Time Synchronisation: Difference between revisions
Mmuehlfeld (talk | contribs) (Complete re-write of the HowTo, incl. client configuration, etc.) |
Mmuehlfeld (talk | contribs) m (Indent image) |
||
| Line 227: | Line 227: | ||
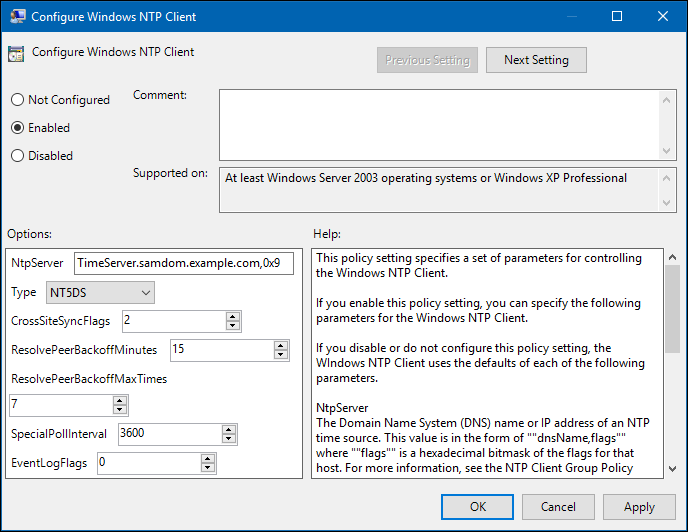
* Edit the „Configure Windows NTP Client“ policy: |
* Edit the „Configure Windows NTP Client“ policy: |
||
[[Image:GPO_Windows_NTP_Client_Options.png]] |
:[[Image:GPO_Windows_NTP_Client_Options.png]] |
||
:This example changes the NTP server setting to a different DC, that provides time, but is not owner of the PDC role. For further explanations on the possible options, see the description in the policy and, visit http://technet.microsoft.com/de-de/library/cc779145%28v=ws.10%29.aspx. |
:This example changes the NTP server setting to a different DC, that provides time, but is not owner of the PDC role. For further explanations on the possible options, see the description in the policy and, visit http://technet.microsoft.com/de-de/library/cc779145%28v=ws.10%29.aspx. |
||
Revision as of 16:02, 4 May 2014
Introducion
In an Active Directory, an accurate time syncronisation is required and critical like DNS E. g. Kerberos relies on correct timestamps to prevent replay attacks and AD needs them for resolving replication conflicts.
The maximum time tolerance in an Active Directory is 5 minutes per default. If e. g. your clients clock differs more than that to your servers clock, accessing the server is denied.
In an Active Directory, the Domain Controller with the PDC Emulator role is considered as the default time source in a forest. See http://technet.microsoft.com/en-us/library/cc773013%28v=ws.10%29.aspx#w2k3tr_times_how_izcr for information about time syncronisation in an AD DS hierarchy.
General information
Server information used in this HowTo
Inside this HowTo, we will be using the following configuration/settings:
Installation Directory: /usr/local/samba/ Domain Controller (owner of PDC role): DC1.samdom.example.com Domain Controller (not owner of PDC role): DC2.samdom.example.com
Limitations of ntpd with old clients
Please note that ntpd from ntp.org Samba interface with, does not support authenticated time to Windows 2000 clients! This is due to these clients not behaving as the ntpd server expects. As these clients are now very old and unsupported, you may need to find another way to keep these clocks in sync.
Configuring Time Syncronisation on a DC
Requirements
- ntpd >= 4.2.6 with enabled signed ntp support
Installation
- Install ntpd from your distributions repository. Make sure, that it was compiled using the „--enable-ntp-signd“ option!
- Compile by yourself (Add „--enable-ntp-signd“ to the „configure“ options!).
