Setting up a Share Using Windows ACLs: Difference between revisions
Mmuehlfeld (talk | contribs) m (Updated link) |
mNo edit summary |
||
| (54 intermediate revisions by 3 users not shown) | |||
| Line 1: | Line 1: | ||
= Introduction = |
= Introduction = |
||
Extended access control lists (ACL) enable you to set permissions on shares, files, and directories using Windows ACLs and applications. Samba supports shares using extended ACLs on: |
|||
On every Samba host you can, as on any MS Windows OS, share a folder to make it accessible for other users. There's no difference if this host is a Samba [[Active_Directory_Domain_Controller|Active Directory Domain Controller]], a [[Setting_up_Samba_as_a_Domain_Member|Domain Member]] or a [[Setting_up_Samba_as_a_Standalone_Server|Standalone Server]]. File shares can be setup in two ways: Set [[Setting_up_a_Share_using_POSIX_ACLs|completely via smb.conf parameters and POSIX ACLs]] or to be managed using Windows tools and ACLs. The latter is described in this documentation. |
|||
* Domain members |
|||
* Active Directory (AD) domain controllers (DC) |
|||
* NT4 primary domain controller (PDC) |
|||
* NT4 backup domain controllers (BDC) |
|||
* Standalone hosts |
|||
'''Important note:''' Samba Active Directory Domain Controllers have extended ACL support enabled globally, to enable management of share permissions and ACLs via Windows! |
|||
= Preparing the Host = |
|||
You need to set up Samba before you are able to create a share. Depending on what type of Samba server you require, see: |
|||
= Preparatory work = |
|||
* [[Setting_up_Samba_as_a_Domain_Member|Setting up Samba as a Domain Member]] |
|||
* [[Active_Directory_Domain_Controller|Setting up Samba as AD DC]] |
|||
* [[Setting_up_Samba_as_an_NT4_PDC_(Quick_Start)|Setting up Samba as an NT4 PDC (Quick Start)]] |
|||
* [[Setting_up_Samba_as_an_NT4_BDC|Setting up Samba as an NT4 BDC]] |
|||
* [[Setting_up_Samba_as_a_Standalone_Server|Setting up Samba as a Standalone Server]] |
|||
== File system support == |
|||
Check that the filesystem, the share will reside on, supports the "user" and "system" xattr name spaces. It also requires ACL and XATTR support. See [[File_System_Support|File system support]] for further details. |
|||
== File System Support == |
|||
The file system, the share will be created on, must support: |
|||
* user and system <code>xattr</code> name spaces. |
|||
* extended access control lists (ACL). |
|||
For further details, see [[File_System_Support|File system support]]. |
|||
== Samba ACL support == |
|||
Make sure, Samba was compiled with ACL support. Check with the following command: |
|||
== Samba Extended ACL Support == |
|||
To create a share with extended access control list (ACL) support, the <code>smbd</code> service must have been built with ACL support enabled. A Samba host working as an Active Directory (AD) domain controller (DC), is always enabled with extended ACL support. |
|||
To verify if Samba has been built with ACL support, enter: |
|||
# smbd -b | grep HAVE_LIBACL |
# smbd -b | grep HAVE_LIBACL |
||
HAVE_LIBACL |
HAVE_LIBACL |
||
If no output is displayed: |
|||
If "HAVE_LIBACL" is not found, then Samba was compiled without extended ACL support. If you compiled Samba yourself, see [[Samba_Dependencies_Required_to_Build_Samba|Samba Dependencies Required to Build Samba]]. |
|||
* Samba was built using the <code>--with-acl-support=no</code> parameter. |
|||
* The Samba <code>configure</code> script was unable to locate the required libraries for ACL support. For details, see [[Package Dependencies Required to Build Samba]]. |
|||
== Enable extended ACL support in smb.conf == |
|||
''Only add The following lines to a Domain Member. Do not add them to a Domain Controller, they are already set in its code.'' |
|||
== Enable Extended ACL Support on a Unix domain member == |
|||
Add the following to your [global] section of your smb.conf: |
|||
Ideally you have a system that supports [[NFS4_ACL_overview|NFS4 ACLs]]. The following example is for systems like Linux, where you don't have those kind of ACLs. To configure shares using extended access control lists (ACL) on a Unix domain member, you must enable the support in the <code>smb.conf</code> file. To enable extended ACL support globally, add the following settings to the <code>[global]</code> section of your <code>smb.conf</code> file: |
