DNS Administration: Difference between revisions
Mmuehlfeld (talk | contribs) (Fix information, that new zones are directly live. Internal DNS requires a restart of Samba for that currently (Bug)) |
m (/* removed note about fixed bug) |
||
| (35 intermediate revisions by 5 users not shown) | |||
| Line 3: | Line 3: | ||
If you're running Samba as Active Directory Domain Controller, you also have to administer a DNS server. |
If you're running Samba as Active Directory Domain Controller, you also have to administer a DNS server. |
||
You will already find general [[ |
You will already find general [[The_Samba_AD_DNS_Back_Ends|information on the internal DNS and the BIND DLZ module]] and documentation about [[BIND9_DLZ_DNS_Back_End|Bind as DNS Backend]] in the Wiki. |
||
= General = |
= General = |
||
By default, Samba creates the following two forward zones during provisioning/upgrading (of course with your own domain name): |
|||
* '''samdom.example.com''': Zone for your domain. |
* '''samdom.example.com''': Zone for your domain. |
||
| Line 18: | Line 22: | ||
= Features = |
= Features = |
||
The Samba internal DNS is a new implementation. Although BIND is a grown up DNS and long in production on millions of servers, the Samba BIND DLZ module is still new. That's why both backends don't cover all features |
The Samba internal DNS is a new implementation. Although BIND is a grown up DNS and long in production on millions of servers, the Samba BIND DLZ module is still new. That's why both backends don't yet cover all the features that you can setup with the Microsoft DNS tools. If you discover problems or missing features, please open a bug report/feature request at [https://bugzilla.samba.org/ https://bugzilla.samba.org/]. |
||
Even though the internal DNS and the BIND DLZ modules are new, they both support all basic requirements for Active Directory and more. |
|||
| Line 29: | Line 33: | ||
* Different zone transfer settings on internal DNS (denied) and BIND DLZ (allowed). [https://bugzilla.samba.org/show_bug.cgi?id=9634 Bug report #9634: Samba Bind DLZ module allows zone transfers for everyone] |
* Different zone transfer settings on internal DNS (denied) and BIND DLZ (allowed). [https://bugzilla.samba.org/show_bug.cgi?id=9634 Bug report #9634: Samba Bind DLZ module allows zone transfers for everyone] |
||
= Importance of DNS for Active Directory = |
= Importance of DNS for Active Directory = |
||
A working Active Directory is heavily based on a working DNS. It's not just for resolving IP addresses into names and vice versa. Clients find their Domain Controller/s and other important AD services by DNS queries. |
A working Active Directory is heavily based on a working DNS. It's not just for resolving IP addresses into names and vice versa. Clients find their Domain Controller/s and other important AD services by DNS queries, this means that your clients must use your Domain Controller/s as their nameservers. Do not use anything else between your clients and Domain Controller/s. |
||
| Line 39: | Line 48: | ||
= Administering DNS on Windows = |
= Administering DNS on Windows = |
||
To administer DNS from a Windows client, you have to install the DNS MMC Snap-In. See [[ |
To administer DNS from a Windows client, you have to install the DNS MMC Snap-In. See [[Installing RSAT|Installing RSAT on Windows for AD Management]] for more details. |
||
If you use the internal DNS server, there are the following known problems: |
|||
* Scavenging is not implemented yet. The error message "This function is not supported on this system" is returned. |
|||
* Conditional forwarders are not implemented yet. The same error message as above is returned. |
|||
* The DNS forwarder can only be changed in the smb.conf, not via the MMC Snap-In. |
|||
* Creating static records. When a static record is created it has a timestamp and the option "Delete this record when it becomes stale". In Windows Active Directory, static records have a "static" timestamp and cannot be accidently deleted. |
