Group Policy: Difference between revisions
(→Policies: Add description of Sudo policy) |
|||
| Line 64: | Line 64: | ||
== Script Policies == |
== Script Policies == |
||
Script policies create cron jobs on client machines which execute the specified commands. Script policies are found in Computer Configuration > Policies > Administrative Templates > Samba > Scripts. |
Script policies create cron jobs on client machines which execute the specified commands. Script policies are found in Computer Configuration > Policies > Administrative Templates > Samba > Unix Settings > Scripts. |
||
To add a script policy, open the policy, enable it, and click ''Show''. In the dialog that appears, add the command to execute on the client. Click OK, then Apply to save the policy. |
To add a script policy, open the policy, enable it, and click ''Show''. In the dialog that appears, add the command to execute on the client. Click OK, then Apply to save the policy. |
||
| Line 72: | Line 72: | ||
Script policies are applied as cron jobs on the winbind client. |
Script policies are applied as cron jobs on the winbind client. |
||
linux-h7xz:~ # /usr/sbin/samba-gpupdate |
linux-h7xz:~ # /usr/sbin/samba-gpupdate --force |
||
linux-h7xz:~ # cat /etc/cron.daily/tmp6l0m809i |
linux-h7xz:~ # cat /etc/cron.daily/tmp6l0m809i |
||
#!/bin/sh |
#!/bin/sh |
||
whoami > /daily.log |
whoami > /daily.log |
||
== Sudoers Policies == |
|||
Sudoers policies add sudo rules to client machines. Sudoers policies are found in Computer Configuration > Policies > Administrative Templates > Samba > Unix Settings > Sudo Rights. |
|||
To add a sudo policy, open the policy, enable it, and click ''Show''. In the dialog that appears, add the sudo rules to the list. Click OK, then Apply to save the policy. |
|||
linux-h7xz:~ # /usr/sbin/samba-gpupdate --force |
|||
linux-h7xz:~ # cat /etc/sudoers.d/gp_eockoryg |
|||
### autogenerated by samba |
|||
# |
|||
# This file is generated by the gp_sudoers_ext Group Policy |
|||
# Client Side Extension. To modify the contents of this file, |
|||
# modify the appropriate Group Policy objects which apply |
|||
# to this machine. DO NOT MODIFY THIS FILE DIRECTLY. |
|||
# |
|||
tux ALL=(ALL) NOPASSWD: ALL |
|||
Revision as of 20:42, 7 August 2020
Introduction
This document describes how to manage winbind clients using Group Policy.
About Group Policy
Group Policy provides centralized management and configuration of operating system, application, and user settings. Policies are delivered to clients by listing them in LDAP, under groupPolicyContainer objects. These objects provide the gPCFileSysPath attribute, which points to policy information stored on the domains SYSVOL share.
Policies are enforced by winbind at a random interval between 90 and 120 seconds. Policies can be manually enforced using the samba-gpupdate --force command.
Configuring Group Policy
Enabling Group Policy in Winbind
To enable Group Policy application in winbind, set the global option apply group policies to yes.
apply group policies = yes
Installing Samba ADMX Templates for the Group Policy Management Console
In order to configure Samba Group Policies, you must first install the ADMX templates provided by Samba.
samba-tool gpo admxload -UAdministrator
The samba-tool gpo admxload command copies the Samba ADMX templates to the <domain>/Policies/PolicyDefinitions directory on the SYSVOL share.
Setting Samba Group Policy in the Group Policy Management Console
To set Samba Group Policy settings, open the Group Policy Management Console and either create a new Group Policy Object, or edit an existing one.
Creating a Group Policy Object
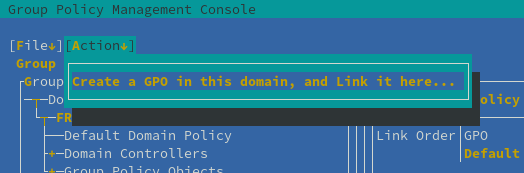
To create the Group Policy Object, highlight the domain or container where you want the object linked, then open the Action menu and select "Create a GPO in this domain, and Link it here".
Enter the name of the new Group Policy in the dialog that appears, then click ok.
Editing a Group Policy Object
Highlight a policy, and select Edit from the Action menu to open the policy for editing.
Samba policies can be found in the Group Policy Management Editor within User or Computer Configuration > Policies > Administrative Templates > Samba. For Samba Domain Controllers, the Password and Kerberos settings are also applied, which are found in Computer Configuration > Policies > OS Settings > Security Settings > Account Policy.
Policies
Password and Kerberos Policies
Password and Kerberos policies, found in Computer Configuration > Policies > OS Settings > Security Settings > Account Policy, are only applicable to Samba Domain Controllers.
The following password policies are applicable:
- Minimum password age
- Maximum password age
- Minimum password length
- Password must meet complexity requirements
And Kerberos policies:
- Maximum ticket age (Maximum lifetime for user ticket)
- Maximum service age (Maximum lifetime for service ticket)
- Maximum renew age (Maximum lifetime for user ticket renewal)
Script Policies
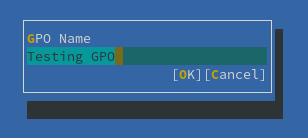
Script policies create cron jobs on client machines which execute the specified commands. Script policies are found in Computer Configuration > Policies > Administrative Templates > Samba > Unix Settings > Scripts.
To add a script policy, open the policy, enable it, and click Show. In the dialog that appears, add the command to execute on the client. Click OK, then Apply to save the policy.
Script policies are applied as cron jobs on the winbind client.
linux-h7xz:~ # /usr/sbin/samba-gpupdate --force linux-h7xz:~ # cat /etc/cron.daily/tmp6l0m809i #!/bin/sh whoami > /daily.log
Sudoers Policies
Sudoers policies add sudo rules to client machines. Sudoers policies are found in Computer Configuration > Policies > Administrative Templates > Samba > Unix Settings > Sudo Rights.
To add a sudo policy, open the policy, enable it, and click Show. In the dialog that appears, add the sudo rules to the list. Click OK, then Apply to save the policy.
linux-h7xz:~ # /usr/sbin/samba-gpupdate --force linux-h7xz:~ # cat /etc/sudoers.d/gp_eockoryg ### autogenerated by samba # # This file is generated by the gp_sudoers_ext Group Policy # Client Side Extension. To modify the contents of this file, # modify the appropriate Group Policy objects which apply # to this machine. DO NOT MODIFY THIS FILE DIRECTLY. # tux ALL=(ALL) NOPASSWD: ALL