|||
vfs objects = acl_xattr |
|||
map acl inherit = yes |
|||
store dos attributes = yes |
|||
vfs objects = acl_xattr |
|||
See the smb.conf man page for further details on the parameters. |
|||
map acl inherit = yes |
|||
# the next line is only required on Samba versions less than 4.9.0 |
|||
store dos attributes = yes |
|||
{{Imbox |
|||
== SeDiskOperatorPrivilege == |
|||
| type = important |
|||
| text = On a Samba Active Directory (AD) domain controller (DC), extended ACL support is automatically enabled globally. You must not enable the support manually. |
|||
}} |
|||
Alternatively, to enable extended ACL support only for a specific share, add the parameters to the share's section. |
|||
Accounts that should be able to configure share permissions, require the privilege "SeDiskOperatorPrivilege". To view the current privilege list on a host, run |
|||
For further details about the parameters, see the <code>smb.conf(5)</code> man page. |
|||
# net rpc rights list accounts -U'SAMDOM\administrator' |
|||
You may have the following error with the previous command: |
|||
Could not connect to server 127.0.0.1 |
|||
Connection failed: NT_STATUS_CANT_ACCESS_DOMAIN_INFO |
|||
If that's the case, retry by specifying a domain controller with the -I option: |
|||
# net rpc rights list accounts -U'SAMDOM\administrator' -I dc1.samdom.example.com |
|||
== Granting the <code>SeDiskOperatorPrivilege</code> Privilege == |
|||
In the following, we will grant the privilege to the group "Domain Admins", but before doing this, make sure that the group is available to the local OS by [[Name_service_switch_(NSS)|NSS]]; usually via [[Winbindd|Winbindd]]: |
|||
By default, the BUILTIN\Administrators is the only holder of the SeDiskOperatorPrivilege privilege. |
|||
# getent group "Domain Admins" |
|||
domain admins:x:10001: |
|||
However, the BUILTIN\Administrators group members are: Administrator, Domain Admins and Enterprise Admins. These will inherit the privileges and permissions that BUILTIN\Administrators holds. |
|||
If you don't get an output showing the queried name and its ID, there may be something wrong in your [[Name_service_switch_(NSS)|NSS configuration]] or if you are using Winbindd with [[Idmap_config_ad|RFC2307 (idmap_ad)]], you might not have an ID assigned (see [[User_and_group_management|User and group management]] for how to administer Unix Attributes in an AD). If the "Domain Admins" group is available to the OS, you can grant the SeDiskOperatorPrivilege privilege to (add the "-I dc1.samdom.example.com" if you had the previous error with NT_STATUS_CANT_ACCESS_DOMAIN_INFO): |
|||
This means that if you use 'Administrator', a member of 'Domain Admins' or 'Enterprise Admins' when logged into Windows, then you do not need to grant the <code>SeDiskOperatorPrivilege</code> at all, it is inherited from BUILTIN\Administrators. |
|||
# net rpc rights grant 'SAMDOM\Domain Admins' SeDiskOperatorPrivilege -U'SAMDOM\administrator' |
|||
Enter SAMDOM\administrator's password: |
|||
Successfully granted rights. |
|||
= Adding a new share = |
|||
{{Imbox |
|||
* Create the new shared folder, if it doesn't already exist |
|||
| type = note |
|||
| text = Only users or groups that are known to Unix can be used. This means that if you use the winbind 'ad' backend on Unix domain members, you must add a uidNumber attribute to users, or a gidNumber to groups in AD. |
|||
}} |
|||
{{Imbox |
|||
| type = note |
|||
| text = If you use the winbind 'ad' backend on Unix domain members and you add a gidNumber attribute to the <code>Domain Admins</code> group in AD, you will break the mapping in <code>idmap.ldb</code>. <code>Domain Admins</code> is mapped as <code>ID_TYPE_BOTH</code> in <code>idmap.ldb</code>, this is to allow the group to own files in <code>Sysvol</code> on a Samba AD DC. It is suggested you create a new AD group (<code>Unix Admins</code> for instance), give this group a <code>gidNumber</code> attribute and add it to the <code>Administrators</code> group and then, on Unix, use the group wherever you would normally use <code>Domain Admins</code>. |