|||
| Line 81: | Line 98: | ||
* Choose „Properties“. |
* Choose „Properties“. |
||
'''Note''': Currently both DNS backends |
'''Note''': Currently both DNS backends don't support all features that can be setup in the dialogues. If you discover problems or missing features, please open a bug report/feature request at [https://bugzilla.samba.org/ https://bugzilla.samba.org/]. |
||
| Line 97: | Line 114: | ||
: [[Image:DNS_Add_Zone_Wizzard_1.png]] |
: [[Image:DNS_Add_Zone_Wizzard_1.png]] |
||
* Zone Replication Scope: |
* Zone Replication Scope: Depends on your needs. |
||
: [[Image:DNS_Add_Zone_Wizzard_2.png]] |
: [[Image:DNS_Add_Zone_Wizzard_2.png]] |
||
* Reverse Lookup Zone Name: |
* Reverse Lookup Zone Name: Depends on your needs. |
||
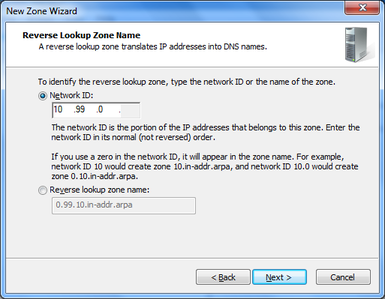
: [[Image:DNS_Add_Zone_Wizzard_3.png]] |
: [[Image:DNS_Add_Zone_Wizzard_3.png]] |
||
: Dynamic Update: |
: Dynamic Update: Depends on your needs. |
||
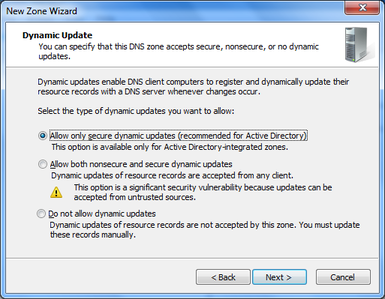
: [[Image:DNS_Add_Zone_Wizzard_4.png]] |
: [[Image:DNS_Add_Zone_Wizzard_4.png]] |
||
| Line 111: | Line 128: | ||
* Finish the wizard. |
* Finish the wizard. |
||
Your new zone is directly live without restarting Samba or BIND. |
|||
The internal DNS as backend currently needs a restart of Samba to take effect. See [https://bugzilla.samba.org/show_bug.cgi?id=9404 bug report #9404]. |
|||
| Line 129: | Line 145: | ||
* Example: Adding an A record |
* Example: Adding an A record |
||
# samba-tool dns add <Your-Server> samdom.example.com demo A 10.99.0.55 |
# samba-tool dns add <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com demo A 10.99.0.55 |
||
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
||
Record added successfully |
Record added successfully |
||
| Line 135: | Line 151: | ||
* Example: Adding a PTR record to a reverse zone |
* Example: Adding a PTR record to a reverse zone |
||
# samba-tool dns add <Your-Server> 0.99.10.in-addr.arpa 55 PTR demo.samdom.example.com |
# samba-tool dns add <Your-AD-DNS-Server-IP-or-hostname> 0.99.10.in-addr.arpa 55 PTR demo.samdom.example.com |
||
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
||
Record added successfully |
Record added successfully |
||
| Line 141: | Line 157: | ||
* Example: Adding a SRV record to _tcp.samdom.example.com |
* Example: Adding a SRV record to _tcp.samdom.example.com |
||
# samba-tool dns add <Your-Server> samdom.example.com _demo._tcp SRV 'demo.samdom.example.com 8080 0 100' |
# samba-tool dns add <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com _demo._tcp SRV 'demo.samdom.example.com 8080 0 100' |
||
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
||
Record added successfully |
Record added successfully |
||
| Line 153: | Line 169: | ||
* Example: Changing an A record |
* Example: Changing an A record |
||
# samba-tool dns update <Your-Server> samdom.example.com demo A 10.99.0.55 10.99.0.66 |
# samba-tool dns update <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com demo A 10.99.0.55 10.99.0.66 |
||
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
||
Record updated succefully |
Record updated succefully |
||
| Line 162: | Line 178: | ||
* Example: Deleting an A record |
* Example: Deleting an A record |
||
# samba-tool dns delete <Your-Server> samdom.example.com demo A 10.99.0.55 |
# samba-tool dns delete <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com demo A 10.99.0.55 |
||
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
||
Record deleted succefully |
Record deleted succefully |
||
| Line 172: | Line 188: | ||
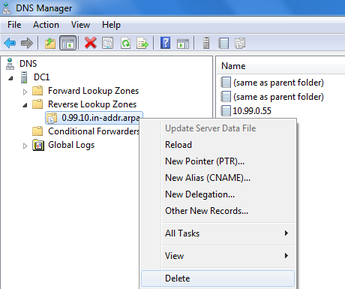
As example we'll add a reverse lookup zone. |
As example we'll add a reverse lookup zone. |
||
# samba-tool dns zonecreate <Your-Server> 0.99.10.in-addr.arpa |
# samba-tool dns zonecreate <Your-AD-DNS-Server-IP-or-hostname> 0.99.10.in-addr.arpa |
||
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
||
