:17 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:35:17 2014 CET
DC=DomainDnsZones,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC2 via RPC
DSA object GUID: c14a774f-9732-4ec2-b9fa-2156c95c4e48
Last attempt @ NTTIME(0) was successful
0 consecutive failure(s).
Last success @ NTTIME(0)
DC=ForestDnsZones,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC3 via RPC
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9
Last attempt @ Sat Dec 20 10:35:17 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:35:17 2014 CET
DC=ForestDnsZones,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC2 via RPC
DSA object GUID: c14a774f-9732-4ec2-b9fa-2156c95c4e48
Last attempt @ NTTIME(0) was successful
0 consecutive failure(s).
Last success @ NTTIME(0)
DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC3 via RPC
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9
Last attempt @ Sat Dec 20 10:34:26 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:34:26 2014 CET
DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC2 via RPC
DSA object GUID: c14a774f-9732-4ec2-b9fa-2156c95c4e48
Last attempt @ NTTIME(0) was successful
0 consecutive failure(s).
Last success @ NTTIME(0)
CN=Schema,CN=Configuration,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC3 via RPC
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9
Last attempt @ Sat Dec 20 10:34:26 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:34:26 2014 CET
CN=Schema,CN=Configuration,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC2 via RPC
DSA object GUID: c14a774f-9732-4ec2-b9fa-2156c95c4e48
Last attempt @ NTTIME(0) was successful
0 consecutive failure(s).
Last success @ NTTIME(0)
CN=Configuration,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC3 via RPC
DSA object GUID: dfaec3fb-7546-4153-ba01-605e5efa27f9
Last attempt @ Sat Dec 20 10:34:21 2014 CET was successful
0 consecutive failure(s).
Last success @ Sat Dec 20 10:34:21 2014 CET
CN=Configuration,DC=samdom,DC=example,DC=com
Default-First-Site-Name\DC2 via RPC
DSA object GUID: c14a774f-9732-4ec2-b9fa-2156c95c4e48
Last attempt @ NTTIME(0) was successful
0 consecutive failure(s).
Last success @ NTTIME(0)
==== KCC CONNECTION OBJECTS ====
Connection --
Connection name: 04baf417-eb41-4f31-a5f1-c739f0e92b1b
Enabled : TRUE
Server DNS name : DC2.samdom.example.com
Server DN name : CN=NTDS Settings,CN=DC2,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com
TransportType: RPC
options: 0x00000001
Warning: No NC replicated for Connection!
Connection --
Connection name: f55bce90-d458-400a-a4ca-801c3e64bef3
Enabled : TRUE
Server DNS name : DC3.samdom.example.com
Server DN name : CN=NTDS Settings,CN=DC3,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com
TransportType: RPC
options: 0x00000001
Warning: No NC replicated for Connection!
Depending on your replication settings - if defined - it may take a few minutes until all connections are established. So please be patient! On the long shot that the outbound connections aren't established automatically - even not after several minutes - you can force the replication (generally not necessary!). See samba-tool drs replicate.
Note about the„Warning: No NC replicated for Connection!“ line: It can be safely ignored. See FAQ: Message: Warning: No NC replicated for Connection!
During the join, Windows tries to retrieve the SysVol content from an other Domain Controller. But Samba currently doesn't support SysVol replication (DFS-R) yet. This causes, that the new Windows DC, doesn't share the SysVol folder.
The folder isn't shared like other folders in Windows. If there is no „SysVol“ share, when you enter \\Hostname („\\DC3“ in this example), change the registry value of „SysvolReady“ in HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Netlogon\Parameters\ to „1“. The share will be visible after the next refresh ([F5]).
SysVol replication
Currently replication of the SysVol share via DFS-R isn't implemented in Samba. If you make changes on that share, you have to keep them in sync on all your Domain Controllers, including ACLs! An example, how to achieve this, is provided in the SysVol replication between Samba and Windows documentation.
Testing directory replication
To check that replication is working correctly between your domain controllers, try adding/modifying e. g. a user on one DC using either the Samba command line tools or the Windows GUI admin tools. Then check that the changes shows up within a few seconds on the new Domain Controller.