|||
}} |
|||
If you are using the 'ad' winbind idmap backend, then you should use the 'Unix Admins' group you were advised to create above. However, if you use any other winbind idmap backend (autorid or rid, for instance), then you can use the 'Domain Admins' group. |
|||
{{Imbox |
|||
| type = note |
|||
| text = It is recommended to grant the privilege to a group instead of individual accounts. This enables you to add and revoke the privilege by updating the group membership. |
|||
}} |
|||
To list all users and groups having the <code>SeDiskOperatorPrivilege</code> privilege granted, enter: |
|||
# net rpc rights list privileges SeDiskOperatorPrivilege -U "SAMDOM\administrator" |
|||
Enter administrator's password: |
|||
SeDiskOperatorPrivilege: |
|||
BUILTIN\Administrators |
|||
{{Imbox |
|||
| type = important |
|||
| text = If you need to grant the <code>SeDiskOperatorPrivilege</code> privilege, it must be done on the Samba server that holds the share. |
|||
}} |
|||
= Adding a Share = |
|||
To share the <code>/srv/samba/Demo/</code> directory using the <code>Demo</code> share name: |
|||
* As the <code>root</code> user, create the directory: |
|||
# mkdir -p /srv/samba/Demo/ |
# mkdir -p /srv/samba/Demo/ |
||
* To enable accounts other than the domain user <code>Administrator</code> to set permissions on Windows, grant <code>Full control</code> (<code>rwx</code>) to the user or group you granted the <code>SeDiskOperatorPrivilege</code> privilege. For example (if using the 'ad' backend): |
|||
* In order to allow a user or group to modify permissions, "Full control" is required. If you haven't modified it, the default value of "acl map full control" is "yes", this defines that "rwx" (read-write-execute) is mapped to "Full control". Accordingly to allow members of the "Domain Admins" group to edit permissions via Windows, we need to set the following: |
|||
# |
# chown root:"Unix Admins" /srv/samba/Demo/ |
||
# |
# chmod 0770 /srv/samba/Demo/ |
||
* Otherwise for any other backend: |
|||
* Add the new share to your smb.conf. No further parameters other than the following are required or suggested (e. g. "force user/group" is not compatible with the vfs objects "acl_xattr" and can cause "Access denied" errors)! |
|||
# chown root:"Domain Admins" /srv/samba/Demo/ |
|||
# chmod 0770 /srv/samba/Demo/ |
|||
* Add the <code>[Demo]</code> share definition to your <code>smb.conf</code> file: |
|||
[Demo] |
[Demo] |
||
| Line 83: | Line 141: | ||
read only = no |
read only = no |
||
: Further share-specific settings and file system permissions are set using the Windows utilities. |
|||
* Reload Samba |
|||
# smbcontrol all reload-config |
|||
:{{Imbox |
|||
| type = note |
|||
| text = If you set the shares permissions from Windows (The recommended way), you can add the line <code>'acl_xattr:ignore system acls = yes'</code> to your share. If the line is added, Samba will ignore the standard Unix system ACL's (ugo). Once the line is added, running <code>setfacl</code> on the shares directory will not show any permission modifications you may have made from Windows. '''You must not add this line until you have set up the share permissions from Windows, otherwise you may find that you are denied permission to change the permissions from Windows.'''. Only add the line if you will only connect to share via Samba. |
|||
}} |
|||
:{{Imbox |
|||
| type = important |
|||
| text = Do not set <code>ANY</code> additional share parameters. Adding any additional parameters to the share definition can prevent you from configuring or using the share. |
|||
}} |
|||
= Setup share permissions (optional) = |
|||
* Log on to a Windows machine, using an account that is a member of the "Domain Admins" group |
|||
* Open the Start Menu, search for "Computer Management" and open the program |
|||
* Reload the Samba configuration: |
|||
* In the menu bar go to "Action" / "Connect to another computer" |
|||
# smbcontrol all reload-config |
|||
* Enter the name of the Samba host on which you want to edit the share permissions |
|||
= Setting Share Permissions and ACLs = |
|||