Zone 0.99.10.in-addr.arpa created successfully |
Zone 0.99.10.in-addr.arpa created successfully |
||
Your new zone is directly live without restarting Samba or BIND. |
|||
The internal DNS as backend currently needs a restart of Samba to take effect. See [https://bugzilla.samba.org/show_bug.cgi?id=9404 bug report #9404]. |
|||
| Line 186: | Line 201: | ||
* Example: Deleting a reverse zone: |
* Example: Deleting a reverse zone: |
||
# samba-tool dns zonedelete <Your-Server> 0.99.10.in-addr.arpa |
# samba-tool dns zonedelete <Your-AD-DNS-Server-IP-or-hostname> 0.99.10.in-addr.arpa |
||
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
Password for [administrator@SAMDOM.EXAMPLE.COM]: |
||
Zone 0.99.10.in-addr.arpa delete successfully |
Zone 0.99.10.in-addr.arpa delete successfully |
||
= Configuring clients to use your AD DNS server = |
|||
If you provide DNS server addresses via DHCP to your clients, configure your DHCP server to ship the adress/es of your DNS server/s. |
|||
== Listing existing zones == |
|||
For static configuration on the different Windows versions, continue reading. |
|||
* Example: listing secondary zones |
|||
# samba-tool dns zonelist <Your-AD-DNS-Server-IP-or-hostname> --secondary -U administrator |
|||
== Windows 8 == |
|||
== Listing zone information == |
|||
* Press [Win]+[W] and search for „Network and Sharing Center“ in Settings and open the app. |
|||
* Example: showing information about a zone |
|||
: [[Image:Win8_Network_App.png]] |
|||
# samba-tool dns zoneinfo <Your-AD-DNS-Server-IP-or-hostname> <zone-name> -U administrator |
|||
* Click „Change adapter settings“. |
|||
* Right-click to your network adapter and choose „Properties“. |
|||
== Listing zone records == |
|||
: [[Image:Win8_Network_and_Sharing_Center.png]] |
|||
* Example: listing records from a zone |
|||
* Click to your Internet Protocol (IPv4/IPv6) and click the „Properties“ button. |
|||
# samba-tool dns query <Your-AD-DNS-Server-IP-or-hostname> <zone-name> @ ALL -U administrator |
|||
= Configuring clients to use your AD DNS server = |
|||
* [[Windows_DNS_Configuration|Windows]] |
|||
: [[Image:Win8_DNS_Server_Addresses.png]] |
|||
* [[Linux_and_Unix_DNS_Configuration|Linux/Unix]] |
|||
* [[MacOSX_DNS_Configuration|MacOSX]] |
|||
* Save the settings by clicking „OK“. |
|||
== Windows 7 == |
|||
* Click to „Start“ and search for „Network and Sharing Center“. |
|||
* Click „Change adapter settings“. |
|||
* Right-click to your network adapter and choose „Properties“. |
|||
: [[Image:Win7_Network_and_Sharing_Center.png]] |
|||
* Click to your Internet Protocol (IPv4/IPv6) and click the „Properties“ button. |
|||
* Enter the IP address/es of your DNS server/s. |
|||
: [[Image:Win7_DNS_Server_Addresses.png]] |
|||
* Save the settings by clicking „OK“. |
|||
== Windows XP == |
|||
* Right-click to „My Network Places“ and choose „Properties“. |
|||
* Right-click to your network connection and choose „Properties“. |
|||
: [[Image:WinXP_My_Network_Places.png]] |
|||
* Click to your Internet Protocol and click the „Properties“ button. |
|||
* Enter the IP address/es of your DNS server/s. |
|||
: [[Image:WinXP_DNS_Server_Addresses.png]] |
|||
* Save the settings by clicking „OK“. |
|||
== Linux/Unix == |
|||
Edit your /etc/resolv.conf and add a „nameserver“ entry for each DNS server and your search domain: |
|||
nameserver 10.99.0.1 |
|||
nameserver 10.99.0.2 |
|||
search samdom.example.com |
|||
| Line 271: | Line 238: | ||
= Testing your DNS Server = |
= Testing your DNS Server = |
||
See [[Testing_the_DNS_Name_Resolution|Testing the DNS Name Resolution]]. |
|||
On Windows and *nix, you can use „nslookup“ to test if your computer can resolve records by using your DNS. Try resolving the name of your Domain Controller into its IP: |
|||
# nslookup DC1.samdom.example.com |
|||
Server: 10.99.0.1 |
|||
Address: 10.99.0.1#53 |
|||
Name: DC1.samdom.example.com |
|||
Address: 10.99.0.1 |
|||
