Wireshark Decryption: Difference between revisions
| Line 13: | Line 13: | ||
==Known limitations== |
==Known limitations== |
||
As of Wireshark 2.6.5 (December 2018): |
As of Wireshark 2.6.5 (December 2018): |
||
* only supports SMB3.0 |
* only supports SMB3.0. Decryption of SMB3.1.1 will be in the next release. |
||
* only supports AES-128-CCM |
* only supports AES-128-CCM |
||
* Due to how the dissector works, the trace requires a Tree Connect packet to be present in the trace being decrypted (done using the right session id). |
* Due to how the dissector works, the trace requires a Tree Connect packet to be present in the trace being decrypted (done using the right session id). |
||
| Line 43: | Line 43: | ||
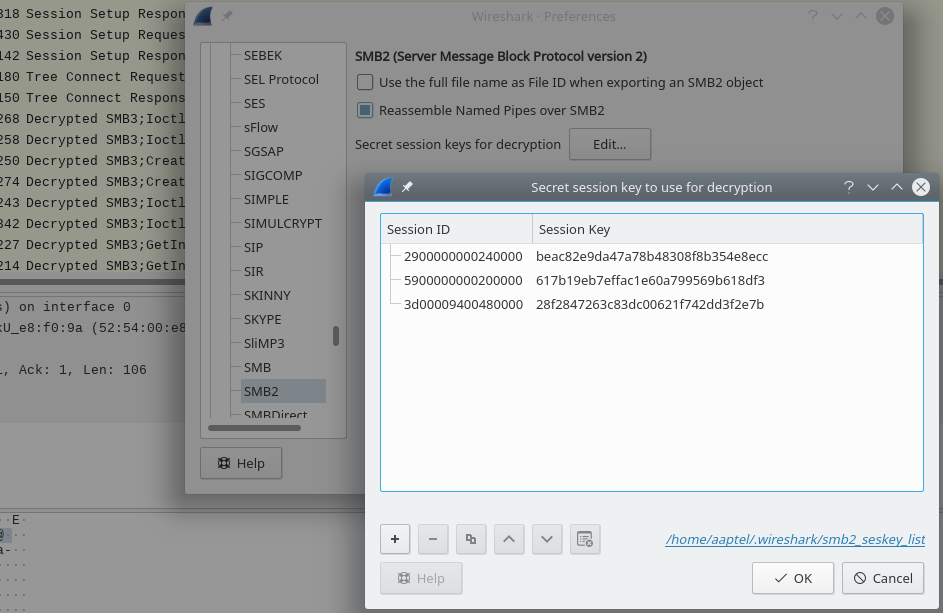
[[File:wireshark-decryption.png|thumb|Setting a key: Edit > Preferences > SMB2, Edit]] |
[[File:wireshark-decryption.png|thumb|Setting a key: Edit > Preferences > SMB2, Edit]] |
||
'''Note''': The kernel prints the Session Id as it is on the wire (little endian). Wireshark decryption expects the Session Id as it is on the wire as well, so you should be able to copy/paste from one to the other (despite showing the Session ID field decoded when dumping packets). |
|||
* Just copy the Session Id and Session Key into wireshark (see screenshot). |
* Just copy the Session Id and Session Key into wireshark (see screenshot). |
||
Revision as of 14:03, 6 February 2019
Using the session key (SMB3)
Starting from Wireshark 2.5.0 (released Feb 2018) you can pass a list of SessionId -> SessionKey mappings via a table in the SMB2 preferences or command-line.
The session key in this context refers to the cryptographic session keys used in authentication and message signing. It is not the same as the CIFS SessionKey.
From MS-SMB2:
Session.SessionKey: The first 16 bytes of the cryptographic key for this authenticated context. If the cryptographic key is less than 16 bytes, it is right-padded with zero bytes.
Known limitations
As of Wireshark 2.6.5 (December 2018):
- only supports SMB3.0. Decryption of SMB3.1.1 will be in the next release.
- only supports AES-128-CCM
- Due to how the dissector works, the trace requires a Tree Connect packet to be present in the trace being decrypted (done using the right session id).
Obtaining the session key
The linux kernel client (cifs.ko) can be configured to dump the cryptographic keys it generates (visible in dmesg output) via the build time option CONFIG_CIFS_DEBUG_DUMP_KEYS. Keep in mind this is a debugging option and it should not be set on a production system.
You can set this option in your .config file or find it in make menuconfig by going in:
- File systems
- Network File Systems
- SMB3 and CIFS support (advanced network filesystem)
- Enable CIFS debugging routines > Dump encryption keys for offline decryption (Unsafe).
- SMB3 and CIFS support (advanced network filesystem)
- Network File Systems
Once enabled, you can mount a share and pass the mount options vers=3 or vers=3.11 to make sure the connection uses SMB3 and seal to require encryption.
If the connection reaches the Tree Connect stage you should be able to see this in the kernel console (via dmesg) for each session established:
CIFS VFS: generate_smb3signingkey: dumping generated AES session keys CIFS VFS: Session Id bc 1a fc 0d 00 00 00 00 CIFS VFS: Session Key 34 57 e1 90 4b 94 3a 0d 09 be 22 b9 b9 cf c7 4c CIFS VFS: Signing Key 28 bf a3 71 39 e5 05 71 c6 15 58 f3 cf 42 3f 0e CIFS VFS: ServerIn Key 79 2a 9a 40 1e cf 16 52 41 a5 ec bd 1c e5 84 17 CIFS VFS: ServerOut Key c0 73 c8 1d 36 f5 74 3e ef 6e c1 9d 5c e5 cb 71
Setting the key
Note: The kernel prints the Session Id as it is on the wire (little endian). Wireshark decryption expects the Session Id as it is on the wire as well, so you should be able to copy/paste from one to the other (despite showing the Session ID field decoded when dumping packets).
- Just copy the Session Id and Session Key into wireshark (see screenshot).
- Alternatively you can pass them via the command line (works with wireshark and tshark):
tshark -ouat:smb2_seskey_list:3d00009400480000,28f2847263c83dc00621f742dd3f2e7b -r smb3-aes-128-ccm.pcap
Using a keytab
Prerequisite
You only need to do that once:
- Open Wireshark
- Goto: Preferences -> Protocols -> KRB5
- Select: Try to decrypt encrypted Kerberos blobs
Basic decryption
The easiest way, on a unix-like system is to run
wireshark -K <PATH TO KEYTAB> <PCAP FILE>
Note: Wireshark for 64-bit Windows (GUI or command-line) doesn't like the -K flag, run the 32-bit Windows version instead.
The other way, is to specify the keytab in Preferences -> Protocols -> KRB5 -> keytab path
How to extract the keytab?
See: How to extract a keytab from a windows domain with Samba
Decrypted AES DCE/RPC
To do this, you will need metze's wireshark branch, and his patched verison of MIT Kerberos
http://gitweb.samba.org/?p=metze/wireshark/wip.git;a=shortlog;h=refs/heads/ws-metze-gssapi git://git.samba.org/metze/wireshark/wip.git ws-metze-gssapi
Also, you will need to apply krb5-1.6-wireshark-hack-01.diff to MIT Kerberos 1.6, and set LD_LIBRARY_PATH to wherever you put the result.