* Navigate to "System Tools" / "Shared Folders" / "Shares" and select the desired share |
|||
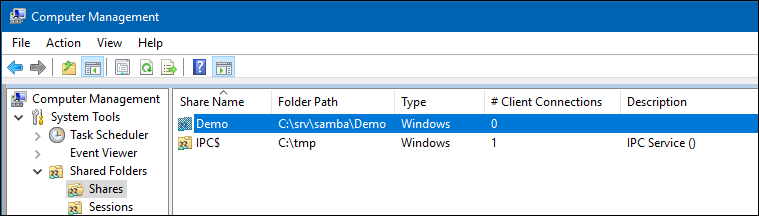
When you configure a share with extended access control lists (ACL) support, you set the share permissions using Windows utilities instead of adding parameters to the share section in the <code>smb.conf</code> file. |
|||
To set permissions and ACLs on the <code>Demo</code> share: |
|||
* Log on to a Windows host using the <code>SAMDOM\Administrator</code> account or an account that is a member of the group that is set as the shares group e.g. <code>SAMDOM\john</code> where <code>john</code> is a member of <code>Domain Admins</code>. |
|||
* Click <code>Start</code>, enter <code>Computer Management</code>, and start the application. |
|||
* Select <code>Action</code> / <code>Connect to another computer</code>. |
|||
* Enter the name of the Samba host and click <code>OK</code> to connect the console to the host. |
|||
* Open the <code>System Tools</code> / <code>Shared Folders</code> / <code>Shares</code> menu entry. |
|||
:[[Image:Computer_Management_Shares.png]] |
:[[Image:Computer_Management_Shares.png]] |
||
* Right-click to the share name and choose "Properties" |
|||
* Go to the "Share Permissions" tab and define who is allowed to connect to the share |
|||
:[[Image:Demo_Share_Permissions.png]] |
|||
* Right-click to the share and select <code>Properties</code>. |
|||
* Save the changes by closing the windows with "OK" |
|||
{{Imbox |
|||
| type = note |
|||
| text = Checking and/or changing the permissions on the 'Share Permissions' tab should not be required, only carry this out if you are having problems, better still, consult the samba mailing list before attempting to use the 'Share Permissions' tab. |
|||
}} |
|||
{{Imbox |
|||
| type = note |
|||
| text = Only users and groups that have been granted the <code>SeDiskOperatorPrivilege</code> privilege can configure the Share Permissions tab. |
|||
}} |
|||
= Set ACLs on the root of a share = |
|||
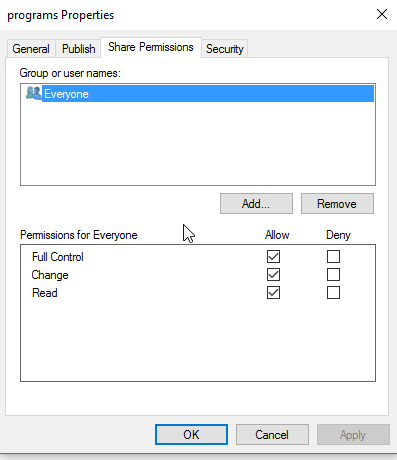
* Select the <code>Share Permissions</code> tab and check the share permissions, you need to see just <code>Everyone</code>. For example: |
|||
* Log on to a Windows machine, using an account that is a member of the "Domain Admins" group |
|||
:[[Image:share.png]] |
|||
{{Imbox |
|||
* Open the Start Menu, search for "Computer Management" and open the program |
|||
| type = important |
|||
| text = If the permissions are as above, do not change anything, if not, change it to just allow <code>Everyone</code> : <code>Full Control, Change and Read</code>. You only make changes to the <code>Security</code> tab. |
|||
}} |
|||
: Samba stores the share tab permissions in the <code>/usr/local/samba/var/locks/share_info.tdb</code> database. |
|||
* In the menu bar go to "Action" / "Connect to another computer" |
|||
* Enter the name of the Samba host on which you want to edit the share permissions |
|||
* Navigate to "System Tools" / "Shared Folders" / "Shares" and select the desired share |
|||
:[[Image:Computer_Management_Shares.png]] |
|||
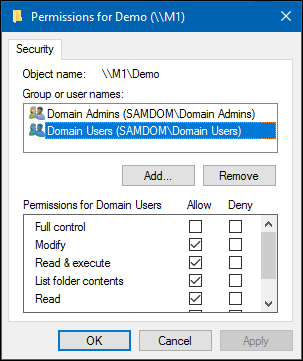
* Select the <code>Security</code> tab to make any required permission changes. |
|||
* Right-click to the share name and choose "Properties" |
|||
{{Imbox |
|||
| type = note |
|||
| text = Only the user or members of the group that are set as owner:group set on the servers share directory can configure the Security tab. |
|||
}} |
|||
* Click the <code>Edit</code> button and set the file system ACLs on the share's root directory. For example: |
|||
* Go to the "Security" tab, click the "Edit" button and configure the desired Windows ACLs |
|||
:[[Image:Demo_Share_Security.png]] |
:[[Image:Demo_Share_Security.png]] |
||
: For details about using the <code>SYSTEM</code> account on a Samba share see [[The SYSTEM Account]]. |
|||
* Save the changes by closing the windows with "OK" |
|||
: For details where the ACLs are stored, see [[#File_System_ACLs_in_the_Back_End|File System ACLs in the Back End]]. |
|||
* Click the <code>Add</code> button. |
|||
* Click <code>Advanced</code> button |
|||
* Click <code>Find Now</code> |
|||
* Select a user or group from the list, <code>Domain Users</code> for instance. |