Check Samba AD DC socket permissions
Check that the socket permissions are set correct. It must be readable by the account your ntpd uses and should not be accessable by other:
# ls -ld /usr/local/samba/var/lib/ntp_signd/ drwxr-x--- 2 root ntp 4096 1. May 09:30 /usr/local/samba/var/lib/ntp_signd/
Setup ntpd.conf
# Local clock (this is not the localhost address!) server 127.127.1.0 fudge 127.127.1.0 stratum 10 # The source, where we are receiving the time from server 0.pool.ntp.org iburst prefer driftfile /var/lib/ntp/ntp.drift logfile /var/log/ntp ntpsigndsocket /usr/local/samba/var/lib/ntp_signd/ # Access control # Default restriction: Only allow querying time (incl. ms-sntp) from this machine restrict default kod nomodify notrap nopeer mssntp # Allow everything from localhost restrict 127.0.0.1 # Allow that our time source can only provide time and do nothing else restrict 0.pool.ntp.org mask 255.255.255.255 nomodify notrap nopeer noquery
For further information about ntpd access control, see http://support.ntp.org/bin/view/Support/AccessRestrictions
SELinux Labeling and Policy (optional)
Set policy for Windows client time sync:
# chcon -u system_u -t ntpd_t /usr/local/samba/var/lib/ntp_signd
Make the policy permanent
# semanage -a -t ntpd_t "/usr/local/samba/var/lib/ntp_signd"
Verify the change
# cat /etc/selinux/targeted/contexts/files/file_contexts.local
You should see a line like:
/usr/local/samba/var/lib/ntp_signd system_u:object_r:ntpd_t:s0
The below policy file is based on 4.1.6 on RHEL 6.5 and should be for reference only. Always run the below egrep command, after you have a base policy file created. Then stop / start ntpd and Samba AD services on your system and add to the base policy until competed.
egrep "samba|ntpd" /var/log/audit/audit.log | audit2allow
If all is fine, you'll see this for each "allow" line below in the policy file.
#!!! This avc is allowed in the current policy allow ntpd_t self:capability sys_admin; etc.
samba4.te policy:
module samba4 1.0;
require {
type ntpd_t;
type usr_t;
type initrc_t;
type fs_t;
type setfiles_t;
type lib_t;
type unconfined_t;
type locate_t;
class dir write;
class dir search;
class dir open;
class dir read;
class dir getattr;
class dir remove_name;
class dir add_name;
class dir relabelto;
class unix_stream_socket connectto;
class sock_file write;
class sock_file create;
class sock_file unlink;
class filesystem associate;
class capability sys_admin;
}
#============= initrc_t ==============
allow initrc_t ntpd_t:dir { write remove_name add_name };
allow initrc_t ntpd_t:sock_file create;
allow initrc_t ntpd_t:sock_file unlink;
#============= ntpd_t ==============
allow ntpd_t usr_t:sock_file write;
allow ntpd_t initrc_t:unix_stream_socket connectto;
allow ntpd_t fs_t:filesystem associate;
allow ntpd_t lib_t:sock_file write;
allow ntpd_t unconfined_t:unix_stream_socket connectto;
allow ntpd_t self:sock_file write;
allow ntpd_t self:capability sys_admin;
#============= locate_t ==============
allow locate_t ntpd_t:dir { read getattr open search };
#============= setfiles_t ==============
allow setfiles_t ntpd_t:dir relabelto;
Check and load policy:
$ checkmodule -M -m -o samba4.mod samba4.te $ semodule_package -o samba4.pp -m samba4.mod $ semodule -i samba4.pp
Configuring Time Syncronisation on Samba Member Servers
Requirements
Installation
- Install ntpd from your distributions repository.
- Compile it by yourself.
Setup ntpd.conf
# Local clock (this is not the localhost address!) server 127.127.1.0 fudge 127.127.1.0 stratum 10 # The source, where we are receiving the time from (PDC) server DC1.samdom.example.com iburst prefer driftfile /var/lib/ntp/ntp.drift logfile /var/log/ntp # Access control # Default restriction restrict default ignore # Allow everything from localhost restrict 127.0.0.1 # Allow that our time source can only provide time and do nothing else restrict DC1.samdom.example.com mask 255.255.255.255 nomodify notrap nopeer noquery
For further information about ntpd access control, see http://support.ntp.org/bin/view/Support/AccessRestrictions
Configuring Time Syncronisation on Windows Clients
Default behaviour
Per default, Windows clients in an Active Directory, automatically syncronize their time with the DC, owning the „PDC“ role. If you don't want to use a different source, configure fallback time server, etc. you don't have to take action.
Setting user defined time source(s) and options
If you require your Windows clients to syncronize time with a different server than your DC owning the PDC role, you can configure this via Group Policies. Using the following way, you can define multiple time servers and adjust time sycronisation related options:
- Create a new Group Policy Object in the Group Policy Management Console and edit it.
- In the Group Policy Management Editor, go to „Computer Configuration“ / „Administrative Templates“ / „System“ / „Windows Time Service“ / „Time Providers“.
- Edit the „Configure Windows NTP Client“ policy:
- This example changes the NTP server setting to a different DC, that provides time, but is not owner of the PDC role. For further explanations on the possible options, see the description in the policy and, visit http://technet.microsoft.com/de-de/library/cc779145%28v=ws.10%29.aspx.
- Save the GPO and link it to the desired OU.
Configuring Time Syncronisation on Linux Clients
See Configuring Time Syncronisation on Samba Member Servers.