DNS Administration: Difference between revisions
No edit summary |
No edit summary |
||
| Line 139: | Line 139: | ||
: [[Image:DNS_Delete_Zone.png]] |
: [[Image:DNS_Delete_Zone.png]] |
||
= Administering DNS on Linux/Unix = |
= Administering DNS on Linux/Unix with samba-tool = |
||
== Adding new records == |
== Adding new records == |
||
| Line 178: | Line 178: | ||
* Example: Changing a SOA Resource Record |
* Example: Changing a SOA Resource Record |
||
: The data part of the SOA record consists of 7 elements in the following order: |
: The data part of the SOA record consists of 7 space (' ') separated elements in the following order: |
||
: ''nameserver, email, serial, refresh, retry, expire, minimum-ttl'' |
: ''nameserver, email, serial, refresh, retry, expire, minimum-ttl'' |
||
: |
: |
||
Revision as of 11:52, 6 August 2019
Introduction
If you're running Samba as Active Directory Domain Controller, you also have to administer a DNS server.
You will already find general information on the internal DNS and the BIND DLZ module and documentation about Bind as DNS Backend in the Wiki.
General
By default, Samba creates the following two forward zones during provisioning/upgrading (of course with your own domain name):
- samdom.example.com: Zone for your domain.
- _msdcs.samdom.example.com: This is the ForestDNSZone, that contains several service records for the entire directory.
Features
The Samba internal DNS is a new implementation. Although BIND is a grown up DNS and long in production on millions of servers, the Samba BIND DLZ module is still new. That's why both backends don't yet cover all the features that you can setup with the Microsoft DNS tools. If you discover problems or missing features, please open a bug report/feature request at https://bugzilla.samba.org/.
Even though the internal DNS and the BIND DLZ modules are new, they both support all basic requirements for Active Directory and more.
Known/issues missing features
- Managing zone transfers is not implemented yet. Bug report #9951:DNS MMC: Enabling DNS zone transfers in MMC fails
- Different zone transfer settings on internal DNS (denied) and BIND DLZ (allowed). Bug report #9634: Samba Bind DLZ module allows zone transfers for everyone
Importance of DNS for Active Directory
A working Active Directory is heavily based on a working DNS. It's not just for resolving IP addresses into names and vice versa. Clients find their Domain Controller/s and other important AD services by DNS queries, this means that your clients must use your Domain Controller/s as their nameservers. Do not use anything else between your clients and Domain Controller/s.
Administering DNS on Windows
To administer DNS from a Windows client, you have to install the DNS MMC Snap-In. See Installing RSAT on Windows for AD Management for more details.
If you use the internal DNS server, there are the following known problems:
- Scavenging is not implemented yet. The error message "This function is not supported on this system" is returned.
- Conditional forwarders are not implemented yet. The same error message as above is returned.
- The DNS forwarder can only be changed in the smb.conf, not via the MMC Snap-In.
- Creating static records. When a static record is created it has a timestamp and the option "Delete this record when it becomes stale". In Windows Active Directory, static records have a "static" timestamp and cannot be accidently deleted.
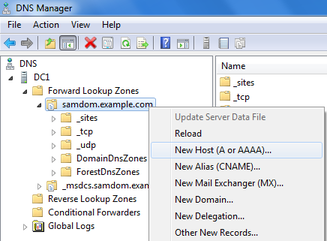
Adding new records
- Navigate to the zone, where you want to to add a new record.
- Right-click to it and choose the kind of record to add.
- Fill the fields and save the new entry.
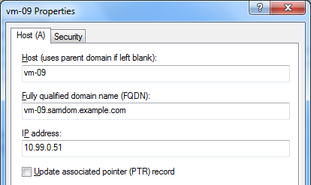
Updating existing records
- Navigate to the zone that contains the record you want to edit.
- Right-click the record and choose „Properties“.
- Edit the entry and save the changes.
Delete a record
- Navigate to the zone that contains the record you want to remove.
- Right-click to the record and choose „Delete“.
Changing zone properties
- Right-click to a zone of which you you want to do changes.
- Choose „Properties“.
Note: Currently both DNS backends don't support all features that can be setup in the dialogues. If you discover problems or missing features, please open a bug report/feature request at https://bugzilla.samba.org/.
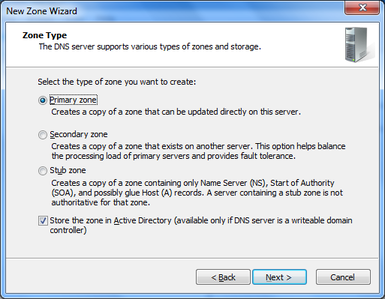
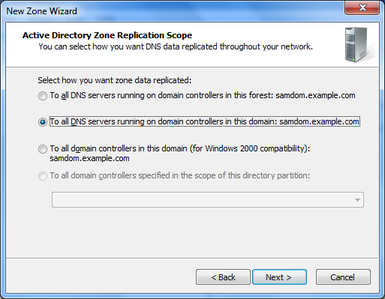
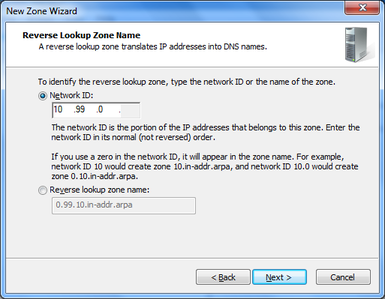
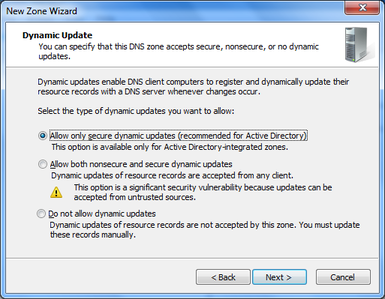
Creating a new zone
As example we'll add a reverse lookup zone.