|||
= Set ACLs on subfolders of a share = |
|||
* Click <code>OK</code> |
|||
* Log on to a Windows machine, using an account that is a member of the "Domain Admins" group |
|||
* Click <code>OK</code> |
|||
* Navigate to the folder of which you want to change the permissions |
|||
* Select permissions to grant, <code>Full control</code> for instance. |
|||
* Right-click to the folder and choose "Properties" |
|||
* A windows security box should open, asking if you want to continue, Click <code>Yes</code> |
|||
* Go to the "Security" tab and click the "Edit" button. |
|||
* If you check the list of <code>Group or user names</code>, you should find <code>Domain Users</code> listed |
|||
* Change the permissions to your needs |
|||
* Click <code>OK</code> to close the <code>Permissions for Demo</code> window. |
|||
* Click <code>OK</code> to store the updated settings. |
|||
For further details about configuring share permissions and ACLs, see the Windows documentation. |
|||
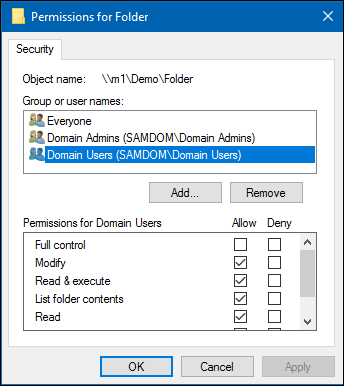
= Setting ACLs on a Folder = |
|||
To set file system permissions on a folder located on a share that uses extended access control lists (ACL): |
|||
* Log on to a Windows host using an account that has <code>Full control</code> on the folder you want to modify the file system ACLs. |
|||
* Navigate to the folder. |
|||
* Right-click to the folder and select <code>Properties</code>. |
|||
* Select the <code>Security</code> tab and click the <code>Edit</code> button. |
|||
* Set the permission. For example: |
|||
:[[Image:Folder_Permissions.png]] |
:[[Image:Folder_Permissions.png]] |
||
: For details about using the <code>SYSTEM</code> account on a Samba share see [[The SYSTEM Account]]. |
|||
* Save the changes by closing the windows with "OK" |
|||
: For details where the ACLs are stored, see [[#File_System_ACLs_in_the_Back_End|File System ACLs in the Back End]]. |
|||
* Click <code>OK</code> to close the <code>Permissions for Folder</code> window. |
|||
* Click <code>OK</code> to store the updated settings. |
|||
For further details about setting ACLs, see the Windows documentation. |
|||
= Troubleshooting = |
|||
In certain situations, configuration parameters which were commonly used on [[Setting_up_a_Share_using_POSIX_ACLs|shares with POSIX ACLs]], such as "force group" or "force user", may lead to "Access denied" errors when trying to set permissions on a new share or other complications, such as losing the ability to even see the "Security" tab. You may find, even after correcting the issues, that the problems may persist, even after removing and re-adding the share properly. In such cases, it may be helpful to manually wipe out all ACLs on the share and recursively re-grant full control to the Domain Admins group with the setfacl command as follows (need to run as root): |
|||
# setfacl -R -b /srv/samba/Demo/ |
|||
# setfacl -R -b /srv/samba/Demo/* |
|||
# setfacl -R -m default:group:"Domain Admins":rwx /srv/samba/Demo/ |
|||
= File System ACLs in the Back End = |
|||
Samba stores the file system permissions in extended file system access control lists (ACL) and in an extended attribute. For example: |
|||
* To list the extended ACLs of the <code>/srv/samba/Demo/</code> directory, enter: |
|||
# getfacl /srv/samba/Demo/ |
|||
# file: srv/samba/Demo/ |
|||
# owner: root |
|||
# group: root |
|||
user::rwx |
|||
user:root:rwx |
|||
group::--- |
|||
group:root:--- |
|||
group:domain\040users:rwx |
|||
group:unix\040admins:rwx |
|||
mask::rwx |
|||
other::--- |
|||
default:user::rwx |
|||
default:user:root:rwx |
|||
default:group::--- |
|||
default:group:root:--- |
|||
default:group:domain\040users:rwx |
|||
default:group:unix\040admins:rwx |
|||
default:mask::rwx |
|||
default:other::--- |
|||
* To list the <code>security.NTACL</code> extended attribute of the <code>/srv/samba/Demo/</code> directory, enter: |
|||
# getfattr -n security.NTACL -d /srv/samba/Demo/ |
|||
# file: srv/samba/Demo/ |
|||