Nslookup will show you, which server was asked (10.99.0.1) and the result of your query (DC1.samdom.example.com has IP 10.99.0.1) |
|||
To query a SVR record, you have to start nslookup and set the type to „SRV“, to retrieve the values (works on Windows and *nix): |
|||
# nslookup |
|||
Default Server: UnKnown |
|||
Address: 10.99.0.1 |
|||
> set type=SRV |
|||
> _ldap._tcp.samdom.example.com. |
|||
Server: UnKnown |
|||
Address: 10.99.0.1 |
|||
_ldap._tcp.samdom.example.com SRV service location: |
|||
priority = 0 |
|||
weight = 100 |
|||
port = 389 |
|||
svr hostname = dc1.samdom.example.com |
|||
samdom.example.com nameserver = dc1.samdom.example.com |
|||
dc1.samdom.example.com internet address = 10.99.0.1 |
|||
If your query can't be answered, because it doesn't exist, you'll receive |
|||
** server can't find DC9.samdom.example.com: NXDOMAIN |
|||
If you query a none existing DNS server, it would result in |
|||
---- |
|||
;; connection timed out; no servers could be reached |
|||
[[Category:Active Directory]] |
|||
[[Category:DNS]] |
|||
Revision as of 15:42, 17 August 2018
Introduction
If you're running Samba as Active Directory Domain Controller, you also have to administer a DNS server.
You will already find general information on the internal DNS and the BIND DLZ module and documentation about Bind as DNS Backend in the Wiki.
General
By default, Samba creates the following two forward zones during provisioning/upgrading (of course with your own domain name):
- samdom.example.com: Zone for your domain.
- _msdcs.samdom.example.com: This is the ForestDNSZone, that contains several service records for the entire directory.
Features
The Samba internal DNS is a new implementation. Although BIND is a grown up DNS and long in production on millions of servers, the Samba BIND DLZ module is still new. That's why both backends don't yet cover all the features that you can setup with the Microsoft DNS tools. If you discover problems or missing features, please open a bug report/feature request at https://bugzilla.samba.org/.
Even though the internal DNS and the BIND DLZ modules are new, they both support all basic requirements for Active Directory and more.
Known/issues missing features
- Managing zone transfers is not implemented yet. Bug report #9951:DNS MMC: Enabling DNS zone transfers in MMC fails
- Different zone transfer settings on internal DNS (denied) and BIND DLZ (allowed). Bug report #9634: Samba Bind DLZ module allows zone transfers for everyone
Importance of DNS for Active Directory
A working Active Directory is heavily based on a working DNS. It's not just for resolving IP addresses into names and vice versa. Clients find their Domain Controller/s and other important AD services by DNS queries, this means that your clients must use your Domain Controller/s as their nameservers. Do not use anything else between your clients and Domain Controller/s.
Administering DNS on Windows
To administer DNS from a Windows client, you have to install the DNS MMC Snap-In. See Installing RSAT on Windows for AD Management for more details.
If you use the internal DNS server, there are the following known problems:
- Scavenging is not implemented yet. The error message "This function is not supported on this system" is returned.
- Conditional forwarders are not implemented yet. The same error message as above is returned.
- The DNS forwarder can only be changed in the smb.conf, not via the MMC Snap-In.
- Creating static records. When a static record is created it has a timestamp and the option "Delete this record when it becomes stale". In Windows Active Directory, static records have a "static" timestamp and cannot be accidently deleted.
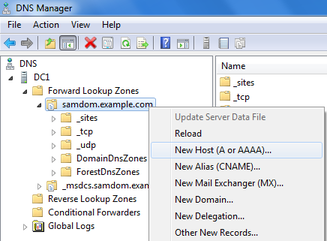
Adding new records
- Navigate to the zone, where you want to to add a new record.
- Right-click to it and choose the kind of record to add.
- Fill the fields and save the new entry.
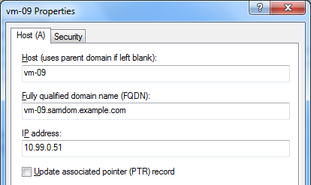
Updating existing records
- Navigate to the zone that contains the record you want to edit.