- Right-click to „Reverse Lookup Zones“ and choose „New Zone“.
- The „New Zone Wizard“ appears.
- Zone Type: Select „Primary zone“ and „Store the zone in Active Directory“.
- Zone Replication Scope: Depends on your needs.
- Reverse Lookup Zone Name: Depends on your needs.
- Dynamic Update: Depends on your needs.
- Finish the wizard.
Your new zone is directly live without restarting Samba or BIND.
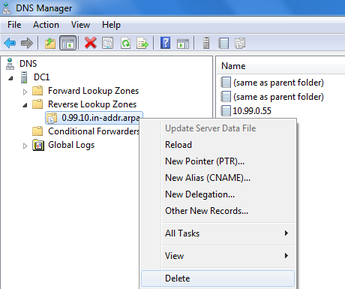
Deleting a zone
- Right-click to a zone and choose „Delete“.
Administering DNS on Linux/Unix with samba-tool
Adding new records
- Example: Adding an A record
# samba-tool dns add <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com demo A 10.99.0.55 Password for [administrator@SAMDOM.EXAMPLE.COM]: Record added successfully
- Example: Adding a PTR record to a reverse zone
# samba-tool dns add <Your-AD-DNS-Server-IP-or-hostname> 0.99.10.in-addr.arpa 55 PTR demo.samdom.example.com Password for [administrator@SAMDOM.EXAMPLE.COM]: Record added successfully
- Example: Adding a SRV record to _tcp.samdom.example.com
# samba-tool dns add <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com _demo._tcp SRV 'demo.samdom.example.com 8080 0 100' Password for [administrator@SAMDOM.EXAMPLE.COM]: Record added successfully
- A note on SRV records: The order of the four parameters in the last field („data“) are 'hostname port priority weight' and have to be between ' '.
- Example: Adding a NS record to samdom.example.com zone
# samba-tool dns add <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com @ NS newdc.sambdom.example.com Password for [administrator@SAMDOM.EXAMPLE.COM]: Record added successfully
Updating existing records
- Example: Changing an A record
# samba-tool dns update <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com demo A 10.99.0.55 10.99.0.66 Password for [administrator@SAMDOM.EXAMPLE.COM]: Record updated succefully
- Example: Changing a SOA Resource Record
- The data part of the SOA record consists of 7 space (' ') separated elements in the following order:
- nameserver, email, serial, refresh, retry, expire, minimum-ttl
- The following example changes the host masters mail address:
# samba-tool dns update <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com @ SOA \ "dc1.samdom.example.com hostmaster.example.com 63 900 600 86400 3600" \ "dc1.samdom.example.com admin.example.com 64 900 600 86400 3600" Password for [administrator@SAMDOM.EXAMPLE.COM]: Record updated successfully
Delete a record
- Example: Deleting an A record
# samba-tool dns delete <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com demo A 10.99.0.55 Password for [administrator@SAMDOM.EXAMPLE.COM]: Record deleted succefully
- Example: Deleting a NS record from samdom.example.com zone
# samba-tool dns delete <Your-AD-DNS-Server-IP-or-hostname> samdom.example.com @ NS olddc.sambdom.example.com Password for [administrator@SAMDOM.EXAMPLE.COM]: Record deleted successfully
Creating a new zone
As example we'll add a reverse lookup zone.
# samba-tool dns zonecreate <Your-AD-DNS-Server-IP-or-hostname> 0.99.10.in-addr.arpa Password for [administrator@SAMDOM.EXAMPLE.COM]: Zone 0.99.10.in-addr.arpa created successfully
Your new zone is directly live without restarting Samba or BIND.
Deleting a zone
- Example: Deleting a reverse zone:
# samba-tool dns zonedelete <Your-AD-DNS-Server-IP-or-hostname> 0.99.10.in-addr.arpa Password for [administrator@SAMDOM.EXAMPLE.COM]: Zone 0.99.10.in-addr.arpa delete successfully
Listing existing zones
- Example: listing secondary zones
# samba-tool dns zonelist <Your-AD-DNS-Server-IP-or-hostname> --secondary -U administrator
Listing zone information
- Example: showing information about a zone
# samba-tool dns zoneinfo <Your-AD-DNS-Server-IP-or-hostname> <zone-name> -U administrator
Listing zone records
- Example: listing records from a zone
# samba-tool dns query <Your-AD-DNS-Server-IP-or-hostname> <zone-name> @ ALL -U administrator
Configuring clients to use your AD DNS server
Testing your DNS Server
See Testing the DNS Name Resolution.