security.NTACL=0sBAAEAAAAAgAEAAIAAQC4zK0lHchKFvwXwbPR/h8P8sXMj5dNIT5QQuWsYwO3RAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAcG9zaXhfYWNsAEbGxuGu39MBuiZRk2pYxeL5ZWc4au0ikqRAk53MkjVd2b4quyk2WwcAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEABJy0AAAA0AAAAAAAAADsAAAAAQUAAAAAAAUVAAAASSVmaZneO8cxOHk/9AEAAAEFAAAAAAAFFQAAAEklZmmZ3jvHMTh5P0oIAAACAMQABwAAAAALFACpABIAAQEAAAAAAAEAAAAAAAAUAAAAEAABAQAAAAAAAQAAAAAACxQA/wEfAAEBAAAAAAADAAAAAAALFACpABIAAQEAAAAAAAMBAAAAAAMkAP8BHwABBQAAAAAABRUAAABJJWZpmd47xzE4eT9KCAAAAAAkAP8BHwABBQAAAAAABRUAAABJJWZpmd47xzE4eT/0AQAAAAMkAL8BEwABBQAAAAAABRUAAABJJWZpmd47xzE4eT8BAgAA |
|||
The previous example of file system ACLs and the extended attribute is mapped to the following Windows ACLs: |
|||
{| class="wikitable" |
|||
!Principal |
|||
!Permissions |
|||
!Applies to |
|||
|- |
|||
|Domain Users (SAMDOM\Domain Users) |
|||
|Modify, Read & execute, List folder contents, Read, Write |
|||
|(This folder, subfolders and files) |
|||
|- |
|||
|Unix Admins (SAMDOM\Unix Admins) |
|||
|Full control |
|||
|(This folder, subfolders and files) |
|||
|} |
|||
* To get the ACL in a more readable form, enter: |
|||
# samba-tool ntacl get /usr/local/samba/var/locks/sysvol --as-sddl |
|||
# O:BAG:SYD:PAI(A;OICIIO;WOWDGRGWGX;;;CO)(A;OICIIO;GRGX;;;AU)(A;;0x001200a9;;;AU)(A;OICIIO;GA;;;SY)(A;;0x001f01ff;;;SY)(A;OICIIO;WOWDGRGWGX;;;BA)(A;;0x001e01bf;;;BA)(A;OICIIO;GRGX;;;SO)(A;;0x001200a9;;;SO) |
|||
= Troubleshooting = |
|||
For troubleshooting, see: |
|||
* [[Troubleshooting_Samba_Domain_Members|Troubleshooting Samba Domain Members]] |
|||
* [[Samba_AD_DC_Troubleshooting|Samba AD DC Troubleshooting]] |
|||
= Related documentation = |
|||
The following documentation discusses related topics: |
|||
* [[User_home_drives|Setting up home drives]] |
|||
---- |
|||
* [[Implementing_roaming_profiles|Implementing Windows roaming profiles]] |
|||
[[Category:Active Directory]] |
|||
[[Category:Domain Members]] |
|||
[[Category:File Serving]] |
|||
[[Category:NT4 Domains]] |
|||
Latest revision as of 18:41, 26 June 2024
Introduction
Extended access control lists (ACL) enable you to set permissions on shares, files, and directories using Windows ACLs and applications. Samba supports shares using extended ACLs on:
- Domain members
- Active Directory (AD) domain controllers (DC)
- NT4 primary domain controller (PDC)
- NT4 backup domain controllers (BDC)
- Standalone hosts
Preparing the Host
You need to set up Samba before you are able to create a share. Depending on what type of Samba server you require, see:
- Setting up Samba as a Domain Member
- Setting up Samba as AD DC
- Setting up Samba as an NT4 PDC (Quick Start)
- Setting up Samba as an NT4 BDC
- Setting up Samba as a Standalone Server
File System Support
The file system, the share will be created on, must support:
- user and system
xattrname spaces. - extended access control lists (ACL).
For further details, see File system support.
Samba Extended ACL Support
To create a share with extended access control list (ACL) support, the smbd service must have been built with ACL support enabled. A Samba host working as an Active Directory (AD) domain controller (DC), is always enabled with extended ACL support.
To verify if Samba has been built with ACL support, enter:
# smbd -b | grep HAVE_LIBACL HAVE_LIBACL
If no output is displayed:
- Samba was built using the
--with-acl-support=noparameter. - The Samba
configurescript was unable to locate the required libraries for ACL support. For details, see Package Dependencies Required to Build Samba.
Enable Extended ACL Support on a Unix domain member
Ideally you have a system that supports NFS4 ACLs. The following example is for systems like Linux, where you don't have those kind of ACLs. To configure shares using extended access control lists (ACL) on a Unix domain member, you must enable the support in the smb.conf file. To enable extended ACL support globally, add the following settings to the [global] section of your smb.conf file:
vfs objects = acl_xattr map acl inherit = yes # the next line is only required on Samba versions less than 4.9.0 store dos attributes = yes
| On a Samba Active Directory (AD) domain controller (DC), extended ACL support is automatically enabled globally. You must not enable the support manually. |
Alternatively, to enable extended ACL support only for a specific share, add the parameters to the share's section.
