Demoting a Samba AD DC: Difference between revisions
Mmuehlfeld (talk | contribs) m (Typo) |
Bishopolis (talk | contribs) m (some English translation) |
||
| Line 11: | Line 11: | ||
= Demote a working Domain Controller = |
= Demote a working Domain Controller = |
||
Follow this section |
Follow this section if your DC is accessible and working. |
||
* Log into the DC you want to demote. |
* Log into the DC you want to demote. |
||
| Line 17: | Line 17: | ||
* Verify that the DC is not the last one remaining in the domain! |
* Verify that the DC is not the last one remaining in the domain! |
||
* Make sure |
* Make sure this DC does not contain any [[Flexible_Single-Master_Operations_(FSMO)_roles|FSMO role]]: |
||
# samba-tool fsmo show |
# samba-tool fsmo show |
||
| Line 31: | Line 31: | ||
ForestDnsZonesMasterRole owner: CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com |
ForestDnsZonesMasterRole owner: CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com |
||
Irrespective of version, there are 7 FSMO roles |
Irrespective of version, there are 7 FSMO roles. See [[Transfering_/_seizing_FSMO_roles#Show_current_FSMO_role_owners|show fsmo roles]] for how to display all 7 roles on earlier versions. |
||
: If it still contains one or more [[Flexible_Single-Master_Operations_(FSMO)_roles#Transfering_a_FSMO_role|FSMO roles, transfer]] them to a different DC. |
: If it still contains one or more [[Flexible_Single-Master_Operations_(FSMO)_roles#Transfering_a_FSMO_role|FSMO roles, transfer]] them to a different DC. |
||
Revision as of 05:07, 28 March 2016
Introduction
Whenever a Domain Controller needs to be removed from your domain, for what ever reason, you will have to demote it. This documentation describes different scenarios to demote a Domain Controller.
See the server information used in documentation page for paths used, hostnames, etc.
Demote a working Domain Controller
Follow this section if your DC is accessible and working.
- Log into the DC you want to demote.
- Verify that the DC is not the last one remaining in the domain!
- Make sure this DC does not contain any FSMO role:
# samba-tool fsmo show InfrastructureMasterRole owner: CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com RidAllocationMasterRole owner: CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com PdcEmulationMasterRole owner: CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com DomainNamingMasterRole owner: CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com SchemaMasterRole owner: CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com
- If you are using Samba 4.3.0 and up, the samba tool command will show an extra two FSMO roles:
DomainDnsZonesMasterRole owner: CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com ForestDnsZonesMasterRole owner: CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com
Irrespective of version, there are 7 FSMO roles. See show fsmo roles for how to display all 7 roles on earlier versions.
- If it still contains one or more FSMO roles, transfer them to a different DC.
- Demote the DC:
# samba-tool domain demote -Uadministrator Using DC1.samdom.example.com as partner server for the demotion Password for [SAMDOM\administrator]: Desactivating inbound replication Asking partner server DC1.samdom.example.com to synchronize from us Changing userControl and container Demote successfull
- Shutdown Samba
Demote a DC that isn't accessable any more
Note: Samba versions prior 4.4 don't support demoting a foreign DC, that is offline. Upgrade your existing DCs to 4.4 or later, in that case.
Follow this section, if your DC is not accessable any more, e. g. by hardware failure and it surely will never come back into the network.
Run the following command on one of the remaining, working Domain Controller:
# samba-tool domain demote --remove-other-dead-server=DC2 Removing nTDSConnection: CN=04baf417-eb41-4f31-a5f1-c739f0e92b1b,CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com Removing nTDSDSA: CN=NTDS Settings,CN=DC2,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=samdom,DC=example,DC=com (and any children) Removing RID Set: CN=RID Set,CN=DC2,OU=Domain Controllers,DC=samdom,DC=example,DC=com Removing computer account: CN=DC2,OU=Domain Controllers,DC=samdom,DC=example,DC=com (and any child objects) Removing Samba-specific DNS service account: CN=dns-DC2,CN=Users,DC=samdom,DC=example,DC=com updating samdom.example.com keeping 3 values, removing 1 values updating DC=_kerberos._tcp.Default-First-Site-Name._sites,DC=samdom.example.com,CN=MicrosoftDNS,DC=DomainDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_ldap._tcp.Default-First-Site-Name._sites,DC=samdom.example.com,CN=MicrosoftDNS,DC=DomainDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_gc._tcp.Default-First-Site-Name._sites,DC=samdom.example.com,CN=MicrosoftDNS,DC=DomainDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_kerberos._tcp,DC=samdom.example.com,CN=MicrosoftDNS,DC=DomainDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_kerberos._udp,DC=samdom.example.com,CN=MicrosoftDNS,DC=DomainDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_kpasswd._tcp,DC=samdom.example.com,CN=MicrosoftDNS,DC=DomainDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_kpasswd._udp,DC=samdom.example.com,CN=MicrosoftDNS,DC=DomainDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_ldap._tcp,DC=samdom.example.com,CN=MicrosoftDNS,DC=DomainDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_gc._tcp,DC=samdom.example.com,CN=MicrosoftDNS,DC=DomainDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_ldap._tcp.4d5258b9-0cd7-4d78-bdd7-99ebe6b19751.domains,DC=_msdcs.samdom.example.com,CN=MicrosoftDNS,DC=ForestDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_kerberos._tcp.Default-First-Site-Name._sites.dc,DC=_msdcs.samdom.example.com,CN=MicrosoftDNS,DC=ForestDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_ldap._tcp.Default-First-Site-Name._sites.dc,DC=_msdcs.samdom.example.com,CN=MicrosoftDNS,DC=ForestDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_ldap._tcp.Default-First-Site-Name._sites.gc,DC=_msdcs.samdom.example.com,CN=MicrosoftDNS,DC=ForestDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=c14a774f-9732-4ec2-b9fa-2156c95c4e48,DC=_msdcs.samdom.example.com,CN=MicrosoftDNS,DC=ForestDnsZones,DC=samdom,DC=example,DC=com keeping 0 values, removing 1 values updating DC=_kerberos._tcp.dc,DC=_msdcs.samdom.example.com,CN=MicrosoftDNS,DC=ForestDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_ldap._tcp.dc,DC=_msdcs.samdom.example.com,CN=MicrosoftDNS,DC=ForestDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values updating DC=_ldap._tcp.gc,DC=_msdcs.samdom.example.com,CN=MicrosoftDNS,DC=ForestDnsZones,DC=samdom,DC=example,DC=com keeping 1 values, removing 1 values Removing Sysvol reference: CN=DC2,CN=Enterprise,CN=Microsoft System Volumes,CN=System,CN=Configuration,DC=samdom,DC=example,DC=com Removing Sysvol reference: CN=DC2,CN=samdom.example.com,CN=Microsoft System Volumes,CN=System,CN=Configuration,DC=samdom,DC=example,DC=com Removing Sysvol reference: CN=DC2,CN=Domain System Volumes (SYSVOL share),CN=File Replication Service,CN=System,DC=samdom,DC=example,DC=com Removing Sysvol reference: CN=DC2,CN=Topology,CN=Domain System Volume,CN=DFSR-GlobalSettings,CN=System,DC=samdom,DC=example,DC=com
Verifying that nothing was left
The following steps are done on a Windows computer having RSAT installed.
Warning: The following are just cleanup steps, if something was left after a demote! It's not a replacement for the demote process itself!
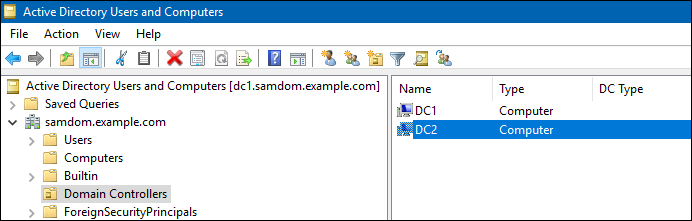
- Open „Active Directory Users and Computers“
- Go to the container „Domain Controllers“ and verify that the demoted DC was removed. If not, remove the account manually. This would also cleanup metadata. DC removal via ADUC is currently broken. See Bug report #10595.
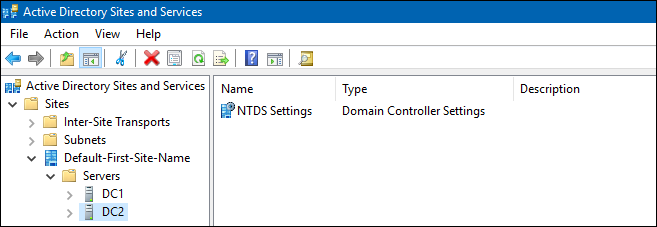
- Open „Active Directory Sites and Services“
- Check that the demoted DC doesn't exist any more in any site. If an entry is still there, remove it manually.
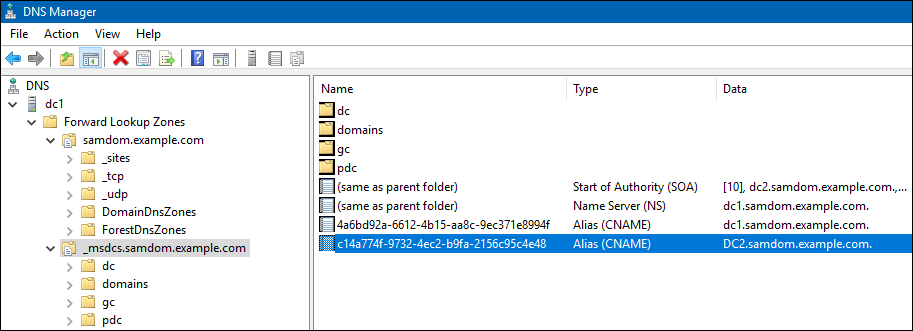
- Open the „DNS“ console
- Check in all zones, that no entry about the demoted DC is still existing.