- Right-click the record and choose „Properties“.
- Edit the entry and save the changes.
Delete a record
- Navigate to the zone that contains the record you want to remove.
- Right-click to the record and choose „Delete“.
Changing zone properties
- Right-click to a zone of which you you want to do changes.
- Choose „Properties“.
Note: Currently both DNS backends don't support all features that can be setup in the dialogues. If you discover problems or missing features, please open a bug report/feature request at https://bugzilla.samba.org/.
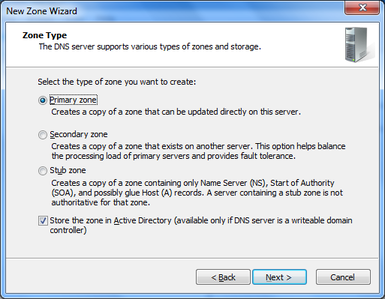
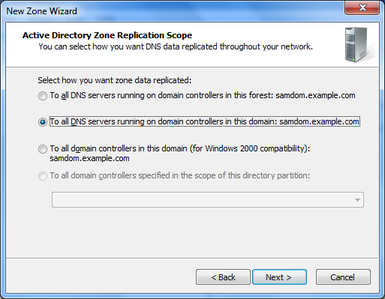
Creating a new zone
As example we'll add a reverse lookup zone.
- Right-click to „Reverse Lookup Zones“ and choose „New Zone“.
- The „New Zone Wizard“ appears.
- Zone Type: Select „Primary zone“ and „Store the zone in Active Directory“.
- Zone Replication Scope: Depends on your needs.
- Reverse Lookup Zone Name: Depends on your needs.
- Dynamic Update: Depends on your needs.
- Finish the wizard.
Your new zone is directly live without restarting Samba or BIND.
Deleting a zone
- Right-click to a zone and choose „Delete“.
Administering DNS on Linux/Unix
Adding new records
- Example: Adding an A record
# samba-tool dns add <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com demo A 10.99.0.55 Password for [administrator@SAMDOM.EXAMPLE.COM]: Record added successfully
- Example: Adding a PTR record to a reverse zone
# samba-tool dns add <Your-AD-DNS-Server-IP-or-hostname> 0.99.10.in-addr.arpa 55 PTR demo.samdom.example.com Password for [administrator@SAMDOM.EXAMPLE.COM]: Record added successfully
- Example: Adding a SRV record to _tcp.samdom.example.com
# samba-tool dns add <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com _demo._tcp SRV 'demo.samdom.example.com 8080 0 100' Password for [administrator@SAMDOM.EXAMPLE.COM]: Record added successfully
- A note on SRV records: The order of the four parameters in the last field („data“) are 'hostname port priority weight' and have to be between ' '.
Updating existing records
- Example: Changing an A record
# samba-tool dns update <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com demo A 10.99.0.55 10.99.0.66 Password for [administrator@SAMDOM.EXAMPLE.COM]: Record updated succefully
Delete a record
- Example: Deleting an A record
# samba-tool dns delete <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com demo A 10.99.0.55 Password for [administrator@SAMDOM.EXAMPLE.COM]: Record deleted succefully
Creating a new zone
As example we'll add a reverse lookup zone.
# samba-tool dns zonecreate <Your-AD-DNS-Server-IP-or-hostname> 0.99.10.in-addr.arpa Password for [administrator@SAMDOM.EXAMPLE.COM]: Zone 0.99.10.in-addr.arpa created successfully
Your new zone is directly live without restarting Samba or BIND.
Deleting a zone
- Example: Deleting a reverse zone:
# samba-tool dns zonedelete <Your-AD-DNS-Server-IP-or-hostname> 0.99.10.in-addr.arpa Password for [administrator@SAMDOM.EXAMPLE.COM]: Zone 0.99.10.in-addr.arpa delete successfully
Listing existing zones
- Example: listing secondary zones
# samba-tool dns zonelist <Your-AD-DNS-Server-IP-or-hostname> --secondary -U administrator
Listing zone information
- Example: showing information about a zone
# samba-tool dns zoneinfo <Your-AD-DNS-Server-IP-or-hostname> <zone-name> -U administrator
Listing zone records
- Example: listing records from a zone
# samba-tool dns query <Your-AD-DNS-Server-IP-or-hostname> <zone-name> @ ALL -U administrator
Configuring clients to use your AD DNS server
Testing your DNS Server
See Testing the DNS Name Resolution.