For further details about the parameters, see the smb.conf(5) man page.
Granting the SeDiskOperatorPrivilege Privilege
By default, the BUILTIN\Administrators is the only holder of the SeDiskOperatorPrivilege privilege.
However, the BUILTIN\Administrators group members are: Administrator, Domain Admins and Enterprise Admins. These will inherit the privileges and permissions that BUILTIN\Administrators holds.
This means that if you use 'Administrator', a member of 'Domain Admins' or 'Enterprise Admins' when logged into Windows, then you do not need to grant the SeDiskOperatorPrivilege at all, it is inherited from BUILTIN\Administrators.
| Only users or groups that are known to Unix can be used. This means that if you use the winbind 'ad' backend on Unix domain members, you must add a uidNumber attribute to users, or a gidNumber to groups in AD. |
If you use the winbind 'ad' backend on Unix domain members and you add a gidNumber attribute to the Domain Admins group in AD, you will break the mapping in idmap.ldb. Domain Admins is mapped as ID_TYPE_BOTH in idmap.ldb, this is to allow the group to own files in Sysvol on a Samba AD DC. It is suggested you create a new AD group (Unix Admins for instance), give this group a gidNumber attribute and add it to the Administrators group and then, on Unix, use the group wherever you would normally use Domain Admins. |
If you are using the 'ad' winbind idmap backend, then you should use the 'Unix Admins' group you were advised to create above. However, if you use any other winbind idmap backend (autorid or rid, for instance), then you can use the 'Domain Admins' group.
| It is recommended to grant the privilege to a group instead of individual accounts. This enables you to add and revoke the privilege by updating the group membership. |
To list all users and groups having the SeDiskOperatorPrivilege privilege granted, enter:
# net rpc rights list privileges SeDiskOperatorPrivilege -U "SAMDOM\administrator" Enter administrator's password: SeDiskOperatorPrivilege: BUILTIN\Administrators
If you need to grant the SeDiskOperatorPrivilege privilege, it must be done on the Samba server that holds the share. |
To share the /srv/samba/Demo/ directory using the Demo share name:
- As the
rootuser, create the directory:
# mkdir -p /srv/samba/Demo/
- To enable accounts other than the domain user
Administratorto set permissions on Windows, grantFull control(rwx) to the user or group you granted theSeDiskOperatorPrivilegeprivilege. For example (if using the 'ad' backend):
# chown root:"Unix Admins" /srv/samba/Demo/ # chmod 0770 /srv/samba/Demo/
- Otherwise for any other backend:
# chown root:"Domain Admins" /srv/samba/Demo/ # chmod 0770 /srv/samba/Demo/
- Add the
[Demo]share definition to yoursmb.conffile:
[Demo]
path = /srv/samba/Demo/
read only = no
- Further share-specific settings and file system permissions are set using the Windows utilities.

If you set the shares permissions from Windows (The recommended way), you can add the line 'acl_xattr:ignore system acls = yes'to your share. If the line is added, Samba will ignore the standard Unix system ACL's (ugo). Once the line is added, runningsetfaclon the shares directory will not show any permission modifications you may have made from Windows. You must not add this line until you have set up the share permissions from Windows, otherwise you may find that you are denied permission to change the permissions from Windows.. Only add the line if you will only connect to share via Samba.

Do not set ANYadditional share parameters. Adding any additional parameters to the share definition can prevent you from configuring or using the share.
- Reload the Samba configuration:
# smbcontrol all reload-config
When you configure a share with extended access control lists (ACL) support, you set the share permissions using Windows utilities instead of adding parameters to the share section in the smb.conf file.
To set permissions and ACLs on the Demo share:
- Log on to a Windows host using the
SAMDOM\Administratoraccount or an account that is a member of the group that is set as the shares group e.g.SAMDOM\johnwherejohnis a member ofDomain Admins.
- Click
Start, enterComputer Management, and start the application.
- Select
Action/Connect to another computer.
- Enter the name of the Samba host and click
OKto connect the console to the host.
- Open the
System Tools/Shared Folders/Sharesmenu entry.
- Right-click to the share and select
Properties.
| Checking and/or changing the permissions on the 'Share Permissions' tab should not be required, only carry this out if you are having problems, better still, consult the samba mailing list before attempting to use the 'Share Permissions' tab. |
Only users and groups that have been granted the SeDiskOperatorPrivilege privilege can configure the Share Permissions tab. |
- Select the
Share Permissionstab and check the share permissions, you need to see justEveryone. For example:
If the permissions are as above, do not change anything, if not, change it to just allow Everyone : Full Control, Change and Read. You only make changes to the Security tab. |
- Samba stores the share tab permissions in the
/usr/local/samba/var/locks/share_info.tdbdatabase.
- Select the
Securitytab to make any required permission changes.
| Only the user or members of the group that are set as owner:group set on the servers share directory can configure the Security tab. |
- Click the
Editbutton and set the file system ACLs on the share's root directory. For example:
- For details about using the
SYSTEMaccount on a Samba share see The SYSTEM Account.
- For details where the ACLs are stored, see File System ACLs in the Back End.
- Click the
Addbutton.
- Click
Advancedbutton
- Click
Find Now
- Select a user or group from the list,
Domain Usersfor instance.
- Click
OK
- Click
OK
- Select permissions to grant,
Full controlfor instance.
- A windows security box should open, asking if you want to continue, Click
Yes
- If you check the list of
Group or user names, you should findDomain Userslisted
- Click
OKto close thePermissions for Demowindow.
- Click
OKto store the updated settings.
For further details about configuring share permissions and ACLs, see the Windows documentation.
Setting ACLs on a Folder
To set file system permissions on a folder located on a share that uses extended access control lists (ACL):
- Log on to a Windows host using an account that has
Full controlon the folder you want to modify the file system ACLs.
- Navigate to the folder.
- Right-click to the folder and select
Properties.
- Select the
Securitytab and click theEditbutton.
- Set the permission. For example:
- For details about using the
SYSTEMaccount on a Samba share see The SYSTEM Account.
- For details where the ACLs are stored, see File System ACLs in the Back End.
- Click
OKto close thePermissions for Folderwindow.
- Click
OKto store the updated settings.
For further details about setting ACLs, see the Windows documentation.
File System ACLs in the Back End
Samba stores the file system permissions in extended file system access control lists (ACL) and in an extended attribute. For example:
- To list the extended ACLs of the
/srv/samba/Demo/directory, enter:
# getfacl /srv/samba/Demo/ # file: srv/samba/Demo/ # owner: root # group: root user::rwx user:root:rwx group::--- group:root:--- group:domain\040users:rwx group:unix\040admins:rwx mask::rwx other::--- default:user::rwx default:user:root:rwx default:group::--- default:group:root:--- default:group:domain\040users:rwx default:group:unix\040admins:rwx default:mask::rwx default:other::---
- To list the
security.NTACLextended attribute of the/srv/samba/Demo/directory, enter:
# getfattr -n security.NTACL -d /srv/samba/Demo/ # file: srv/samba/Demo/ security.NTACL=0sBAAEAAAAAgAEAAIAAQC4zK0lHchKFvwXwbPR/h8P8sXMj5dNIT5QQuWsYwO3RAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAcG9zaXhfYWNsAEbGxuGu39MBuiZRk2pYxeL5ZWc4au0ikqRAk53MkjVd2b4quyk2WwcAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEABJy0AAAA0AAAAAAAAADsAAAAAQUAAAAAAAUVAAAASSVmaZneO8cxOHk/9AEAAAEFAAAAAAAFFQAAAEklZmmZ3jvHMTh5P0oIAAACAMQABwAAAAALFACpABIAAQEAAAAAAAEAAAAAAAAUAAAAEAABAQAAAAAAAQAAAAAACxQA/wEfAAEBAAAAAAADAAAAAAALFACpABIAAQEAAAAAAAMBAAAAAAMkAP8BHwABBQAAAAAABRUAAABJJWZpmd47xzE4eT9KCAAAAAAkAP8BHwABBQAAAAAABRUAAABJJWZpmd47xzE4eT/0AQAAAAMkAL8BEwABBQAAAAAABRUAAABJJWZpmd47xzE4eT8BAgAA
The previous example of file system ACLs and the extended attribute is mapped to the following Windows ACLs:
| Principal | Permissions | Applies to |
|---|---|---|
| Domain Users (SAMDOM\Domain Users) | Modify, Read & execute, List folder contents, Read, Write | (This folder, subfolders and files) |
| Unix Admins (SAMDOM\Unix Admins) | Full control | (This folder, subfolders and files) |
- To get the ACL in a more readable form, enter:
# samba-tool ntacl get /usr/local/samba/var/locks/sysvol --as-sddl # O:BAG:SYD:PAI(A;OICIIO;WOWDGRGWGX;;;CO)(A;OICIIO;GRGX;;;AU)(A;;0x001200a9;;;AU)(A;OICIIO;GA;;;SY)(A;;0x001f01ff;;;SY)(A;OICIIO;WOWDGRGWGX;;;BA)(A;;0x001e01bf;;;BA)(A;OICIIO;GRGX;;;SO)(A;;0x001200a9;;;SO)
Troubleshooting
For troubleshooting, see: